According to Kaspersky Lab researchers, cybercriminals have started using sophisticated infection methods and techniques borrowed from targeted attacks in order to install mining software on attacked PCs within organizations.
According to Kaspersky Lab researchers, cybercriminals have started using sophisticated infection methods and techniques borrowed from targeted attacks in order to install mining software on attacked PCs within organizations. The most successful group observed by Kaspersky Lab earned at least $7 million by exploiting their victims in just six months during 2017.
Although the cryptocurrency market is experiencing plenty of ups and downs, last year’s phenomena with surges in the value of Bitcoin has significantly changed not only global economics, but the world of cybersecurity as well. With the aim of earning cryptocurrency, criminals have started to use mining software in their attacks, which, like ransomware, has a simple monetization model. But, unlike ransomware, it doesn’t destructively harm users and is able to stay undetected for a long time by silently using the PC’s power. Back in September 2017, Kaspersky Lab recorded a rise of miners that started actively spreading across the world, and predicted its further development. The latest research reveals that this growth has not only continued, but has also increased and extended.
Kaspersky Lab researchers recently identified a cybercriminal group with APT-techniques in their arsenal of tools to infect users with miners. They have been using the process-hollowing method that is usually used in malware and has been seen in some targeted attacks of APT actors, but has never been observed in mining attacks before.
The attack works in the following way: the victim is lured into downloading and installing an advertisement software with the miner installer hidden inside. This installer drops a legitimate Windows utility, with the main purpose being to download the miner itself from a remote server. After its execution, a legitimate system process starts, and the legitimate code of this process is changed to malicious code. As a result, the miner operates under the guise of a legitimate task, so it will be impossible for a user to recognize if there is a mining infection. It is also challenging for security solutions to detect this threat. In addition, miners mark this new process through the way it restricts any task cancellation. If the user tries to stop the process, the computer system will reboot. As a result, criminals protect their presence in the system for a longer and more productive time.
Based on Kaspersky Lab’s observations, the actors behind these attacks have been mining Electroneum coins and earned almost $7 million during the second half of 2017, which is comparable to the sums that ransomware creators used to earn.
“We see that ransomware is fading into the background, instead giving way to miners. This is confirmed by our statistics, which show a steady growth of miners throughout the year, as well as by the fact that cybercriminals groups are actively developing their methods and have already started to use more sophisticated techniques to spread mining software. We have already seen such an evolution – ransomware hackers were using the same tricks when they were on the rise,” said Anton Ivanov, Lead Malware Analyst at Kaspersky Lab.
Overall, 2.7 million users were attacked by malicious miners in 2017, according to Kaspersky Lab data. That is approximately 50% higher than in 2016 (1.87 mln). They have been falling victims as a result of adware, cracked games and pirated software used by cybercriminals to secretly infect their PCs. Another approach used was web mining through a special code located in an infected web page. The most widely used web miner was CoinHive, discovered on many popular websites.
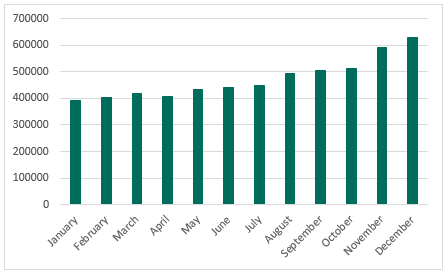
Number of Kaspersky Lab users attacked by malicious cryptocurrency miners in 2017
In order to stay protected, Kaspersky Lab recommends that users do the following:
- Don’t click on unknown websites, or suspicious banners and ads;
- Do not download and open unknown files from untrusted sources;
- Install a reliable security solution such as Kaspersky Internet Security or Kaspersky Free Antivirus that detects and protects you from all possible threats, including malicious mining software.
For organizations, Kaspersky Lab recommends the following:
- Carry out a security audit on a regular basis
- Install a reliable security solution on all workstations and servers and make sure all its components are enabled to ensure the maximum protection. Kaspersky Lab customers are protected with Kaspersky Endpoint Security for Business.
More information on miners’ activities can be found on Securelist.com
Key trends in mining attacks and the latest discoveries of cryptocurrency threats will be presented at the Security Analyst Summit by Kaspersky Lab researchers, March 9 2018 : https://sas.kaspersky.com/
