An in-depth investigation by Kaspersky Lab researchers into Brazilian and Russian underground forums has revealed that cybercriminals on opposite sides of the world have overcome time differences and language barriers to foster a close cooperation that is driving a rapid evolution of the malicious tools used in attacks
An in-depth investigation by Kaspersky Lab researchers into Brazilian and Russian underground forums has revealed that cybercriminals on opposite sides of the world have overcome time differences and language barriers to foster a close cooperation that is driving a rapid evolution of the malicious tools used in attacks.
The Brazilian and Russian cybercrime underground are two of the most visible markets to security researchers due to their relative openness, high level of activity and large number of online forums used by criminals to communicate with each other. Historically, both markets have developed independently from each other, creating distinct cyber-attack techniques tailored to local conditions (e.g. “Boleto” malware in Brazil, or malware targeting mobile banking services in Russia). However, the investigation by Kaspersky Lab researchers shows that Brazilian and Russian-speaking criminals have established a system of cooperation in recent years. Brazilian criminals seek out samples on Russian underground forums, buying new crimeware and ATM/PoS malware, or offering their own services. And this trade is two-way, with cooperation helping speed up malware evolution.
Real-life examples
Signs of cooperation were spotted on one underground forum frequented by Russian-speaking users. In one of the topics listed a user named Doisti74 stated an interest in buying Brazilian “loads”, which is cybercriminal jargon for successful installations of malware on victim PCs located in Brazil.
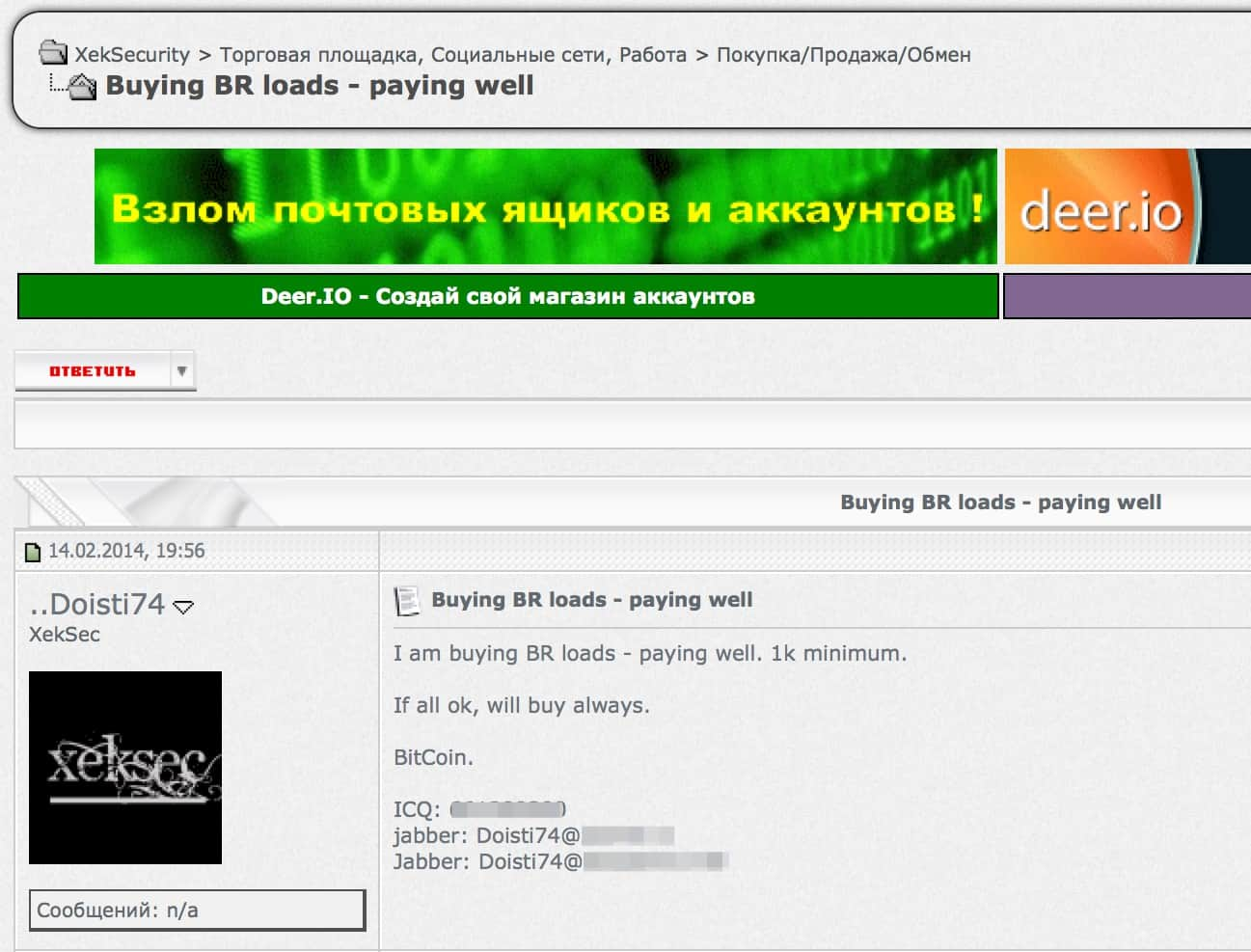
The Kaspersky Lab researchers noticed a user with the same name in the Brazilian underground scene where he is known as an active user of forums and has been identified as a user that spreads Ransomware targeting Brazilian users.
Another case shows how criminals share malicious infrastructure. A few months after an allegedly Russian banking Trojan family (Crishi) started using an algorithm that generated domains in abuse-resistant hosting in Ukraine, Brazilian criminals behind the infamous Boleto malware campaigns also started using the infrastructure. Without some form of cooperation between the Boleto actors and those behind the domain-generating algorithm, it would have been impossible to make identification of command and control servers more difficult for researchers and law enforcement agencies.
Cybercriminals are also borrowing malicious technologies from each other. For instance, since at least 2011 Brazilian criminals have been actively abusing PACs – an outdated technology, but one that is still supported by some browsers – to redirect victims to fake banking pages. Less than a year passed before Kaspersky Lab researchers detected the same technique being used in Capper – yet another banking Trojan targeting Russian banks and most likely created by Russian-speaking criminals.
These are just some of the many examples of cooperation between Brazilian and Russian-speaking cybercriminals observed by Kaspersky Lab researchers in recent years.
“Just a few years ago, Brazilian banking malware was very basic and easy to detect. With time, however, the malware authors have adopted multiple techniques to avoid detection, including code obfuscation, root and bootkit functions and so on, making their malware much more sophisticated and harder to combat. This is thanks to malicious technologies developed by Russian-speaking criminals. And this cooperation works both ways,” said Thiago Marques, security researcher at Kaspersky Lab.
“Kaspersky Lab's experience of tracking and combating the Russian and LatAm cyber-underground is unparalleled. Our experts detect emerging malicious trends long before they become widespread and we are leveraging this knowledge to combat the spread of local cybercrime worldwide. We think the best way to address this kind of international threat is to conduct an international investigation of these activities. Just as cybercrime has no borders, nor should any investigation.”
To learn more about how Brazilian malware has evolved in recent years, read the research conducted by Kaspersky Lab’s experts for Securelist.com.
