Cybercriminals have been exploiting the increased popularity in video games during lockdown to launch attacks.
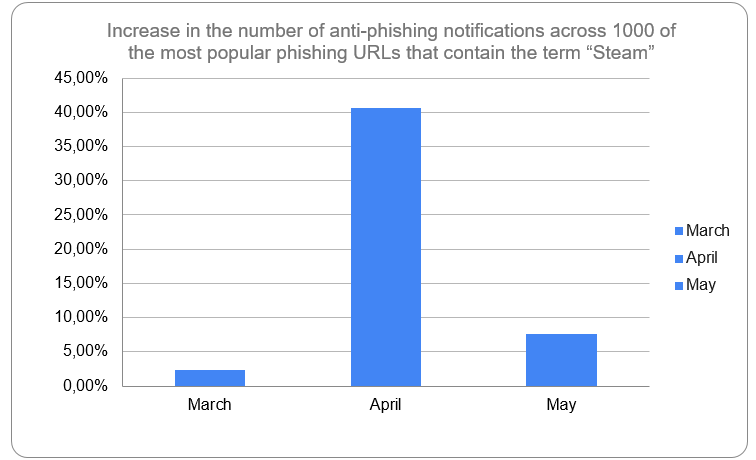
Cybercriminals have been exploiting the increased popularity in video games during lockdown to launch attacks. In April, the daily number of blocked attempts to direct Kaspersky users to malicious sites that exploit the gaming theme increased by 54% when compared to January 2020. In addition, for April, the number of blocked attempts to direct users to phishing pages for one of the most popular gaming platforms increased by 40% compared to February 2020.
This spring, millions of people around the world were relegated to staying inside, as many countries enforced some form of lockdown measures or movement restrictions. With more people at home and greater amounts of free time on their hands, many turned to available online entertainment, including video games. Beginning in March, the overall number of Steam users (the most popular online gaming platform, community, and store) increased significantly, with the platform reaching an all-time record for both active users and concurrent users actively playing games by March 30.
Upon noticing this trend, Kaspersky researchers decided to look deeper into the threat landscape of video games during the lockdown period. What they found—not surprisingly—was that cybercriminals have been exploiting the increased interest in video games to launch various attacks.
According to data from Kaspersky Security Network, there was a significant increase in the daily number of attempts to direct users to malicious sites that exploited the gaming theme: a 54% increase in April when compared to January. Often times, users are lured by promises such as free versions of popular games, updates and extensions, or cheats. However, if users click on these links, a wide variety of malicious programs can be downloaded, from password stealing malware to ransomware and miners, software that secretly mines cryptocurrency from the victim’s computer.
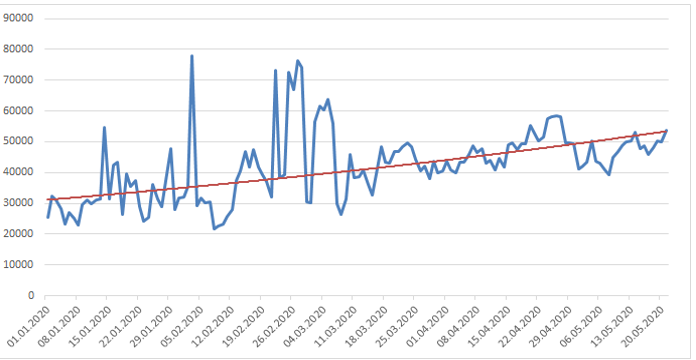
Daily numbers of web attacks that use the theme of online games as a lure, January-May 2020
The game most often used by criminals was Minecraft, one of the most popular games ever made. Its name was used in more than 130,000 web attacks. The other most popular games used in attacks were Counter Strike: Global Offensive and The Witcher 3.
What’s more, according to statistics from Kaspersky’s Anti-Phishing System, compared with February, the number of blocked redirects to phishing pages that contained the word “Steam” increased by 40% in April.
“Many of these video game-related attacks are not particularly sophisticated; there is a large user component to their success. The past few months have shown that users are highly susceptible to falling for phishing attacks or clicking on malicious links when it comes to games—whether they’re looking to find pirated versions or eager for a cheat that will help them win,” comments Maria Namestnikova, security expert at Kaspersky.
“Now that many players started using the same machines that they use to enter corporate networks for games, their cautiousness should be doubled: risky actions make not only personal data or money vulnerable but also corporate resources. When working from home, if possible, try to avoid mixing your personal computer with the one you use for accessing corporate network,” adds Yury Namestnikov, security expert at Kaspersky.
Read more about video game-related cybercrime on Securelist.
To stay safe from attacks while playing video games, Kaspersky experts recommend:
- Use strong passwords and two-factor authentication (2FA) where possible to protect your video-gaming accounts
- Be wary of any cheats and pirated copies of video-games, since it’s one of the favorite lures used by cybercriminals
- Use a reliable security solution like Kaspersky Security Cloud that identifies malicious downloads, blocks phishing sites, and prevents redirects to malicious pages
- During the game, don’t switch off your security solution, but turn on gaming mode, which consumes less resources
About Kaspersky
Kaspersky is a global cybersecurity company founded in 1997. Kaspersky’s deep threat intelligence and security expertise is constantly transforming into innovative security solutions and services to protect businesses, critical infrastructure, governments and consumers around the globe. The company’s comprehensive security portfolio includes leading endpoint protection and a number of specialized security solutions and services to fight sophisticated and evolving digital threats. Over 400 million users are protected by Kaspersky technologies and we help 250,000 corporate clients protect what matters most to them. Learn more at www.kaspersky.com.
