The new release of Kaspersky Threat Intelligence (TI) unifies all vendors’ TI services, sources and cyber-reconnaissance capabilities in a single and convenient interface. The updated portal supports real-time search across various threat intelligence resources, including Kaspersky’s databases, Dark Web and Surface Web. New features include the visualization of cyber-investigations and extended opportunities for analysis of complex malicious objects.
Threat intelligence, which provides insights on the threat landscape and allows organizations to anticipate risks, has become one of the most evolving and in-demand specialties – as confirmed by IT security leaders’ surveys and market predictions. However, the diverse set of TI capabilities and the variety of available sources and services have made it difficult for security specialists to assemble a unified threat intelligence solution which matches their needs.
The renewed Kaspersky Threat Intelligence Portal[1] is a single pane of glass for threat intelligence. In addition to cyberthreat data, it also delivers validated information from external sources and new features that facilitate incident investigation as well as detection and attribution of previously unseen malicious objects.
Unified search across all threat intelligence resources
Kaspersky Threat Intelligence Portal now supports search across different sources[2], all in a single UI, making access to valuable insights easily accessible. Through real-time master search customers are able to get information across Kaspersky’s databases, including APT, crimeware, ICS and Digital Footprint Intelligence reports and actor profiles as well as across Dark Web, Surface Web and validated OSINT IoCs sources[3].
New Dark Web search offers instant access to insights from a comprehensive range of deep and dark web sources allowing organizations to get tailored evidence of planned attacks, discussions around vulnerabilities and successful data breaches in order to reduce the attack surface, secure online brand value and take appropriate actions.
To offer security practitioners a reliable source of information about global security events that can potentially or are already threatening company’s assets, brand or organization, Kaspersky Threat Intelligence Portal introduces Surface Web search. The service allows investigators to search for security-related news, discussions or other content across a validated range of relevant open web sources, such as theme-based newswires, blogs or forums.
Better visibility for in-depth investigation
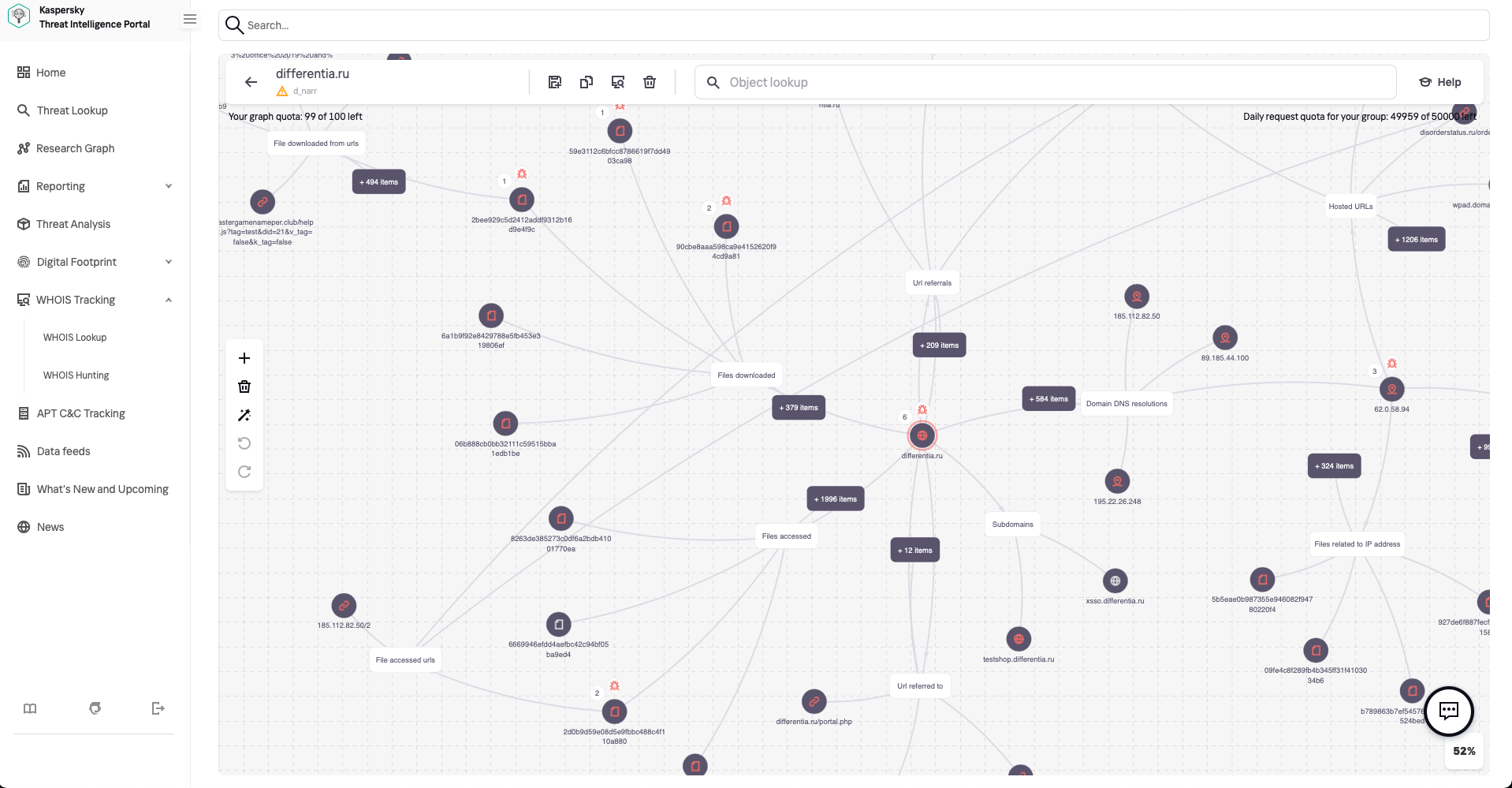
Graphical visualization is an extremely useful tool for researchers when they are looking for indicators and try to find connections between them. The Research Graph introduced in Kaspersky Threat Intelligence Portal is designed to explore data stored inside the portal, discover threat commonalities and generate new related IoCs. It provides a clear picture of the relationship between web addresses, domains, IP addresses, files and other context encountered during investigations. It also allows for an in-depth view of information without losing the context of the conducted investigation.
Complex threat analysis
Kaspersky Threat Intelligence Portal delivers a unified interface for complex file analysis via a merged “Threat Analysis” tab that leads to Cloud Sandbox and Threat Attribution Engine (TAE), which now runs completely in the cloud. The tab offers access to the results of Dynamic, Static, Anti-Virus and Attribution analysis for objects considered suspicious, offering enriched Threat Intelligence within a single place and providing a powerful tool for faster detection of previously unseen malicious objects.
“We see that customers are looking for a consolidated threat intelligence offering that, on the one hand, can deliver a holistic and global perspective on the threat landscape and, on the other, can fit their specific needs. Our renewed Threat Intelligence Portal meets these requirements as it unifies our unique and broad knowledge about threats with external threat data and allows companies to customize our offering by choosing services and sources that are most beneficial for their existing IT security function,” comments Anatoly Simonenko, Head of Technology Solutions Product Management at Kaspersky.
More information about Kaspersky Threat Intelligence Portal is available via this link.
[1] Kaspersky Threat Intelligence Portal provides a single point of entry to the following services: Threat Data Feeds, APT Intelligence Reporting, Crimeware Intelligence Reporting, ICS Threat Intelligence Reporting, Digital Footprint Intelligence, Threat Lookup, Threat Attribution Engine and Cloud Sandbox.
[2] Amount and types of search sources defined by licensing.
[3] URL, Domain and IP address IoC types will be available during 2022.
