Anti-Rootkit and Remediation Technology
Rootkit - A malicious program that applies different techniques of concealing malicious code and activities from detection and counteracts against attempted remediation by antivirus. Anti-Rootkit technology, part of Kaspersky’s multi-layered, next generation protection, detects active infection by these rootkit programs and remediates systems from this type of infection.
In most cases, a rootkit includes a driver (or chain of drivers), functions in kernel mode, and performs some or all the following functionality:
- Concealing of files on storage (HDD), Windows registry keys and values, processes in system, loaded modules, memory regions (in case of fileless malware), network activities, disk sectors, other objects and artefacts
- Counteractions against modification and\or elimination of the rootkit by antivirus in case of detection, including restoring changed ones
- Provision of access to OS kernel for malicious code\applications (for the sake of antivirus processes termination), injection of malicious code into legitimate processes, interception of network traffic (sniffing), interception of presses keys (keylogging), etc
Malware writers are interested in functioning their malicious code during long periods of time on a targeted host, even in case of running antivirus software. For this purpose they need to operate different techniques to hamper detection and remediation of the active infection. They may use both documented and undocumented methods of Operation System. RootKits are known to use different approaches of interception in user mode and in kernel mode, manipulations with objects (DKOM), techniques of bypassing filter-drivers and callback functions, etc. To support persistency on the victim system, RootKits need to start executing on early stages of Operation System boot, so they infect boot sectors, as Primary Boot Record (PBR) and Volume Boot Record (VBR). RootKit with such functionality is called BootKit.
Kaspersky’s Anti-rootkit technologies
- Search for active infection in system memory of Operation System
- Scan all the possible locations used for AutoRun
- Remediate in case of active infection detection, recovery on early stage of Operation System booting
- Neutralize active infections during product installation onto the infected system
This complicated multi-module protection technology implements two approaches for detection and neutralization of active infection: exact and generic. Kaspersky products utilize both of these approaches.
Exact approach: procedures of detection and neutralization are targeted against particular rootkit techniques, like presence concealing or counteractions to remediation by antivirus. This approach allows protection against a rootkit within a short period of time to cover current outbreaks, saving more time to develop a more generic approach.
Generic approach: Anti-RootKit scans active processes, system modules, memory, AutoRun objects, and provides access to the malware code to other antivirus components such as an emulator, AV engine, static heuristics, behavior-based heuristics empowered by ML model, etc. In case of triggering by any of the listed component, the anti-rootkit disinfects the system.
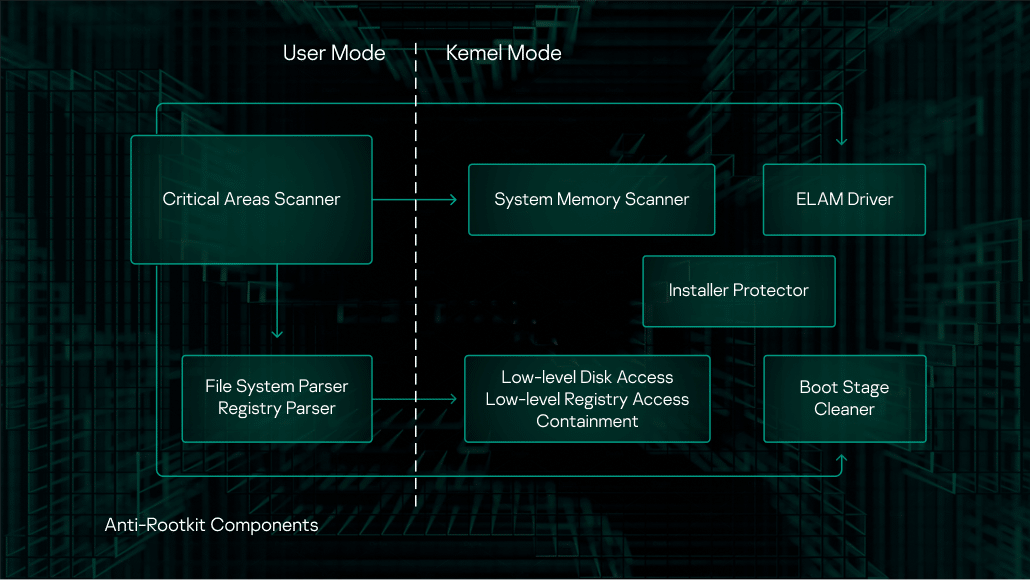
Anti-rootkit components
- Installer Protector: Counteracts against active infection during security product installation onto the victim system
- Low-level Disk Access, Low-level Registry Access, Containment: provide low-level access to hard drive and Windows registry, bypassing different methods of access interception. Contains implementation of techniques for active infection containment for a period of remediation
- Boot Stage Cleaner: Remediates early stage of Operation System booting
- System Memory Scanner: A module to search for and remediate rootkits in system memory
- Filesystem Parser, Registry Parser: Parses numerous formats of File System and Window Registry
- Critical Areas Scanner: Module to scans and remediate AutoRun objects, benefits from the modules described above.
One form of threat that’s been growing over recent years is that of rootkits hiding in firmware. This type of malware is very dangerous, as it starts executing in the early stages of OS booting, so the malicious code can stay in the system even after the disk is formatted and the OS is rebooted. The first UEFI rootkits were discovered in 2015. Over subsequent years, a number of successful APT attacks using this sort of rootkits have been detected.
To counter this threat, our set of Anti-Rootkit technologies includes a Firmware Scanner, which analyzes the contents of the ROM BIOS when the Critical Areas Scanner is running. This technology can work for systems booted in UEFI mode or in legacy mode (BIOS).
The Firmware Scanner operates as follows:
- The contents of the ROM BIOS is dumped by a special driver.
- The scanner inspects the dump using the heuristics specific to rootkit detection.
- If malicious code is detected, the user is notified by an alert that shows the malware’s location (System Memory) and the mode in which the system was booted ('MEM:Rootkit.Multi.EFI.a' verdict for UEFI mode, 'MEM:Rootkit.Multi.BIOS.a' for legacy mode).
- As rewriting the ROM BIOS is a potentially hazardous operation and is platform-dependent, automatic remediation is not performed for this type of infection. If a rootkit is detected, you should contact our Support Service for instructions on how to manually rewrite the ROM BIOS. In the very worst case, it’s possible that you’ll need to replace the motherboard.
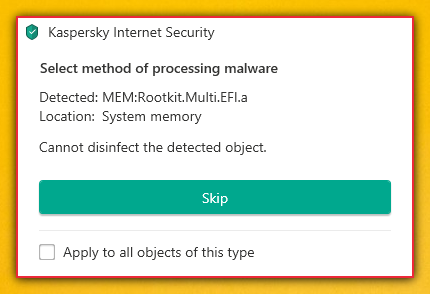
A UEFI rootkit detection alert from Kaspersky Internet Security
Kaspersky's Firmware Scanner detects all known UEFI rootkits, including Hacking Team (VectorEDK), Lojax (DoubleAgent) and Finfish. The dedicated heuristics are regularly updated, based on studies of new rootkits discovered by Kaspersky's and other vendors' experts. The Firmware Scanner is used in all our major products (Kaspersky Anti-Virus, Kaspersky Internet Security, Kaspersky Total Security, Kaspersky Endpoint Security for Business, etc).




