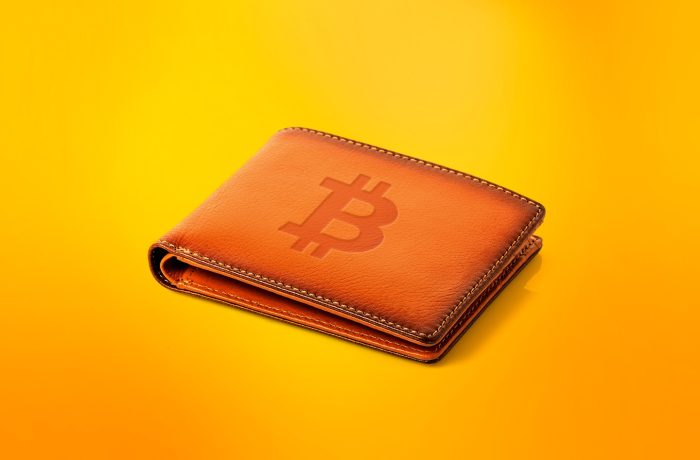
Crypto thieves ramping up attacks on Apple users
We’ve discovered over two dozen phishing apps mimicking popular crypto wallets right in the official App Store. Here’s a breakdown of the new waves of attacks targeting iPhone and Mac users and their crypto holdings.
 iOS
iOS
 AI
AI


 open-source
open-source

 backup
backup

 supply chain
supply chain
 phishing
phishing

 Education
Education