Malicious objects of all types were detected and blocked on 34 percent of Industrial Control System (ICS) computers in the first half of 2023, according to the ICS CERT landscape report by Kaspersky. The second quarter of 2023 saw the highest quarterly level of threats globally since 2019, with 26.8 percent of ICS computers affected. One of the findings highlights a trend showing high-income countries are experiencing rise in cyber threat detections.
In the first half of 2023, Kaspersky's security solutions blocked 11,727 different malware families in industrial systems. Out of all categories, only one showed growth in H1 2023: denylisted internet resources (11.3%). This marks the second consecutive half-year of increased threat activity in this category. Denylisted internet resources were the leading threat category until 2022, when they were overtaken by malicious scripts and phishing pages. These elements remain the most prevalent threats (12.7%), although their percentages have been increasingly converging.
In H1 2023, traditionally safer regions experienced unexpected shifts. Australia and New Zealand, the United States and Canada, Western Europe, and Northern Europe, typically characterized by lower threat levels, witnessed increases in attacked ICS computers proportions during this time period.
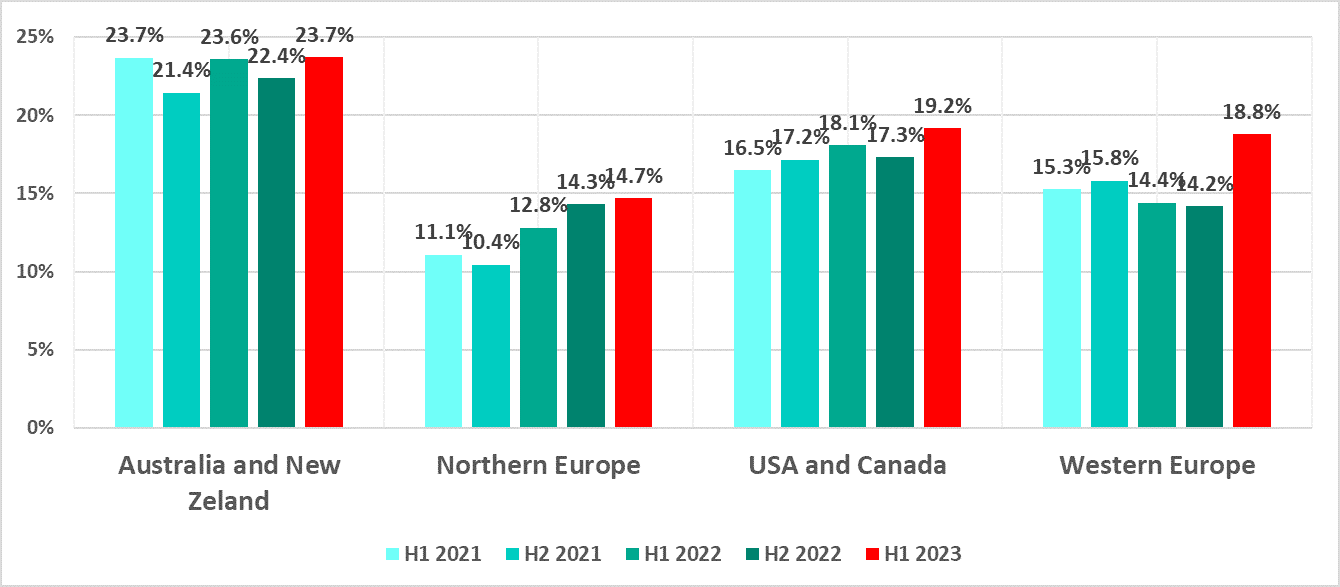
Percentage of ICS computers on which malicious objects were blocked in selected regions
Despite these increases, it's crucial to emphasize that these regions still maintain relatively low threat percentages when compared to others. The rise in threats can be primarily attributed to the blocking of denylisted internet resources and malicious scripts, commonly delivered via the internet and email. Additionally, spyware detection showed considerable growth in these areas.
Regarding global figures, threat percentages varied significantly by region, with Africa experiencing the highest incidence at 40.3 percent, while Northern Europe reported the lowest at 14.7 percent. Notably, Ethiopia faced the highest threat percentage by country at 53.3 percent, while Luxembourg reported the lowest, at 7.4 percent.
Building automation remained the industry most exposed to cyber threats, accounting for 38.5 percent of computers attacked. However, the energy, oil and gas industries experienced opposite trends since 2021. Energy saw an increase of 36 percent in threats, while the oil and gas sector experienced a decrease, accounting for 30.8 percent.
In addition, engineering, ICS integration, manufacture, and energy sectors showed an overall increase in the percentage of ICS computers on which malicious objects were blocked in H1 2023.
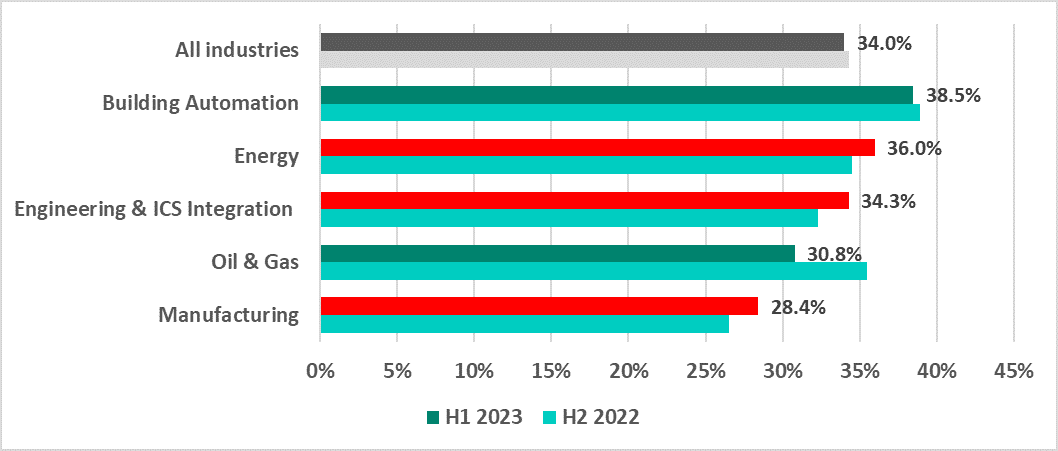
Percentage of ICS computers on which malicious objects were blocked in selected industries
“For industrial enterprises cybersecurity is now about safeguarding investments and ensuring the resilience of key assets. The findings from our analysis of attacks on the industrial sector reveal crucial insights into evolving threat landscapes in various industries. By understanding these risks, organizations can make informed decisions, allocate resources wisely, and efficiently fortify their defenses. In doing so, they not only protect their bottom line but also contribute to a safer and more secure digital ecosystem for all,” comments Evgeny Goncharov, head of Kaspersky ICS CERT.
Read more about the ICS threat landscape in H1 2023 on the Kaspersky ICS CERT website.
To keep your OT computers protected from various threats, Kaspersky experts recommend:
· Conducting regular security assessments of OT systems to identify and eliminate possible cyber security issues.
· Establishing continuous vulnerability assessment and triage as a basement for effective vulnerability management process. Dedicated solutions like Kaspersky Industrial CyberSecurity may become an efficient assistant and a source of unique actionable information, not fully available in public.
· Performing timely updates for the key components of the enterprise’s OT network; applying security fixes and patches or implementing compensating measures as soon as it is technically possible is crucial for preventing a major incident that might cost millions due to the interruption of the production process.
· Using EDR solutions such as Kaspersky Endpoint Detection and Response for timely detection of sophisticated threats, investigation, and effective remediation of incidents.
· Improving the response to new and advanced malicious techniques by building and strengthening your teams’ incident prevention, detection, and response skills. Dedicated OT security trainings for IT security teams and OT personnel is one of the key measures helping to achieve this.
