
World War II information security: Navajo VPN
During WW2 modern cryptography principles were often coupled with ‘amateur’ ciphering methods. Curiously, the latter ones often proved to be equally reliable
1393 articles

During WW2 modern cryptography principles were often coupled with ‘amateur’ ciphering methods. Curiously, the latter ones often proved to be equally reliable

The necessity of a product that is positioned in-between the enterprise-level suites and home-users solutions became apparent only a few years ago.

The global workforce is increasingly going mobile: 37% currently, up to 50% by 2020. There are more actively used mobile devices in any more or less developed country than there are adult citizens, so clearly “mobility” is something related to us all.

With so many games and apps available for download on your mobile devices, it’s important to remember that not all of them are suitable for children. That’s why you should be monitoring what your kid installs.

Security is a tough matter for small businesses for multiple reasons; startups and small entities tend to save on their IT wherever possible, and that’s where security failures are common.

Recently Interpol, Microsoft and Kaspersky Lab revealed and the shut down of a huge botnet which zombified about 770,000 PCs worldwide. Check this story out and then check your PC

Over the last few years we have witnessed a number of high-profile, large scale security breaches with quite dramatic consequences, such as massive leaks of personally identifiable data.

As cybercrime keeps focusing on profit, the share of plainly malicious spam, spreading out Trojans, phishing links, etc., will grow.

Figures show that just 58% of Android-based smartphones and 63% of Android tablets are protected by any kind of an anti-virus solution, while 31% of smartphones and 41% of tablets are not even password-protected.

There are several ways to avoid phishing attacks on your Facebook account. The common theme in each is to be highly suspicious of any online request for your personal information

Losing a phone is always a bit of a nuisance, especially if it’s an expensive piece of hardware. With smartphones conquering the world with authority, losing a phone means also

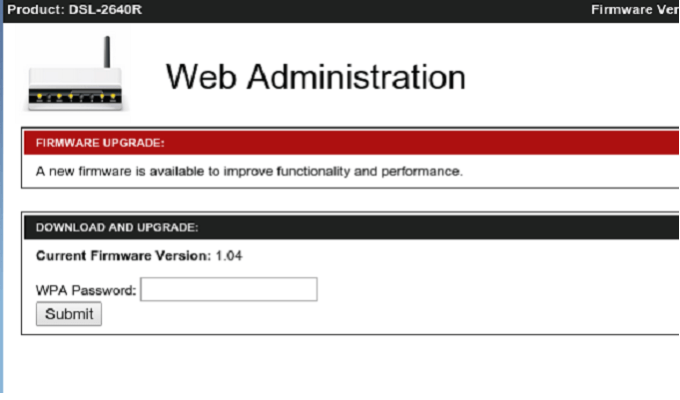
A large-scale “pharming” campaign targeting home routers took place in South America, the latest in a trend Kaspersky Lab’s experts have been monitoring for awhile. Home routers are frequently used

Fraudsters hacked Skype and tricked people from a contact list to send them about $5,000 over the course of a few days. Skype support, local banks and the police refused to do anything.

Windows 10 will offer users the ability to authenticate themselves with biometric identifiers rather than passwords

During my first two weeks of the biochip experience I had time to mull over a lot of things. In this post I’m going to touch upon the subject of form factor.

New allegations against the NSA claim the group hacked into the network of the world’s largest SIM card provider, stealing encryption keys to millions of devices.

The story of how a biochip was implanted into my hand and why I needed it.

One dollar lesson is a new interactive project by Kaspersky Lab that aims to help you stay protected from online money frauds. Learn three simple lessons right now!

It turned out that Lenovo’s laptops had been shipped with an adware called Superfish. It possibly allows eavesdropping on encrypted connections
Today we discuss the most important news on information security from January.

A malware that cannot be wiped from the victim’s hard drive does exist. However, it’s so rare and expensive, that you probably won’t ever encounter it.