Anastasiya Kazakova, Public Affairs Manager
The policy framework on critical infrastructure protection (CIP) in the European Union (EU) is one of the world’s most advanced. It relies on:
- 2006 European Programme of Critical Infrastructure Protection (EPCIP), which gives the Commission the legal basis and solid framework to support Member States in protecting their own national critical infrastructure (CI);
- 2008 Directive on European Critical Infrastructure (ECI Directive), which outlines a general approach to CIP and prescribes identifying and designating European CI (ECI). It also requires developing operator security plans; threat assessments; reports on risks, threats and vulnerabilities identified; as well as carrying out and maintaining communication between relevant Member State authorities and Security Liaison Officers, which need to be appointed as points of contact for security-related issues between ECI operators and the competent authorities.
Since the ECI direction applies only to the energy and transportation sectors, we also identify an additional legal instrument:
- 2016 Network and Information Systems (NIS) Directive, which applies to seven sectors, including transportation and energy. The NIS Directive prescribes identifying operators of essential services (OES) meeting certain criteria, and implementing for both OES and digital service providers (DSPs) a range of NIS security requirements, including technical and organizational measures for incident notification. The NIS Directive established a Cooperation Group and EU CSIRT network to enhance strategic cross-border cooperation between EU Member States, the Commission, nationally designated CSIRTs, and the EU Agency for Cybersecurity (ENISA).
Last year the ECI Directive was subject to an external evaluation, after which the Directorate-General of the European Commission (DG HOME) published a Staff Working Document. In 2019, Directorate-General for Communications Networks, Content and Technology (DG CONNECT) published a report assessment of the NIS Directive’s effectiveness, which revealed gaps in consistency in the application of the Directive by Member States and concluded that fragmented application across the EU ‘can have a negative impact on the level playing field in the internal market and potentially render entities more vulnerable’ to cyberthreats. Based on that, the newly established Commission announced a review of the NIS Directive scheduled for Q4 2020.
From that perspective, the least helpful advice for policy makers wishing to improve the CIP policy framework would certainly be to leave the situation as it is. But what would be good to advice then?
Suggestions for strengthening the CIP policy framework in the EU
Apparently, since the first legal instruments were created, the threat landscape risking the integrity and security of CI in Europe has significantly changed. In particular, the rapid development of emerging technologies have the potential to dramatically impact the EU’s CIP:
- machine learning enables sophisticated and malicious attacks with the ability to learn and adapt to compromise systems with minimal chances of detection;
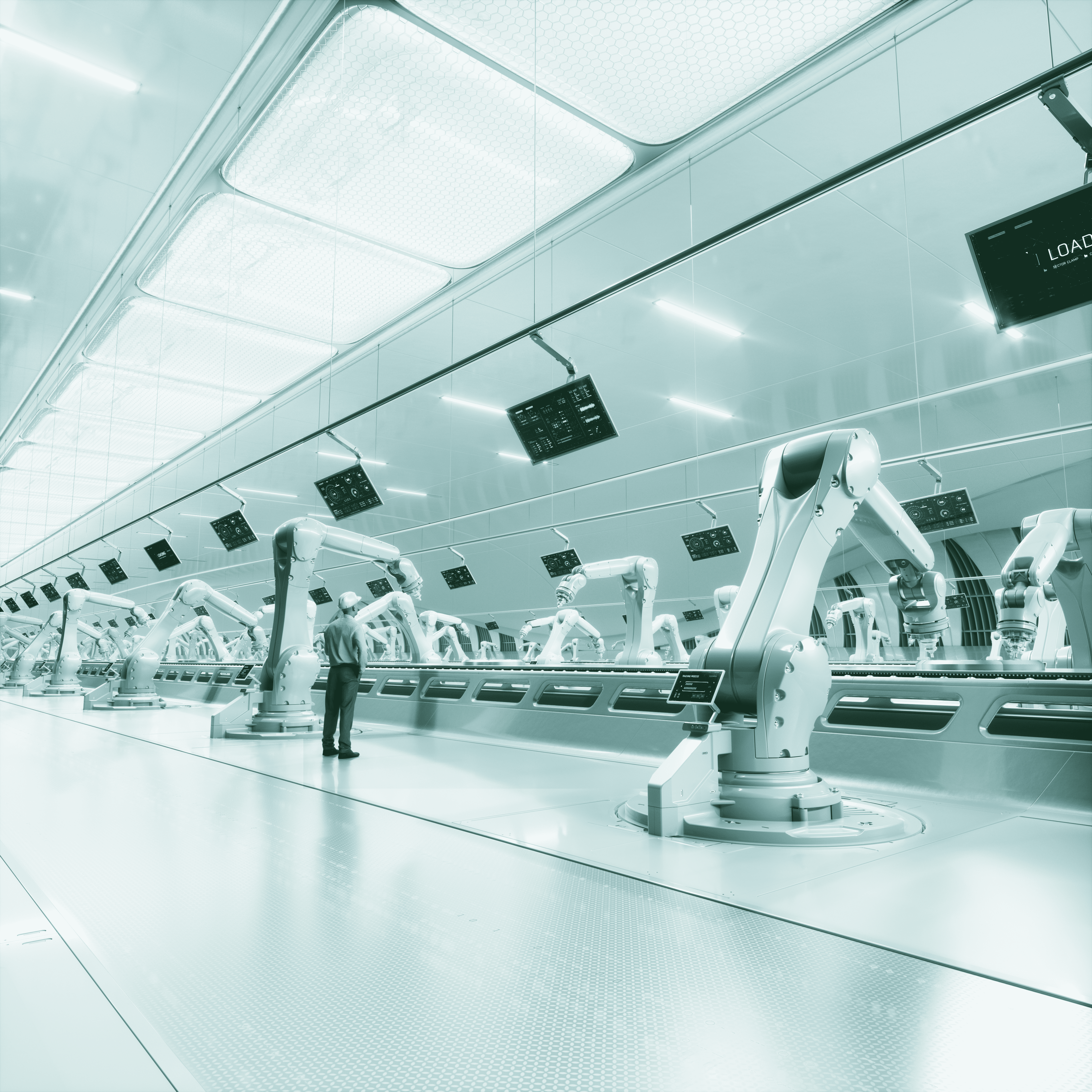
- interconnected devices, sensors and systems (the Internet of Things) embedded in smart cities and smart industries create a new target for malicious actors to compromise critical infrastructure or services guaranteeing public and social wellbeing;
- distributed ledger technologies continue to be attractive targets for criminal attacks, which not only result in criminal profits, but cause severe reputational damage to the victims and undermine confidence in the financial sector as a whole;
- with a growing reliance on cloud computing and related systems and data services, the number of attacks targeting vulnerabilities in these technologies increases as well;
- quantum computing raises questions regarding the security of modern cryptography and encryption methods.
In this regard, we welcome the European Commission’s decision to develop a new proposal on CIP and conduct a review of the NIS Directive to adjust both legal instruments to new threats and risks. To support this process, we share the following suggestions to strengthen the CIP policy framework in the EU. In particular, we recommend actions for:
- Enhancing critical infrastructure cybersecurity through:
- A government-industry supply-chain-security task force to identify best practices, guidelines and lessons learned for secure technology procurement, and evaluation of ICT suppliers’ trustworthiness and integrity;
- Transparent vulnerability management programs to ensure the integrity of CI by ensuring operators can fix vulnerabilities before they are exploited by hostile actors;
- Private-to-government (including government-to-government and private-to-private) threat information sharing about cybersecurity threats, vulnerabilities, and incidents, including with affected parties and companies capable of developing means to develop remediation plans against attacks. The information sharing should be voluntary, and with legal protections for vendors, operators and companies against legal liability or regulatory consequences.
- Achieving full harmonization in the implementation of the CIP policy framework across EU Member States through:
- Creating common data hubs/portals for competent authorities and industry with mapping of national security measures, definition, incident notification and incident reporting procedures;
- Developing thresholds, requirements and templates for incident notification and incident reporting – harmonized across Member States;
- Achieving synchronization of the NIS Directive and ECI Directive in terms of security requirements for CI operators, vendors and competent authorities.
A detailed position paper can be found here.
Following also the conclusions made in the 2019 Staff Working Document that ECI and NIS Directives, we believe that it could be necessary to explore advantages for aligning both directives into a single legal instrument for greater harmonization. A single policy legal instrument on CIP would be central to outlining the holistic approach with regard to CI sectors and their risk profiles, security technical and organizational measures, and mechanisms for deepening cross-border cooperation in the EU.
