A new global Kaspersky Security Services report ‘Anatomy of a Cyber World’ reveals a blind spot in enterprise SOCs: while performance is typically measured by detection and response speed, organizations rarely assess whether they’re detecting the right threats. Large portions of collected telemetry don’t enter real-time detection pipelines, creating hidden gaps that internal assessments tend to miss – and fueling demand for independent SOC Consulting to uncover them.
As organizations continue to invest in Security Operations Centers (SOCs), measuring the real performance of these departments remains a challenge. Operational effectiveness depends not only on the volume of collected data, but on how well that data is used for detection. According to the recent Kaspersky survey, organizations typically evaluate SOC effectiveness through a limited set of key performance indicators: mean time to respond (MTTR) and detect (MTTD) dominate the picture, while deeper indicators like false positive rates or cost per incident remain secondary. The real question is not just how fast the SOC responds, but whether it is detecting threats before they escalate
The findings from the Kaspersky Security Services Global Report[1] tell a consistent story: most SOCs are collecting far more data than they are using for detection. The mean correlation rule coverage across assessed organizations stands at 43%, meaning that on average, active detection logic covers less than half of all ingested data sources. The rest sits in the platform, available for retrospective investigation, threat hunting or compliance purposes, but invisible to real-time detection.
This gap is not always unintentional. Some data is deliberately collected outside the scope of active correlation, serving investigation or regulatory requirements. But in many cases, sources are onboarded without a clear detection plan or with rule development deferred and never completed. However, this is more typical of mature SOCs; in less mature environments, the data is often collected but never actually used.There are several reasons for that, including sources onboarded ahead of planned rule development, compliance-driven collection without active correlation requirements, unclear internal ownership of detection logic and resource constraints deferring engineering work indefinitely. However, the result is the same either way: significant portions of the environment are effectively unmonitored in real time.
What makes this harder to solve is that the problem tends to grow with the organization. SOCs managing the highest data volumes cover only around 30% of their sources with active detection logic. As infrastructure expands, detection engineering capacity rarely scales at the same pace. The sources most consistently left without coverage are network telemetry, databases and web servers – foundational infrastructure that should be at the core of any detection strategy.
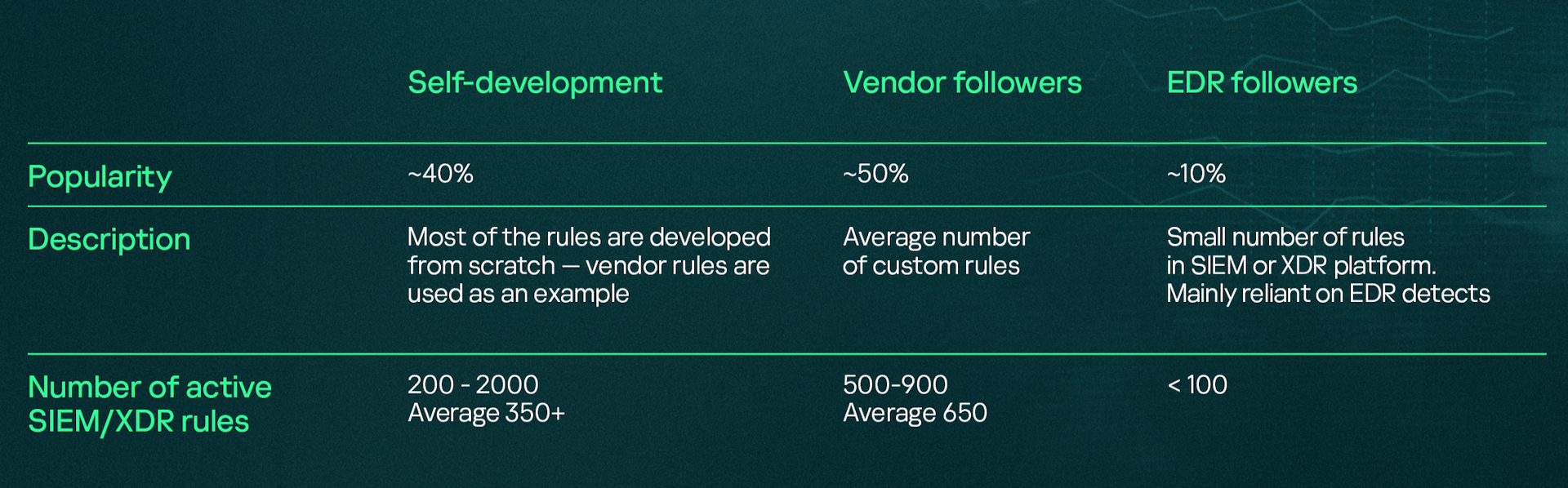
The approach to detection logic itself varies widely. Around 50% of assessed SOCs rely primarily on vendor-provided rule sets, while roughly 40% build their logic from scratch. Vendor-reliant teams frequently face elevated false-positive rates and coverage gaps from insufficient tuning; those dependent on EDR carry blind spots where cross-source correlation is absent. Meanwhile, a lot of organizations set their SOC's detection scope at initial design and never revisit it, meaning blind spots accumulate silently as infrastructure evolves.
“Even with defined KPIs in place, assessing SOC effectiveness internally remains difficult due to insider view bias, which is why organizations are turning to external SOC Consulting to evaluate detection logic, analyze event flows and simulate attacks to understand what is actually being caught. To improve, organizations should build a structured detection engineering process: a repeatable discipline for developing, validating and regular reviewing detection logic,”comments Roman Nazarov, Head of SOC Consulting at Kaspersky.
To align internal processes and technologies with today's evolving threat landscape, organizations can explore Kaspersky SOC Consulting, which helps build an in-house SOC from scratch, assess the maturity of an existing one or enhance specific capabilities such as detection and response procedures. In 2025, the most common consulting projects were SOC Technical Assessment (23.4%), SOC Framework Development (20%) and both SOC Maturity Assessment and SIEM Quality Assurance (11.7% each), reflecting a growing demand for deeper visibility into SOC performance.
To learn more about SOC detection effectiveness and practical steps to strengthen your security monitoring, read the full report.
[1] The ‘Anatomy of a Cyber World’ is a comprehensive global report drawing on incident statistics from Kaspersky Managed Detection and Response, Kaspersky Incident Response, Kaspersky Compromise Assessment and Kaspersky SOC Consulting, shedding light on the most prevalent attacker tactics, techniques and tools, as well as the characteristics of detected incidents and their distribution across regions and industry sector
