According to Kaspersky ICS CERT, almost one in three industrial computer was subject to malicious activity in H1 2021. During the first half of 2021, cybercriminals intensively used various types of spyware and malicious scripts while performing their attacks. These types of threats are growing for the second six-month period and pose a big challenge to industrial control systems (ICS).
According
to Kaspersky ICS CERT, almost one in three industrial computer was subject to
malicious activity in H1 2021. During the first half of 2021, cybercriminals
intensively used various types of spyware and malicious scripts while performing
their attacks. These types of threats are growing for the second six-month
period and pose a big challenge to industrial control systems (ICS).
Attacks against industrial organizations are
particularly dangerous as cybercriminals might steal data and money and disrupt
the established system of production. An increase in the diversity of threats
to such networks indicates the growth of the attackers’ interest in them and, consequently,
an increase in the need to reliably protect them.
According to the “Threat Landscape for Industrial
Automation Systems Report”, Kaspersky
security solutions blocked over 20,000 malware variants during the first six
months of 2021. To find out more about how the ICS threat landscape changed
during the reporting period, Kaspersky researchers analyzed various types of
malware used during cyberattacks against industrial systems. They subsequently
found that the percentage of spyware and malicious scripts used against ICS has
grown continuously over the past half a year.
In fact, spyware (Trojan-Spy malware, backdoors and
keyloggers), which is mostly used to steal money, are up by 0.4 percentage
points. At the same time, malicious scripts grew by 0.7 percentage points. Threat
actors use such scripts on various websites hosting pirated content to redirect
users to sites which distribute spyware or malware designed to mine
cryptocurrency without the user’s knowledge.
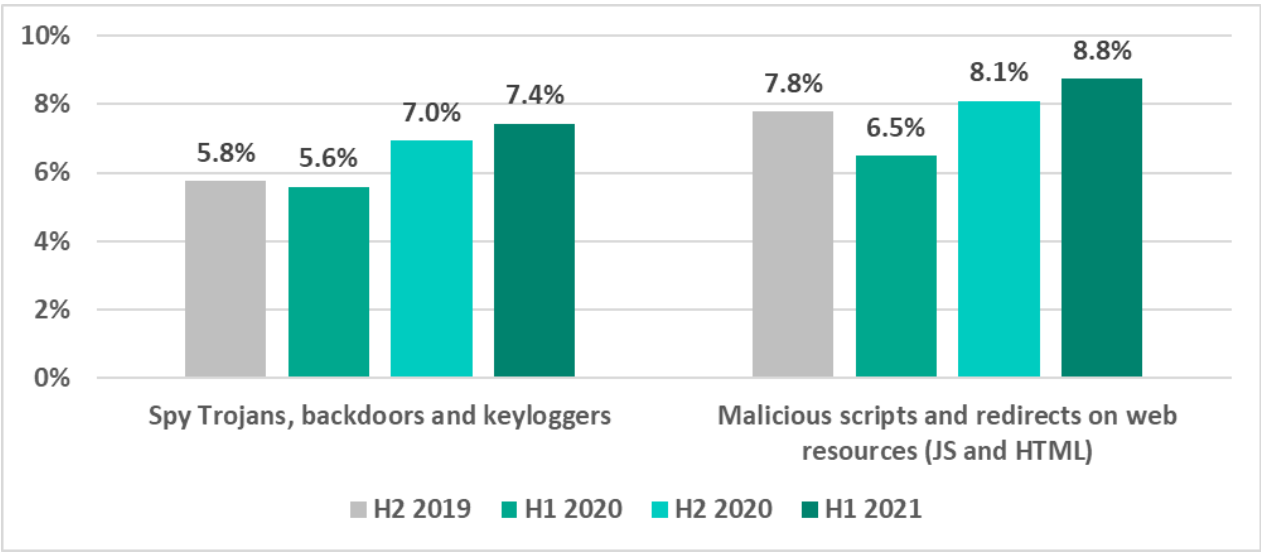
Percentage of ICS computers on which malicious objects were blocked in H2 2019-H1 2021
“Industrial organizations always attract attention from both cybercriminals and politically-motivated threat actors. Reflecting on the previous half year, we have seen among other findings, growth in the number of cyberespionage and malicious credential stealing campaigns. Their success has most likely been the main factor raising the ransomware threat to such a high degree. And I see no reason why some of the APT groups won’t benefit from these credential stealing campaigns as well.” comments Evgeny Goncharov, security expert at Kaspersky. Read more about the ICS threat landscape in H1 2021 on the Kaspersky ICS CERT website.
To keep your ICS computers protected from various threats, Kaspersky experts recommend:
- Using security solutions for OT endpoints and networks, such as Kaspersky Industrial CyberSecurity to ensure comprehensive protection for all industry critical systems.
- Regularly updating operating systems and application software that are part of the enterprise’s industrial network. Apply security fixes and patches to ICS network equipment as soon as they are available.
- Undertaking dedicated ICS security training for IT security teams and OT engineers, which is crucial to improve responses to new and advanced malicious techniques.
- Conducting regular security audits of OT networks to identify and eliminate security issues.
- Providing the security team responsible for protecting industrial control systems with up-to-date threat intelligence. ICS Threat Intelligence Reporting service provides insights into current threats and attack vectors, as well as the most vulnerable elements in OT and industrial control systems and how to mitigate them.
- Using ICS network traffic monitoring, analysis and detection solutions for better protection from attacks potentially threatening technological processes and main enterprise assets.
About Kaspersky ICS CERT
Kaspersky Industrial Control Systems Cyber Emergency Response Team (Kaspersky ICS CERT) is a global project launched by Kaspersky in 2016 to coordinate the efforts of automation system vendors, industrial facility owners and operators, and IT security researchers to protect industrial enterprises from cyberattacks. Kaspersky ICS CERT devotes its efforts primarily to identifying potential and existing threats that target industrial automation systems and the Industrial Internet of Things. Kaspersky ICS CERT is an active member and partner of leading international organizations that develop recommendations on protecting industrial enterprises from cyberthreats. ics-cert.kaspersky.com
About Kaspersky
Kaspersky is a global cybersecurity and digital privacy company founded in 1997. Kaspersky’s deep threat intelligence and security expertise is constantly transforming into innovative security solutions and services to protect businesses, critical infrastructure, governments and consumers around the globe. The company’s comprehensive security portfolio includes leading endpoint protection and a number of specialized security solutions and services to fight sophisticated and evolving digital threats. Over 400 million users are protected by Kaspersky technologies and we help 240,000 corporate clients protect what matters most to them. Learn more at www.kaspersky.com.
