Kaspersky Lab discovers the ancestor of Stuxnet and Flame – powerful threat actor with an absolute dominance in terms of cyber-tools and techniques
For several years, Kaspersky Lab’s Global Research and Analysis Team (GReAT) has been closely monitoring more than 60 advanced threat actors responsible for cyber-attacks worldwide. The team has seen nearly everything, with attacks becoming increasingly complex as more nation-states got involved and tried to arm themselves with the most advanced tools. However, only now Kaspersky Lab’s experts can confirm they have discovered a threat actor that surpasses anything known in terms of complexity and sophistication of techniques, and that has been active for almost two decades – The Equation Group.
According to Kaspersky Lab researchers the group is unique almost in every aspect of their activities: they use tools that are very complicated and expensive to develop, in order to infect victims, retrieve data and hide activity in an outstandingly professional way, and utilize classic spying techniques to deliver malicious payloads to the victims.
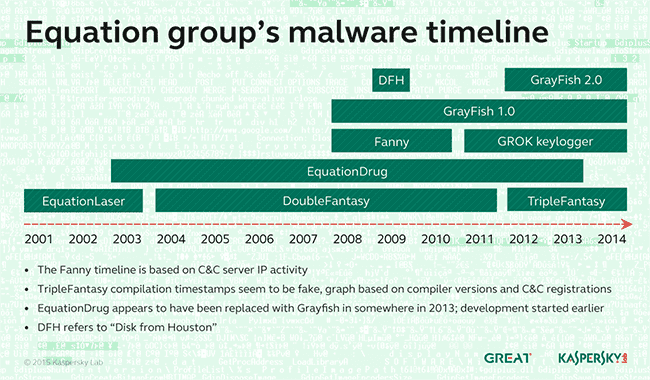
To infect their victims, the group uses a powerful arsenal of “implants” (Trojans) including the following that have been named by Kaspersky Lab: EquationLaser, EquationDrug, DoubleFantasy, TripleFantasy, Fanny and GrayFish. Without a doubt there will be other “implants” in existence.
WHAT MAKES THE EQUATION GROUP UNIQUE?
Ultimate persistence and invisibility
GReAT has been able to recover two modules which allow reprogramming of the hard drive firmware of more than a dozen of the popular HDD brands. This is perhaps the most powerful tool in the Equation group’s arsenal and the first known malware capable of infecting the hard drives.
By reprogramming the hard drive firmware (i.e. rewriting the hard drive’s operating system), the group achieves two purposes:
- An extreme level of persistence that helps to survive disk formatting and OS reinstallation. If the malware gets into the firmware, it is available to “resurrect” itself forever. It may prevent the deletion of a certain disk sector or substitute it with a malicious one during system boot.
“Another dangerous thing is that once the hard drive gets infected with this malicious payload, it is impossible to scan its firmware. To put it simply: for most hard drives there are functions to write into the hardware firmware area, but there are no functions to read it back. It means that we are practically blind, and cannot detect hard drives that have been infected by this malware” – warns Costin Raiu, Director of the Global Research and Analysis Team at Kaspersky Lab. - The ability to create an invisible, persistent area hidden inside the hard drive. It is used to save exfiltrated information which can be later retrieved by the attackers. Also, in some cases it may help the group to crack the encryption: “Taking into account the fact that their GrayFish implant is active from the very boot of the system, they have the ability to capture the encryption password and save it into this hidden area,” explains Costin Raiu.
Ability to retrieve data from isolated networks
The Fanny worm stands out from all the attacks performed by the Equation group. Its main purpose was to map air-gapped networks, in other words – to understand the topology of a network that cannot be reached, and to execute commands to those isolated systems. For this, it used a unique USB-based command and control mechanism which allowed the attackers to pass data back and forth from air-gapped networks.
In particular, an infected USB stick with a hidden storage area was used to collect basic system information from a computer not connected to the Internet and to send it to the C&C when the USB stick was plugged into a computer infected by Fanny and having an Internet connection. If the attackers wanted to run commands on the air-gapped networks, they could save these commands in the hidden area of the USB stick. When the stick was plugged into the air-gapped computer, Fanny recognized the commands and executed them.
Classic spying methods to deliver malware
The attackers used universal methods to infect targets: not only through the web, but also in the physical world. For that they used an interdiction technique – intercepting physical goods and replacing them with Trojanized versions. One such example involved targeting participants at a scientific conference in Houston: upon returning home, some of the participants received a copy of the conference materials on a CD-ROM which was then used to install the group’s DoubleFantasy implant into the target’s machine. The exact method by which these CDs were interdicted is unknown.
INFAMOUS FRIENDS: STUXNET AND FLAME
There are solid links indicating that the Equation group has interacted with other powerful groups, such as the Stuxnet and Flame operators – generally from a position of superiority. The Equation group had access to zero-days before they were used by Stuxnet and Flame, and at some point they shared exploits with others.
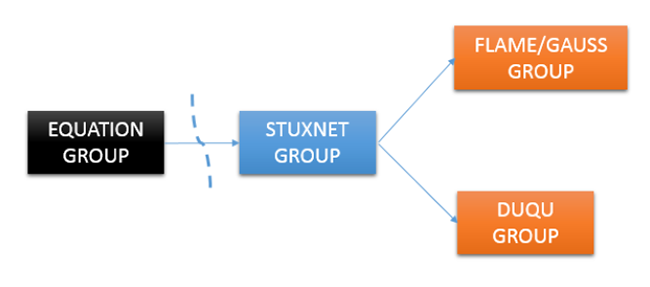
For example, in 2008 Fanny used two zero-days which were introduced into Stuxnet in June 2009 and March 2010. One of those zero-days in Stuxnet was actually a Flame module that exploits the same vulnerability and which was taken straight from the Flame platform and built into Stuxnet.
POWERFUL AND GEOGRAPHICALLY DISTRIBUTED INFRASTRUCTURE
The Equation group uses a vast C&C infrastructure that includes more than 300 domains and more than 100 servers. The servers are hosted in multiple countries, including the US, UK, Italy, Germany, Netherlands, Panama, Costa Rica, Malaysia, Colombia and Czech Republic. Kaspersky Lab is currently sinkholing a couple dozen of the 300 C&C servers.
THOUSANDS OF HIGH-PROFILE VICTIMS GLOBALLY
Since 2001, the Equation group has been busy infecting thousands, or perhaps even tens of thousands of victims in more than 30 countries worldwide, covering the following sectors: Government and diplomatic institutions, Telecommunications, Aerospace, Energy, Nuclear research, Oil and Gas, Military, Nanotechnology, Islamic activists and scholars, Mass media, Transportation, Financial institutions and companies developing encryption technologies.
DETECTION
Kaspersky Lab observed seven exploits used by the Equation group in their malware. At least four of these were used as zero-days. In addition to this, the use of unknown exploits was observed, possibly zero-day, against Firefox 17, as used in the Tor browser.
During the infection stage, the group has the ability to use ten exploits in a chain. However Kaspersky Lab's experts observed that no more than three are used: if the first one is not successful, they try with another one, and then with the third one. If all three exploits fail, they don't infect the system.
Kaspersky Lab products detected a number of attempts to attack its users. Many of these attacks were not successful due to Automatic Exploit Prevention technology which generically detects and blocks exploitation of unknown vulnerabilities. The Fanny worm, presumably compiled in July 2008, was first detected and blacklisted by our automatic systems in December 2008.
To learn more about the Equation Group, please read the blog post available at Securelist.com.
