Jochen Michels, Head of Public Affairs, Europe
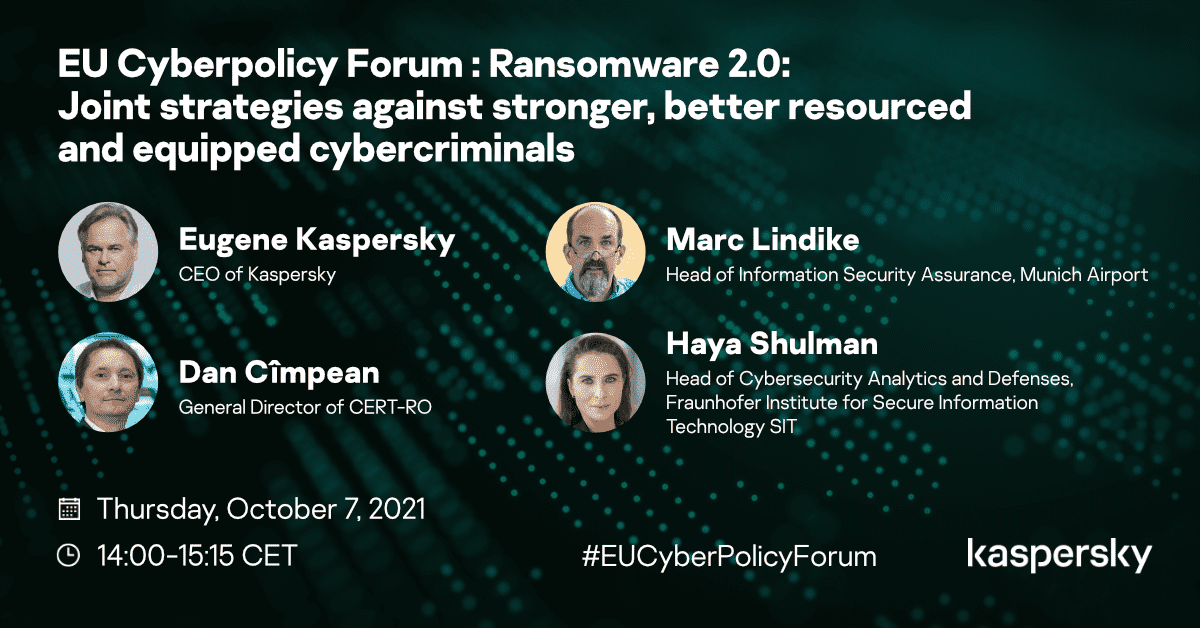
‘Just as the vaccine is our strongest weapon against the COVID-19 pandemic, technical solutions must serve as our main weapon against ransomware criminals,’ said Kaspersky CEO Eugene Kaspersky during Thursday’s EU Cyberpolicy Forum on joint strategies against ransomware, before expressing that, unfortunately, ‘when it comes to ransomware, most cybersecurity products are only placebos’. This statement was rather representative of the candid nature of the debate among four leading European cybersecurity experts on how to tackle the ever-growing issue of ransomware.
Indeed, ransomware attacks are on the rise, and not only in Europe but all around the globe. According to Kaspersky’s own study, in some regions the covid pandemic has led to a tenfold increase in such attacks, with no clear sign indicating that this trend will slow down. ‘To perform a cyberattack, you need only expertise, nothing else,’ explained Haya Shulman, Head of Cybersecurity Analytics and Defences at Germany’s Fraunhofer Institute for Security Information Technology (SIT) – adding that the abstract and indirect nature of such attacks means that the ‘psychological barrier’ is higher and therefore people are not so sensitive to their occurring, at least when they occur to others.
‘The techniques used by such criminals are surprisingly straightforward,’ noted Dan Cimpean, Director of the National Cybersecurity Directorate of Romania. Others agreed that given that such software is relatively easy to procure on the ‘Dark Web’, more and more actors are involved in such activities – and not necessarily those actors with the ability to conduct sophisticated attacks. ‘I don’t believe that there are many targeted ransomware attacks against companies,’ noted Marc Lindike, Head of Information Security Assurance at Munich Airport, adding: ‘my theory is that a lot of these attacks are shotgun-style attacks targeting everybody’.
Given that a lot of ransomware attacks are relatively low in sophistication, three rather simple steps were identified that could go a long way in reducing their effectiveness.
The first is awareness and cyber hygiene – ‘without awareness, it’s impossible to fight this phenomenon’, warned Dan Cimpean, adding that this awareness needs to expand to all levels, including ‘policymakers, top-level management, operational teams, students and average citizens’. Marc Lindike agreed. ‘Protecting the front door, for example by enhancing cyber hygiene, is important,’ he emphasized, but warned that this approach is not enough against the more sophisticated strategies, such as supply chain attacks. ‘It’s not enough to protect your front door if the bad guys understand that they can first hijack your cleaning company and then use it to hack your company. We also need to protect the back doors’ – he added.
The second important step is to block – or at least increase the transparency of – the payment channels used by ransomware criminals. All speakers agreed that cryptocurrencies have been a godsend for the ransomware ‘business’. ‘Since China banned cryptocurrencies, there are not many Mandarin-speaking ransomware criminals’, noted Eugene Kaspersky. Dan Cimpean agreed, but warned that there are still other ways through which criminals can move money without being caught.
The third and final layer of protection against ransomware identified is the use of effective cybersecurity software on devices. However, the effectiveness of the various software solutions offered varies greatly from product to product. Indeed, independent tests show that only Kaspersky’s endpoint security solution provides 100% protection against ransomware in practice, with the second most effective product lagging behind at a mere 62% effectiveness. These were the worrying numbers that led to the Kaspersky CEO’s ‘placebo’ comments mentioned in the opening paragraph. ‘We are fighting very smart guys – the cybersecurity industry must be smart as well’ – he warned.
But what can be done once an attack has already taken place?
In brief, the speakers agreed that although, prevention of such attacks can be achieved through relatively simple steps, once an attack has already taken place, catching the attackers is a much more difficult task. ‘The attribution topic is challenging,’ noted Ms Shulman, explaining that in certain cases cybercriminals purposefully use the tools and methods of other actors so as to make attribution even more challenging. Eugene added: ‘Almost every cybercriminal can be investigated. Where our expertise is requested by a public authority, often we find e-mail addresses and the internet provider of the perpetrators within a few days,’ he explained, and emphasized that examples like this prove that strong cooperation between different actors such as law enforcement, policy-makers and industry is crucial. For his part, Dan Cimpean emphasized the importance of making the carrying out of such attacks so expensive as to not be worth it – a concept that echoes Kaspersky’s ‘cyber immunity’ concept. ‘We need to make the cost of ransomware prohibitive,’ he explained, adding that such efforts need to forget about the concept of national borders, since the threats are also international.
Indeed, the topic of international cooperation was the second major point of the discussions, especially in the context of tackling more sophisticated attacks such as those on supply chains. It was one of the messages that all speakers could agree on: In cyber, there are no borders. So we need cooperation among all stakeholders in the ecosystem to stop ransomware.
Useful links
NoMoreRansom: The “No More Ransom” website is an initiative of the National High Tech Crime Unit of the Netherlands’ police, Europol’s European Cybercrime Centre, Kaspersky and McAfee, which helps victims of ransomware retrieve their encrypted data without having to pay the criminals.
Anti-Ransomware Tool: Ransomware attacks someone every five seconds. Our free tool provides proven, powerful protection from ransomware like WannaCry, Petya, Bad Rabbit, Locky, TeslaCrypt, Rakhni, Rannoh and many others. It's completely compatible with your current security solutions and will successfully compliment them.
We look forward to hosting you at our next #EUCyberPolicyForum. If you are interested in participating in forthcoming EU policy-related webcasts organized by Kaspersky, please send an email to policy.europe@kaspersky.com.
