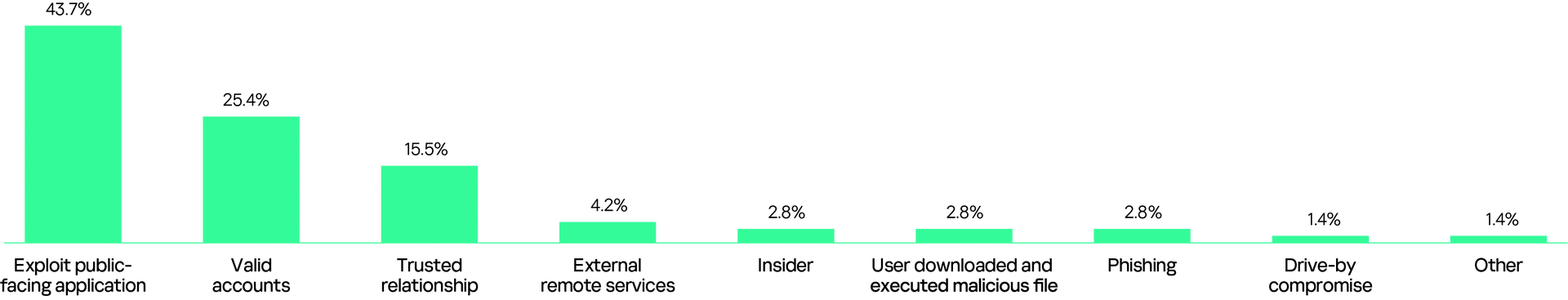
Although the main initial vectors in 2025 remain similar to 2024, their combined share has grown to over 80%. Public-facing applications account for 43.7%, while trusted relationships have increased from 12.7% to 15.5%. Valid accounts make up 25.4%. These insights are from the recent Global Report by Kaspersky Security Services.
The ‘Anatomy of a Cyber World’ is an in-depth global report based on incident data gathered in 2025 from Kaspersky Managed Detection and Response, Kaspersky Incident Response, Kaspersky Compromise Assessment and Kaspersky SOC Consulting. It highlights the most common attacker tactics, techniques and tools, as well as the peculiarities of detected incidents and their distribution across regions and industries.
According to data derived from Kaspersky Incident Response, the top three initial attack vectors have remained relatively stable over the past seven years and have not changed significantly. Valid accounts and exploits in public-facing applications consistently represent the most common entry points. The third position has periodically shifted: malicious emails, once a common initial vector, were replaced by trusted relationships, which first appeared in 2021 and entered the TOP-3 in 2023. By 2025, the distribution of main vectors looked as follows:
These attack vectors are often interconnected within the same chain, for example, organizations compromised through trusted relationships are frequently first breached via exploits in public-facing applications. Recent cases reveal attackers targeting service providers or IT integrators to then access their clients. This problem is compounded by many small service providers lacking dedicated cybersecurity expertise and resources. As they manage accounting software or websites, breaches in these companies can lead to the compromise of their clients’ systems through exploited remote access.
When examining the investigated attacks in terms of duration and impact, the data shows that the majority (50.9%) of them were rapid in nature, typically lasting less than a day and most often resulting in file encryption. A significant portion (33%) were long-lasting, with an average duration of 108 days, during which attackers not only encrypted files but also installed persistence mechanisms, compromised Active Directory and caused data leakage. The remaining 16.1% exhibited a hybrid pattern: they initially appeared as rapid attacks but involved a considerable delay between the initial breach and subsequent malicious activities, extending their overall duration to nearly 19 days.
"Given that attackers are increasingly orchestrating coordinated, multi-stage attacks, organizations cannot afford to rely on a reactive, “firefighting” approach. To counter this, a proactive security posture is essential, one that embeds real-time threat monitoring and continuous detection into everyday operations. This enables defenders to respond swiftly to adversary activity before it escalates. Key measures for protecting digital assets against both rapid intrusions and long-term compromises include: timely patching, enforcement of multi-factor authentication and strict control of third-party access," comments Konstantin Sapronov, Head of Global Emergency Response Team at Kaspersky.
To enhance protection against sophisticated attacks, Kaspersky recommends the following:
- Augment your existing security controls with human-led detection from Kaspersky Managed Detection and Response (MDR) and receive comprehensive and detailed analysis of security incidents with Kaspersky Incident Response. These services offer 24/7 monitoring and cover the entire incident management cycle – from threat identification to continuous protection and remediation.
- Align your internal processes and technologies with today’s evolving threat landscape through Kaspersky SOC Consulting. This service helps you build an in-house SOC from scratch, assess the maturity of an existing SOC or enhance specific capabilities such as detection and response procedures.
- Use centralized and automated solutions such as Kaspersky Next XDR Expert to enable comprehensive protection of all your assets. By aggregating and correlating data from multiple sources in one place and using machine-learning technologies, this solution provides effective threat detection and fast automated response.
To learn more insights from the Kaspersky’s global report, please visit the website.
