Explore the Kaspersky Enterprise portfolio
KASPERSKY NEXT
Cybersecurity that grows with your business
Kaspersky Next offers tiered security to strengthen your security at every step of your business’s growth – from essential endpoint protection and EDR to advanced AI-driven XDR that delivers total cybersecurity for proactive cyberthreat defense.
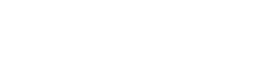
Resilient. Unified. Adaptive.
A comprehensive IT-OT cybersecurity ecosystem for complete protection: wehether you're an industrial business or a large enterprise, we have the expertise, insights, and adaptability to meet you where you are and take you where you need to go, safely
Kaspersky
Expertise Centers
Discover why expertise is so important when choosing a cybersecurity vendor.
INDUSTRIES
Industry-specific security that understands your business
Protect continuity, optimize efficiency
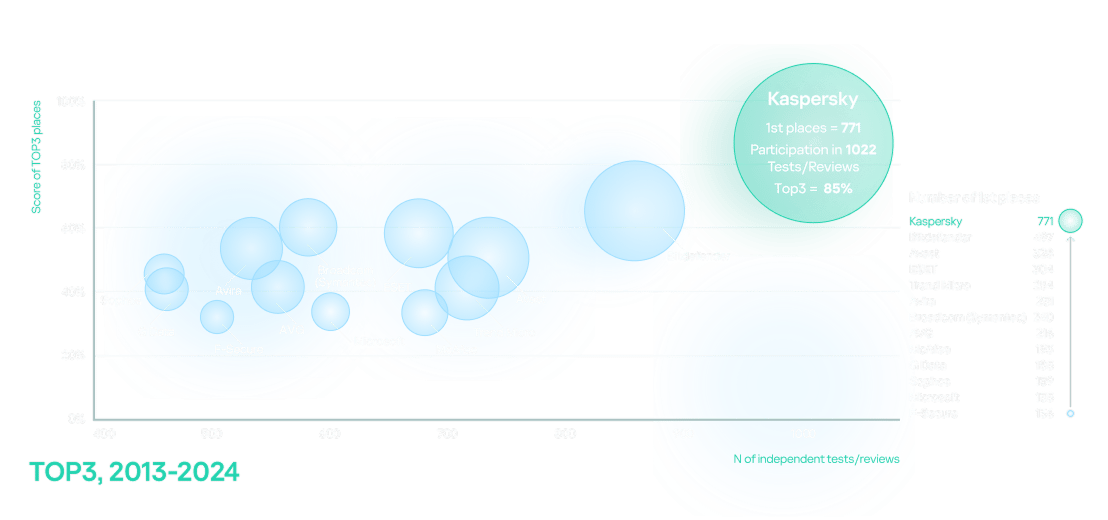
Most tested. Most awarded.
Kaspersky's most tested, most awarded status was uninterrupted
between 2013 and 2024.
Resource Center
Connect with your local partner
If you'd like to find out how to protect your business from complex cybersecurity attacks, with the most tested, most awarded product on the market, please contact your local partner or request a demo.