Kaspersky recognized as a Leader in Frost Radar: Cyber Threat Intelligence, 2024
Global Cyber Threat Insights
at Your Fingertips
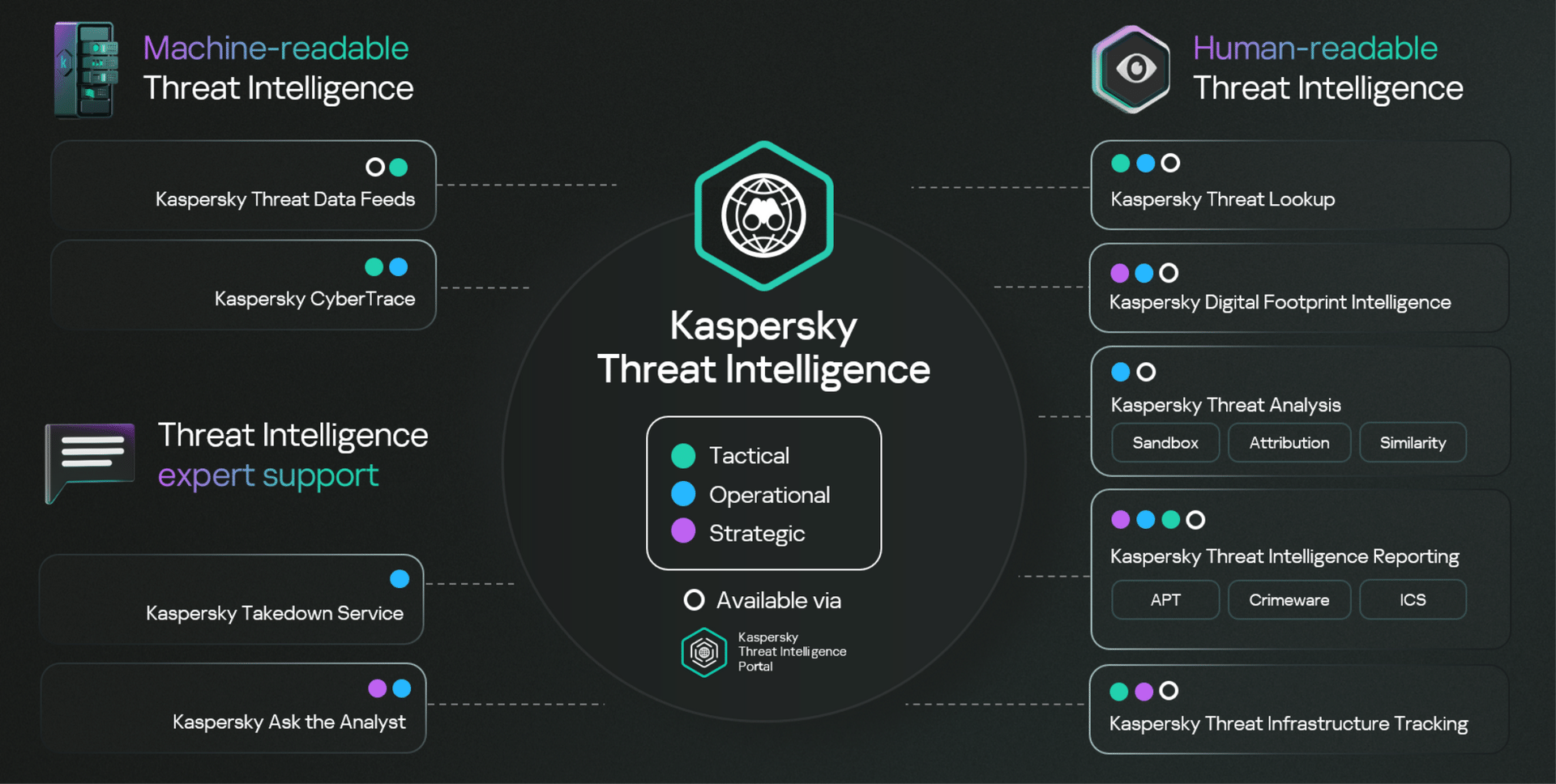
Key Elements of Kaspersky Threat Intelligence
By combining diverse data sources and expert research, Kaspersky Threat Intelligence Portal offers actionable insights. Access tactical, operational, and strategic intelligence to stay secure in a dynamic threat landscape.
Discover your threat landscape with the Kaspersky Threat Intelligence Portal
Machine-readable
Threat Intelligence
30+ threat data feeds focusing on different needs of IT and OT and supported by threat intelligence platform
Kaspersky Threat Data Feeds
Enhance the detection capabilities of your existing security controls
Human-readable Threat Intelligence
Kaspersky Threat Intelligence Portal - bringing together all the knowledge we have acquired about cyberthreats into a single access point.
Kaspersky APT Intelligence Reporting
Get insights into APT actors
targeting your industry and
region
targeting your industry and
region
Kaspersky Crimeware Intelligence Reporting
Understand and successfully combat crimeware threats
Kaspersky ICS Intelligence Reporting
Understand cyberthreats affecting industrial organizations
Kaspersky Threat
Lookup
Lookup
Effectively investigate threats by revealing their various relationships
Kaspersky Digital Footprint Intelligence
Explore the risks associated with your company’s digital footprint
Kaspersky Threat
Analysis
Analysis
Detect unknown threats with a flexible set of threat analysis tools
Kaspersky Threat Infrastructure Tracking
Track threat infrastructures to mitigate ongoing and future attacks
Threat Intelligence
Expert Support
Comprehensive guidance from the most experienced professionals
Kaspersky Takedown Service
Request fully managed takedowns of malicious and phishing domains
Why Kaspersky Threat Intelligence
Kaspersky Threat Intelligence Portal Free Version
Get free access to trusted threat intelligence
Out-of-the-box integarations
Integrate your security tools with Kaspersky Threat Intelligence with out-of-the-box connectors or our robust RESTful API
CASE STUDIES
Explore Kaspersky Threat Intelligence at work
Recognition
Materials
Connect with our local partner
If you'd like to find out how to protect your business from complex cybersecurity attacks, with the most tested, most awarded product on the market, please contact your local partner or request a demo.