The Kaspersky Lab Global Research and Analysis Team has discovered new wave of targeted attacks against the industrial and engineering sectors in multiple countries around the world
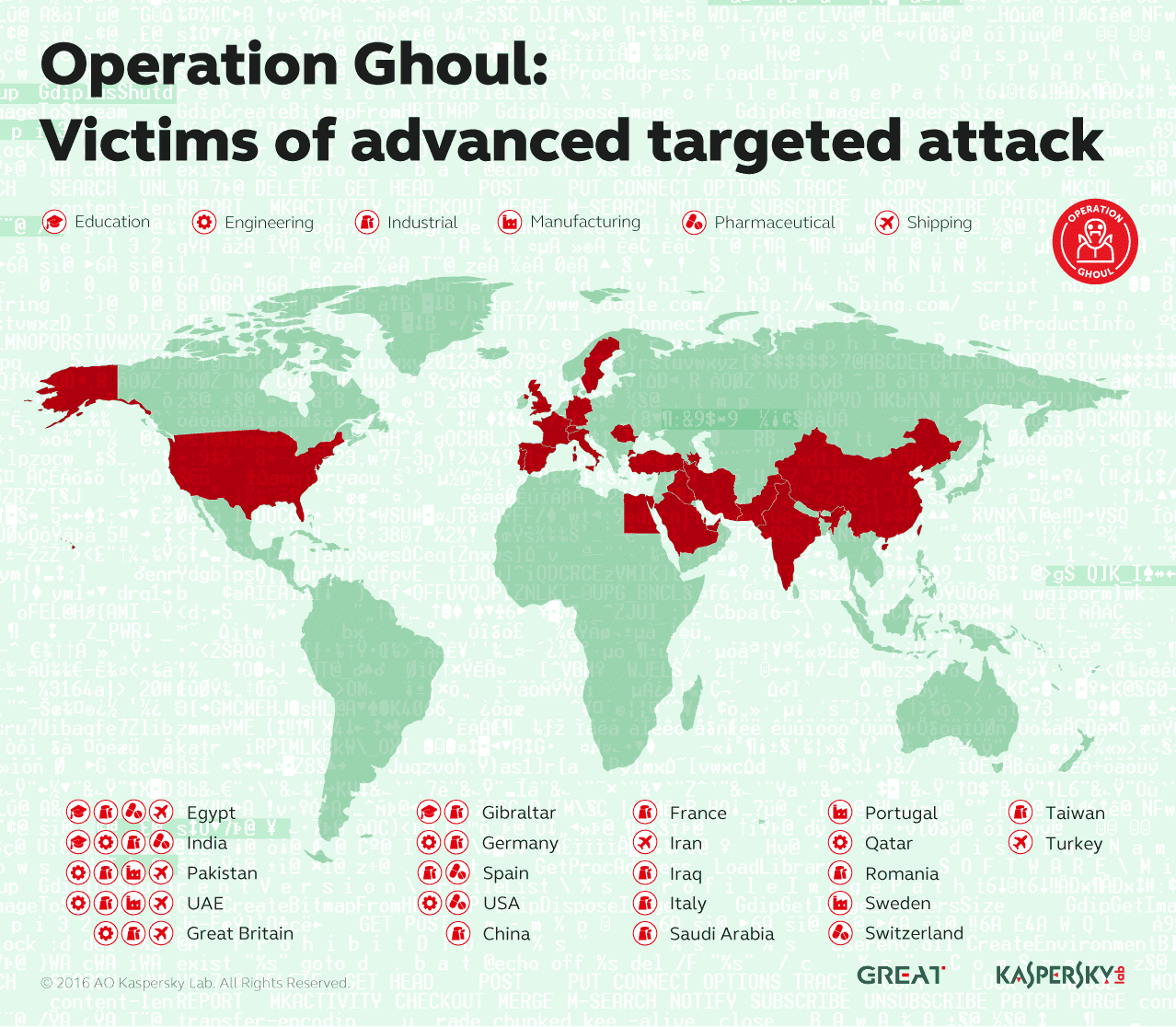
The Kaspersky Lab Global Research and Analysis Team has discovered new wave of targeted attacks against the industrial and engineering sectors in multiple countries around the world. Using spear-phishing emails and malware based on commercial spyware kit, criminals hunt for valuable business related data stored in their victims’ networks. In total over 130 organizations from 30 countries, including Spain, Pakistan, United Arab Emirates, India, Egypt, United Kingdom, Germany, Saudi Arabia and other countries were successfully attacked by this group.
In June 2016, Kaspersky Lab researchers spotted a wave of spear-phishing e-mails with malicious attachments. These messages were mostly sent to the top and middle level managers of numerous companies. The e-mails sent by the attackers appeared to be coming from a bank in the UAE: they looked like payment advice from the bank with an attached SWIFT document, but in reality the attached archive contained malware.
Further investigation conducted by Kaspersky Lab researchers, showed that the spear-phishing campaign has most likely been organized by a cybercriminal group which has been tracked by company researchers since March 2015. The June attacks appear to be the most recent operation conducted by this group.
The malware in the attachment is based on the HawkEye commercial spyware that is being sold openly on the Darkweb, and provides a variety of tools for the attackers. After installation it collects interesting data from the victim's PC, including:
- Keystrokes
- Clipboard data
- FTP server credentials
- Account data from browsers
- Account data from messaging clients (Paltalk, Google talk, AIM...)
- Account data from email clients (Outlook, Windows Live mail...)
- Information about installed applications (Microsoft Office)
This data is then sent to the threat actor’s command and control servers. Based on information received from the sinkhole of some command and control servers, the majority of the victims are organizations working in the industrial and engineering sectors, others include shipping, pharmaceutical, manufacturing, trading companies, educational organizations and other types of entities.
These companies all hold valuable information that could be subsequently sold on the black market - financial profit is the main motivation of the attackers behind Operation Ghoul.
Dubbed Operation Ghoul by Kaspersky Lab researchers, it is only one among several other campaigns that are supposedly controlled by the same group. The group is still active.
“In ancient Folklore, the Ghoul is an evil spirit associated with consuming human flesh and hunting kids, originally a Mesopotamian demon. Today, the term is sometimes used to describe a greedy or materialistic individual. This is quite a precise description of the group behind Operation Ghoul. Their main motivation is financial gain resulting either from sales of stolen intellectual property and business intelligence, or from attacks on their victim’s banking accounts. Unlike state-sponsored actors, which choose targets carefully, this group and similar groups might attack any company. Even though they use rather simple malicious tools, they are very effective in their attacks. Thus companies that are not prepared to spot the attacks, will sadly suffer”, - said Mohammad Amin Hasbini, security expert at Kaspersky Lab.
In order to protect your company from Operation Ghoul and other threats like this, Kaspersky Lab researchers recommend businesses implement the following measures:
- Educate your staff so they are able to distinguish a spear phishing email or a phishing link from real emails and links
- Use a proven corporate grade security solution, in combination with anti-targeted attack solutions, capable of catching attacks by analyzing network anomalies
- Provide your security staff with access to the latest threat intelligence data, which will arm them with helpful tools for targeted attack prevention and discovery, such as Indicators of compromise and YARA rules
Kaspersky Lab products detect the malware used by the group behind Operation Ghoul with the following detection names:
- Trojan.MSIL.ShopBot.ww
- Trojan.Win32.Fsysna.dfah
- Trojan.Win32.Generic
Read more about Operation Ghoul in our blogpost at Securelist.com.
Learn more about how Kaspersky Lab products can protect users from this threat.
The full report on Operation Ghoul operations has been available in advance for customers of Kaspersky APT Intelligence Reporting Service.