Kaspersky has identified PhantomRPC, a vulnerability in the Windows Remote Procedure Call architecture that stems from architectural design behavior. The results of the research were presented at Black Hat Asia 2026.
The company’s researchers found that the issue enables a new local privilege escalation technique rather than the exploitation of a single faulty component. In scenarios where a process has impersonation privileges, attackers can abuse this behavior to gain SYSTEM-level access.
Five different exploitation paths were reviewed to demonstrate how privileges can be escalated from various local or network service contexts to SYSTEM or other highly privileged accounts. As the issue stems from an architectural weakness, the number of potential attack vectors is effectively unlimited: any new process or service that depends on RPC could introduce an additional escalation path.
“The exact exploitation paths may vary from one system to another, depending on factors such as the software installed on the system, the DLLs involved in RPC communication, and whether the corresponding RPC servers are available,” says Haidar Kabibo, application security specialist at Kaspersky. “This variability makes the vulnerability particularly important for businesses to consider when assessing their exposure and mitigation strategies.”
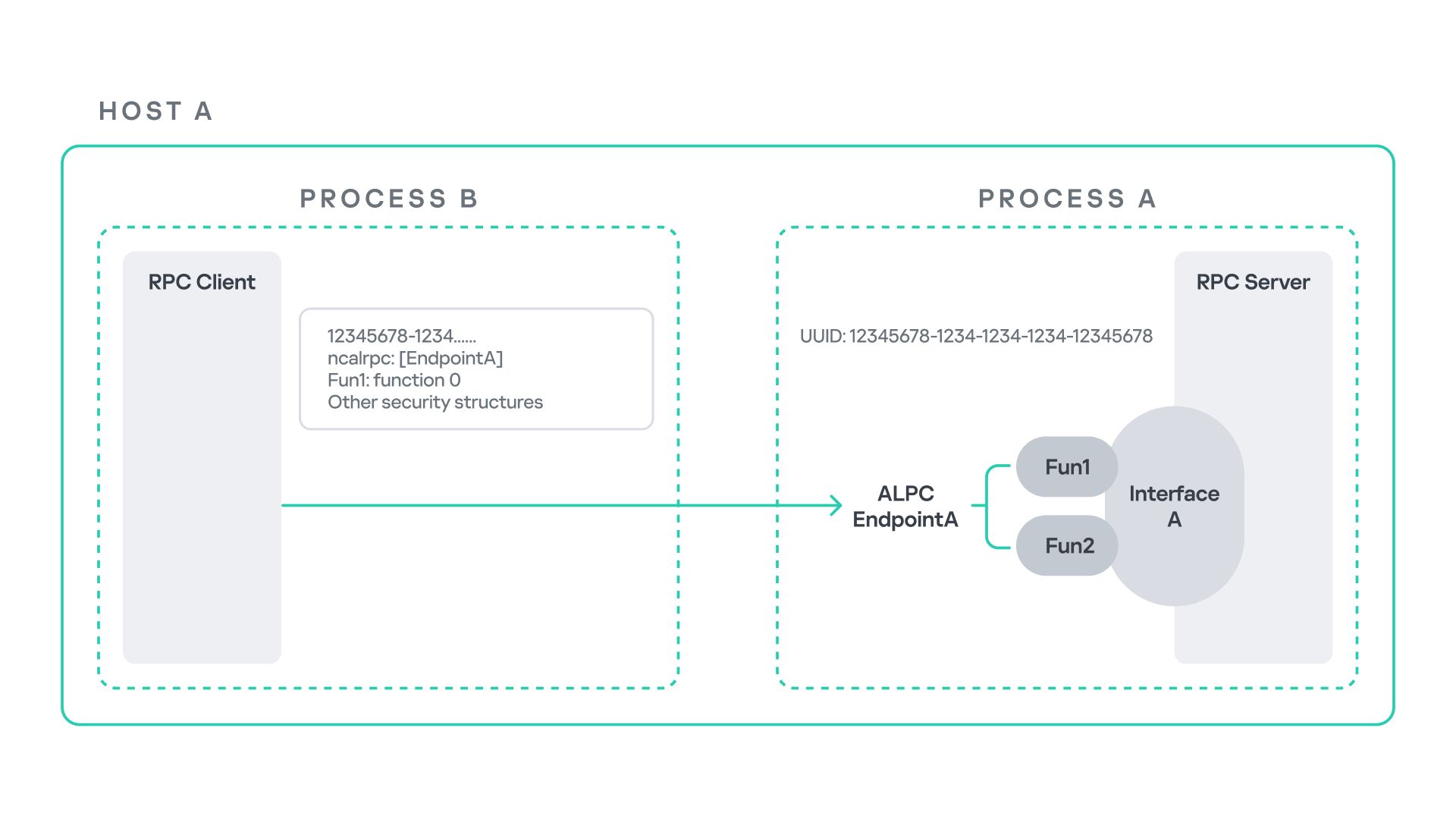
Microsoft RPC workflow
Windows Interprocess Communication (IPC) represents one of the most complex subsystems within the operating system. At the core of this ecosystem is the Remote Procedure Call (RPC) mechanism, which can operate either as a standalone communication channel or as a foundational transport layer for higher-level IPC technologies. In Windows, RPC enables communication between processes by allowing one process to invoke functions implemented in another, even when they execute in separate contexts.
Read the full version of the report on Securelist.com.
The proof-of-concept implementations can be found in the research repository.
Kaspersky advises organizations to take steps to detect and mitigate potential abuse:
Implement ETW-based monitoring. This allows defenders to identify RPC exceptions within their environment, particularly cases where RPC clients attempt to connect to unavailable servers. Monitoring such events can help administrators detect situations in which legitimate RPC servers are expected but not running. In some cases, the attack surface may be reduced by enabling the corresponding services, ensuring that legitimate RPC endpoints are available and limiting opportunities for attackers to deploy malicious servers that mimic them.
Limit the use of SeImpersonatePrivilege. This privilege should be restricted to processes that strictly require it. While some system processes depend on it for normal operation, it is sometimes granted to custom or third-party processes, which is generally considered poor security practice.
