
Every time you open an account, make a purchase, or download an app, you share pieces of information about yourself. Some of that data may seem harmless. Other details can be used to verify your identity, access your accounts, or commit fraud if they fall into the wrong hands.
Understanding which information puts you at risk and how it can be misused is the first step toward protecting your digital identity. When you know what to watch for, it becomes easier to reduce your exposure and stay in control of your personal data.
What you need to know:
- PII includes obvious details like your name and Social Security number, but also indirect data like location history or device identifiers.
- Some PII identifies you directly, while other data becomes identifying when linked together.
- Exposed PII can lead to identity theft, fraud, phishing, and account takeover.
- Businesses are expected to handle PII carefully under privacy and data protection laws.
- You can reduce risk by limiting what you share and securing accounts. People also monitor for misuse.
What is personally identifiable information (PII)?
Personally identifiable information (PII) is any information that can be used to identify a person directly or indirectly.
The data may be particular to one individual, such as a social security number, or they can be “quasi-identifiers,” different bits of general data, like place and date of birth, which can be combined to identify an individual.
PII can range from names and ID numbers to email addresses, IP addresses, and location data. It is important to understand the risks of exposure and how PII should be protected or removed from the internet.
What are examples of personally identifiable information?
PII includes all information that can identify you. Some data points may seem harmless on their own. But together, they can narrow down someone’s identity quickly. Kaspersky’s research shows that personally identifiable information is among the most commonly exposed data in breaches, appearing in about 43% of cases, which highlights how often this type of data is at risk.
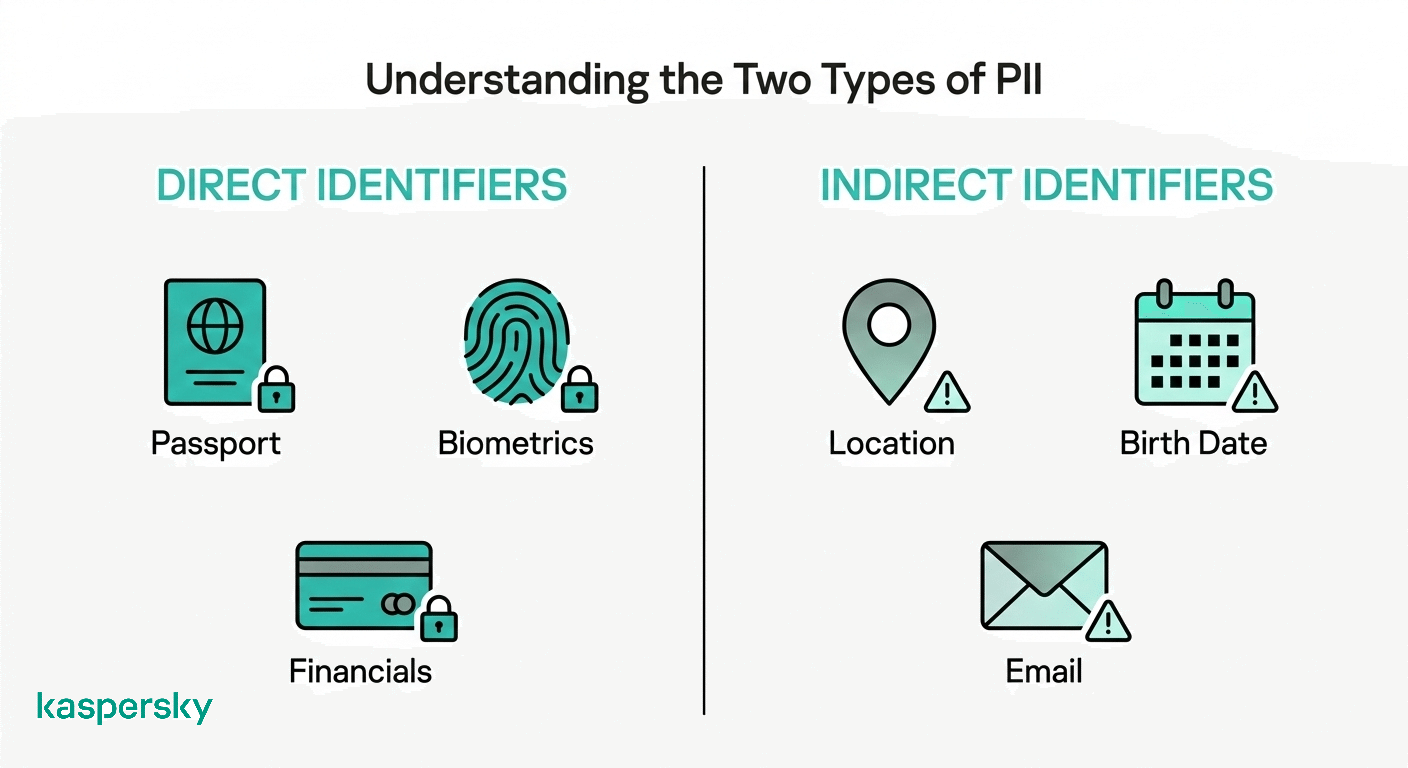
Direct identifiers
Direct identifiers clearly point to a specific person without needing extra context. These include:
- Credit card details
- Social security numbers
- Driver’s license numbers
- Passport numbers and details
- Bank account information
- Medical records
- Biometrics data and identifiers such as fingerprints and facial recognition data
If exposed, this type of information can quickly lead to identity theft or financial fraud.
Indirect (quasi) identifiers
Indirect or quasi-identifiers may be less obvious. They include:
- ZIP codes
- Race
- Religions
- Gender
- Dates of birth
- Places of birth
- Full name
- Employment information and history
- Education details
- Email address or postal address
- Phone numbers
- Mother’s maiden name
- Biographical information – such as details of parents, siblings, partners, and children
- IP addresses and device-related identifiers collected online
While these details may appear routine, linking them together can reveal more than expected and increase risk.
What is PII in healthcare?
PII is often referred to as protected health information (PHI) in a healthcare setting. PHI includes medical or health-related data that can be linked to a specific person under laws such as HIPAA in the United States.
PHI usually combines basic PII (name or date of birth) with medical details like diagnoses, treatment records, prescriptions, or insurance information. Connecting these pieces can provide a lot of information about an individual.
For patients, this potentially affects online portals, insurance claims, appointment systems, and billing records. Because health data is personal and long-lasting, protecting PHI is critical to prevent identity theft or misuse of medical records.
What is the difference between sensitive and non-sensitive PII?
The difference comes down to impact. Sensitivity depends on how much harm could happen if the information is exposed.
Sensitive PII can lead directly to identity theft or financial fraud. Non-sensitive PII may seem harmless on its own and is reliant on other data to provide a precise identity.
Passport or driver’s license numbers are considered sensitive. They can be harmful on their own, if exposed. Your employment or education history are non-sensitive examples of PII.
Even “non-sensitive” data can become dangerous when linked together. For example, a name plus date of birth and location can narrow down identity quickly. Alternatively, an IP address alone may not clearly name a person. But when linked to login records and device fingerprints it can point to a specific user.
Why do criminals target personally identifiable information?
Criminals target PII because it can be used for many forms of fraud and account takeover.
Stolen information may be used directly to access financial accounts or reset passwords. It can also be bundled and sold or traded on the dark web to others who carry out scams. PII is very valuable to scammers.
For victims, the result can include financial losses and long-term issues with things like damaged credit. Recovering accounts and identity can be a long and difficult process.
How does PII get stolen?
PII is usually stolen through everyday channels rather than complex hacks.
The most common route is phishing or smishing. A fake email or text asks you to click a link or confirm details, but is actually a way of stealing your details to use or sell on. Social engineering scams work the same way by using pressure and perceived urgency to get you to share information directly.
Data breaches and malware attacks are another major source. When companies are hacked, their customers’ important account details can be exposed in bulk. This can even happen to globally-recognized companies. For example, a recent error in the coding of a PayPal loan app left some customers’ data exposed for many months.
PII can also be exposed through lost devices or unsafe public Wi-Fi. An unsecure connection can give attackers access to stored accounts and saved credentials.
Red flags to watch for:
- Messages asking for urgent confirmation of account or payment details
- Requests to share one-time codes or passwords
- Unsecured public Wi-Fi networks without passwords
- Unexpected charges or login notifications
You should also pay attention to news stories (from reputable sources) about data breaches involving services you use.
Protect your Sensitive Data
Kaspersky Premium offers various tools designed to protect your PII, including tools to protect sensitive data by encrypting files and using secure passwords and a secure VPN to keep your connection private.
Try Premium for FreeWhat laws protect personally identifiable information?
Several laws worldwide are designed to protect personal data and give individuals certain rights over their information. Countries make their own laws on this data, but may use the same frameworks.
- GDPR (General Data Protection Regulation) gives people in the EU the right to access, correct, and request deletion of their personal data.
- CCPA/CPRA (California Consumer Privacy Act and California Privacy Rights Act) allow California residents to know what data is collected about them and request that it be deleted or not sold.
- The Privacy Act of 1974 regulates how U.S. federal agencies collect and use personal information.
- HIPAA (Health Insurance Portability and Accountability Act) protects health-related information handled by medical providers and insurers.
- PCI DSS (Payment Card Industry Data Security Standard) sets security requirements for companies handling credit card data.
- PDPA (Singapore Personal Data Protection Act) sets rules for data collection, use, and disclosure in Singapore.
- POPIA (South Africa’s Protection of Personal Information Act) establishes conditions for lawful processing of personal data.
- PDPL (Saudi Arabia’s Personal Data Protection Law) came into full effect in 2024. It provides data protection rights and obligations within the Kingdom of Saudi Arabia.
How can you protect your personally identifiable information?
Protecting your PII means reducing how much of it is exposed, plus making it harder for attackers to use what they find. There are multiple simple methods you can implement to tackle account takeover and identity misuse.
Strengthen account security
Use strong and unique passwords for every account and store them in a password manager for extra security. Turn on multi-factor authentication wherever possible to add another level of security.
Be sure to check for leaked credentials through breach alerts and change exposed passwords quickly.
Limit what you share online
Review your social media privacy settings and remove unnecessary public details – think about what you really want to be publicly available. Avoid posting your full birthday or home address or real-time location.
Be cautious with anything that encourages you to share information. This may include quizzes or posts that resemble security questions. These can be scams, made specifically to collect your information.
Secure devices and connections
Use security settings and technologies to ensure that you are as protected as possible. It is a good idea to keep devices updated and use screen locks and built-in encryption.
We also recommend that you use a VPN on public Wi-Fi to reduce interception risks. Public connections carry risks.
Reduce tracking and data collection
Tracking is another threat to your information. Adjust privacy settings and limit third-party cookies to restrict how your internet connection and device details are tracked. Review app permissions and disable unnecessary tracking or surveillance features that may compromise your data.
Restrict things like location access for apps that don’t need it to lower the chance that your data is being tracked and used to identify you.
Experts also recommend optimizing browser privacy settings – disabling third-party cookies, preventing website tracking, limiting ads – regularly clearing browsing histories (including cookies and caches), and deleting unnecessary extensions.
Monitor for identity misuse
It often pays to be observant and set up alerts for your accounts. Enable transaction alerts on bank and credit card accounts so you can see when money is spent. It is a good idea to regularly check credit reports for unfamiliar activity. In the US, the “big three” credit unions, Experian, TransUnion and Equifax, provide reports for free.
Identity monitoring or scrubbing services can provide additional visibility if you want ongoing oversight of your information.
How can you remove your personal information from the internet?
Removing PII online is possible, but it may be a process rather than a one-time fix. The goal is to reduce exposure in the places that matter most.
The top tips include:
- Delete or deactivate unused accounts. Old forum sites and apps often store personal details you no longer need online. Social media sites may store a lot of information. Remove your data from these where possible.
- Tighten social media privacy settings. Limit who can see your profile and what information is made public. Remove personal details like phone numbers or full birth dates.
- Request removals. Ask website owners to delete outdated or unnecessary information about you. You can also request removal of certain personal details from search engine results where applicable.
- Opt out of data brokers. Many companies collect and resell personal data. You can submit opt-out requests directly or use a reputable removal service if your information is widely listed.
- Revisit your PII online. Personal information can resurface over time. It’s crucial to review and clean up periodically rather than treating removal as a one-and-done task.
What should you do if your PII is exposed?
If your PII is exposed, try to avoid panicking. Prioritize steps that limit further access and reduce financial damage.
- Secure your accounts first. Change passwords, especially for email. Enable multi-factor authentication (MFA) where possible.
- Check for unauthorized activity. Review account logins and recent transactions plus whether security settings have been changed.
- Contact your bank or card provider. Report suspicious charges and ask about additional protections.
- Freeze your credit if needed. A credit freeze can prevent new accounts from being opened in your name until you secure your data.
- Monitor statements and alerts. Keep an eye on financial and account activity for ongoing misuse.
- Report identity theft. In the UK, for example, it is easy to file a report with the Prevent Fraud arm of the police or call them on 0300 123 2040.
Be cautious of follow-up scams. Attackers sometimes pose as “recovery” services or security teams after a breach. Always verify independently before sharing more information.
Related Articles:
- What are the risks associated with Data Leakage?
- How can you best protect privacy from online threats?
- What are the key causes of a Data Breach?
- How does the internet impact individual privacy and data protection?
Related Products:
FAQ
Is an IP address considered PII?
On its own, an IP address may not directly identify a person, but when linked to other data or account records, it can become personally identifiable.
What is the difference between PII and personal data?
PII is a term commonly used to describe identifiable information. “Personal data” is a broader term used in regulations like GDPR and may include additional types of data.
What is the difference between PII and PHI?
PII covers general identifying information. PHI refers specifically to health-related information linked to a person and is protected under laws like HIPAA.
Can you completely remove your PII from the internet?
Full removal is rarely possible. Ongoing monitoring and periodic clean-up are often more realistic approaches.

