Kaspersky Lab’s Global Research and Analysis Team has published extensive research on the Adwind Remote Access Tool (RAT), a cross-platform, multifunctional malware program also known as AlienSpy, Frutas, Unrecom, Sockrat, JSocket and jRat, and which is distributed through a single malware-as-a-service platform
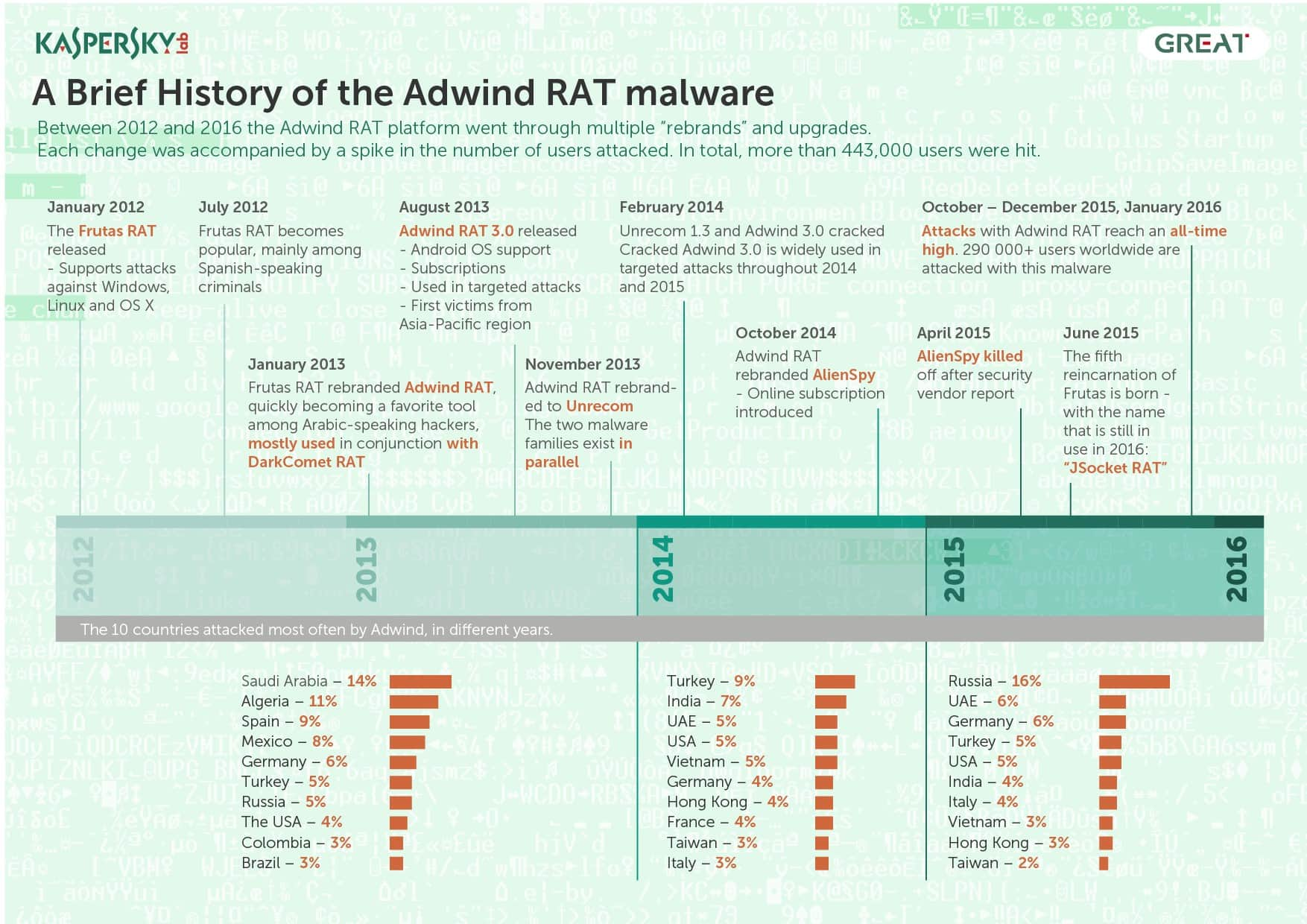
Kaspersky Lab’s Global Research and Analysis Team has published extensive research on the Adwind Remote Access Tool (RAT), a cross-platform, multifunctional malware program also known as AlienSpy, Frutas, Unrecom, Sockrat, JSocket and jRat, and which is distributed through a single malware-as-a-service platform. According to the results of the investigation, conducted between 2013 and 2016, different versions of the Adwind malware have been used in attacks against at least 443,000 private users, commercial and non-commercial organizations around the world. The platform and the malware are still active.
At the end of 2015, Kaspersky Lab researchers became aware of an unusual malware program that had been discovered during an attempted targeted attack against a bank in Singapore. A malicious JAR file was attached to a spear-phishing email received by a targeted employee at the bank. The malware’s rich capabilities, including its ability to run on multiple platforms as well as the fact that it was not detected by any antivirus solution, immediately captured the attention of the researchers.
The Adwind RAT
It turned out that the organization had been attacked with the Adwind RAT, a backdoor available for purchase and written entirely in Java, which makes it cross-platform. It can run on Windows, OS X, Linux and Android platforms providing capabilities for remote desktop control, data gathering, data exfiltration etc.
If the targeted user opens the attached JAR file the malware self-installs and attempts to communicate with the command and control server. The malware’s list of functions includes the ability to:
- collect keystrokes
- steal cached passwords and grab data from web forms
- take screenshots
- take pictures and record video from the webcam
- record sound from the microphone
- transfer files
- collect general system and user information
- steal keys for cryptocurrency wallets
- manage SMS (for Android)
- steal VPN certificates
While it is used mainly by opportunistic attackers and distributed in massive spam campaigns, there are cases where Adwind was used in targeted attacks. In August 2015 Adwind popped up in the news related to cyber-espionage against an Argentinian prosecutor who had been found dead in January 2015. The incident against the Singaporean bank was another example of a targeted attack. A deeper look into events related to the usage of the Adwind RAT showed that these targeted attacks were not the only ones.
Targets of interest
During their investigation the Kaspersky Lab researchers were able to analyze nearly 200 examples of spear-phishing attacks organized by unknown criminals to spread the Adwind malware, and were able to identify the industries most of the targets worked in:
- Manufacturing
- Finance
- Engineering
- Design
- Retail
- Government
- Shipping
- Telecom
- Software
- Education
- Food production
- Healthcare
- Media
- Energy
Based on information from Kaspersky Security Network, the 200 examples of spear-phishing attacks observed in the six months between August 2015 and January 2016 resulted in Adwind RAT malware samples being encountered by more than 68,0000 users.
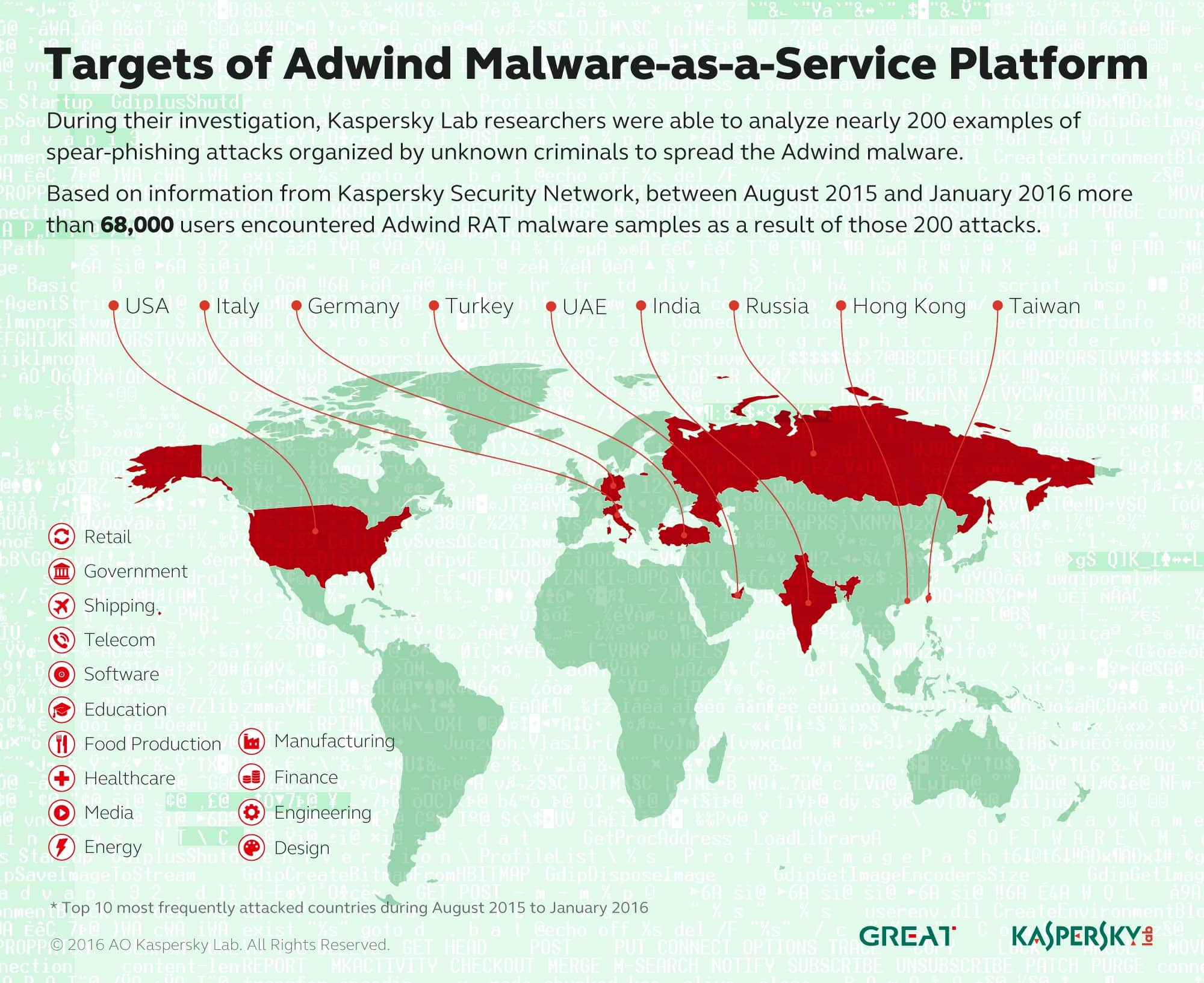
The geographical distribution of attacked users registered by KSN during this period shows that almost half of them (49%) were living in the following 10 countries: United Arab Emirates, Germany, India, the USA, Italy, Russia, Vietnam, Hong Kong, Turkey and Taiwan.
Based on the profiles of identified targets, Kaspersky Lab researchers believe that the clients of the Adwind platform fall into the following categories: scammers that want to move to the next level (using malware for more advanced fraud), unfair competitors, cyber-mercenaries (spies for hire), and private individuals that want to spy on people they know.
Threat-as-a-Service
One of the main features that distinguishes the Adwind RAT from other commercial malware is that it is distributed openly in the form of a paid service, where the “customer” pays a fee in return for use of the malicious program. Based on an investigation of users' activity on the internal message board and some other observations, Kaspersky Lab researchers estimate that there were around 1,800 users in the system by the end of 2015. This makes it one of the biggest malware platforms in existence today.
“The Adwind platform in its current state lowers significantly the minimum amount of professional knowledge required by a potential criminal looking to enter the area of cybercrime. What we can say based on our investigation of the attack against the Singaporean bank is that the criminal behind it was far from being a professional hacker, and we think that most of the Adwind platform’s “clients” have that level of computer education. That is a worrisome trend,” - said Aleksandr Gostev, Chief Security Expert at Kaspersky Lab.
“Despite multiple reports about different generations of this tool, published by security vendors in recent years, the platform is still active and inhabited with criminals of all kinds. We’ve conducted this research in order to attract the attention of the security community and law enforcement agencies and to make the necessary steps in order to disrupt it completely,” - said Vitaly Kamluk, Director of Global Research & Analysis Team in APAC at Kaspersky Lab.
Kaspersky Lab has reported its findings on the Adwind platform to law enforcement agencies.
In order to protect yourself and your organization against this threat, Kaspersky Lab encourages enterprises to review the purpose of using a Java platform and to disable it for all unauthorized sources.
Read more about the Adwind Malware-as-a-Service platform on Securelist.com
Learn how sophisticated targeted attacks are investigated: http://www.youtube.com/watch?v=FzPYGRO9LsA
More about cyber-espionage operations here: https://apt.securelist.com/
