Behavior-based Protection
Behavior based detection is part of Kaspersky Lab’s multi-layered, next generation approach to protection. It’s one of the most efficient ways to protect against advanced threats like fileless malware, ransomware and zero-day malware.
The following protection capabilities make up Kaspersky Lab's new Threat Behavior Engine:- Behavior Detection
- Exploit Prevention (EP)
- Remediation Engine
- Anti-locker
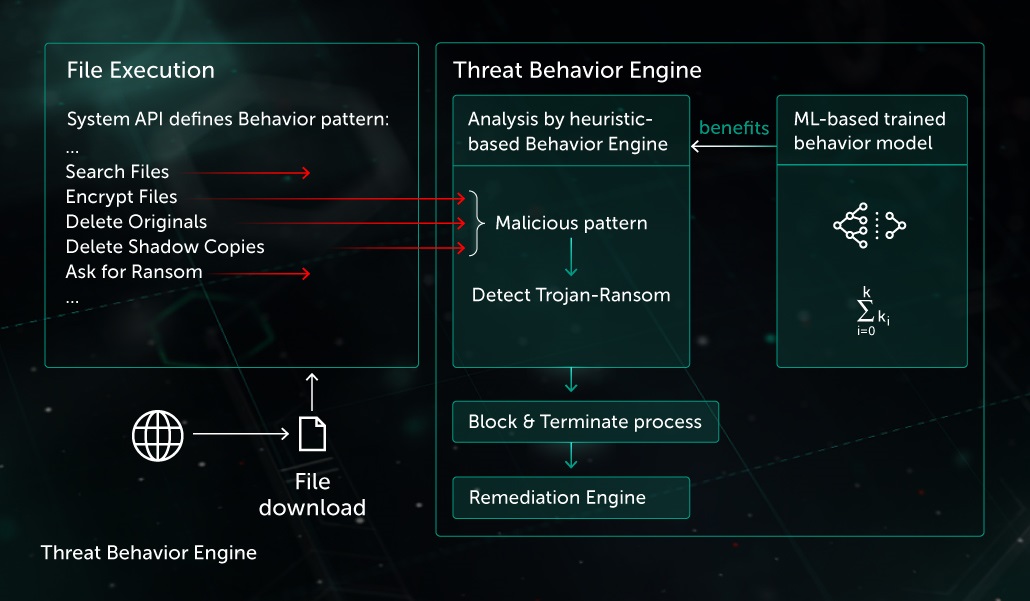
In real life, threat actors obfuscate malicious code to bypass static detection technologies in and emulation by security products. For example, just-created ransomware code is often packed by custom-made packer with anti-emulation feature. Before execution, any attempt to scan the well-done sample by On Demand Scan or On Access Scan will return no success in detection, so the task of the threat actor is carried out.
But when it comes to execution stage, the Threat Behavior Engine analyzes the actual process activity in real time and reveals its malicious nature. All that is needed then is to flag the alarm, terminate the process and perform rollback of the changes.
In the mentioned example with packed ransomware, the sample could try to
- Find important files on target system
- Encrypt important files
- Delete original files
- Delete shadow copies
Such information is enough for detection and does not depend on packer or anti-emulation techniques used. Running Threat Behavior Engine, armored by both behavior heuristics and ML-based models, the product becomes non-sensitive to static avoidance techniques and even sample behavior modifications.
Making behavior based judgments, it is important to produce detection of malicious activity as soon as possible, which in combination with proper Remediation Engine allows to prevent any final user’s data loss. Remediation Engine protects different objects, like files, registry keys, tasks, etc.
Returning to the sample above, let’s assume that before actual malicious activity, the ransomware added itself to autorun (for example, through registry). After detection, Remediation Engine should analyze the behavioral stream and not just restore user’s data but also delete the created registry key.
Among other advantages, in some cases behavior based detection technology becomes the only means to detect and protect from a threat such as fileless malware. For example, while surfing the internet, a user is targeted by a drive-by based attack. After exploitation, malicious code is executed in the context of web browser. The main goal of the malicious code is to use registry or WMI subscriptions for persistence, and this ends up with no single object for static scan. Nevertheless, the Behaviour Detection component analyses the web browser’s thread behaviour, flags the detect and blocks the malicious activity.
Behavioral Engine component benefits from ML-based models on the endpoint to detect previously unknown malicious patterns in addition to behaviour heuristic records. Collected from different sources, system events are delivered to the ML model. After processing, ML model produces a verdict if the analysed pattern is malicious. Even in the case of a non malicious verdict, the result from the ML model is then used by Behaviour heuristics, which in turn could also flag the detect.
Behavior Detection component implements a Memory Protection mechanism. It guards system critical process like lsass.exe and allows to prevent user credential leakage with the help of mimikatz like malware.


