The global nightmare of ransomware shows no sign of slowing down, with the volume of mobile ransomware rising over three-fold (3.5 times) during the first few months of the year, according to Kaspersky Lab’s Malware Report for Q1, 2017.
The global nightmare of ransomware shows no sign of slowing down, with the volume of mobile ransomware rising over three-fold (3.5 times) during the first few months of the year, according to Kaspersky Lab’s Malware Report for Q1, 2017. The number of mobile ransomware files detected reached 218,625 during the quarter, compared to 61,832 in the previous quarter, with the Congur family accounting for more than 86%. Ransomware targeting all devices, systems and networks also continued to grow, with 11 new cryptor families and 55,679 new modifications making their appearance in Q1.
Congur ransomware is primarily a blocker – setting or resetting the device PIN (passcode) so the requires the attackers to have administrator rights on the device, and some variants of the malware take further advantage of these rights to install their module into the system folder from where it is almost impossible to remove.
Despite the popularity of Congur, Trojan-Ransom.AndroidOS.Fusob.h remained the most widely used mobile ransomware, accounting for nearly 45% of all users attacked by this threat during the quester. Once run, the Trojan requests administrator privileges, collects information about the device, including GPS coordinates and call history, and uploads the data to a malicious server. Based on what it receives, the server may send back a command to block the device.
The USA became the country hardest hit by mobile ransomware in Q1, with Svpeng ransomware the most widespread threat.
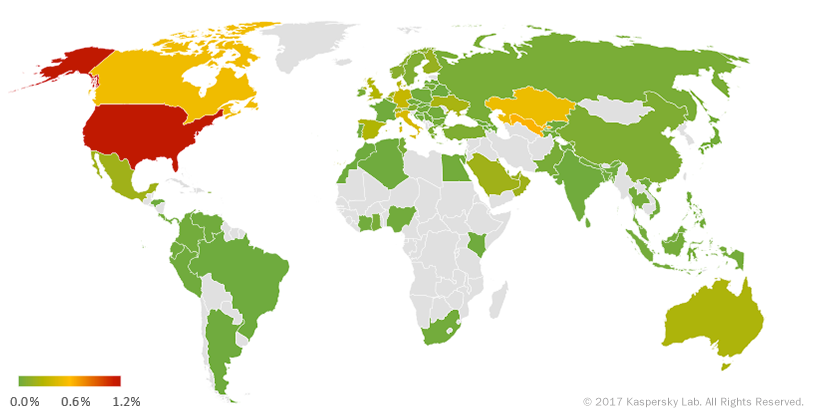
Geography of mobile Trojan-Ransomware in Q1 2017 (percentage of all users attacked)
In all, 55,679 new Windows ransomware modifications were detected during the quarter representing a near two-fold increase on Q4, 2016 (29,450). Most of these new modifications belonged to the Cerber family.
“The mobile threat landscape for ransomware was far from calm in Q1. Ransomware targeting mobile devices soared, with new ransomware families and modifications continuing to proliferate. People need to bear in mind that attackers can – and increasingly will - try to block access to their data not only on a PC but also on their mobile device,” notes Roman Unuchek, Senior Malware Analyst at Kaspersky Lab.
Other online threat statistics from the Q1, 2017 report include:
- Kaspersky Lab solutions detected and repelled 479,528,279 malicious attacks from online resources located in 190 countries all over the world.
- 79,209,775 unique URLs were recognized as malicious by web antivirus components.
- Attempted infections by malware that aims to steal money via online access to bank accounts were registered on 288,000 user computers.
- Crypto-ransomware attacks were blocked on 240,799 computers of unique users.
- Kaspersky Lab’s file antivirus detected a total of 174,989,956 unique malicious and potentially unwanted objects.
- Kaspersky Lab mobile security products also detected:
o 1,333,605 malicious installation packages;
o 32,038 mobile banking Trojans (installation packages).
To reduce the risk of infection, users are advised to:
- Use robust security solutions and make sure they keep all software up to date.
- Regularly run a system scan to check for possible infection.
- Stay wise while online. Do not enter personal information into a website if you are at all unsure or suspicious.
- Back up valuable information.
For help and advice on dealing with ransomware visit No More Ransom
Read the full version of the Kaspersky Lab’s Malware Report on Securelist.com.
