
Switcher hacks Wi-Fi routers, switches DNS
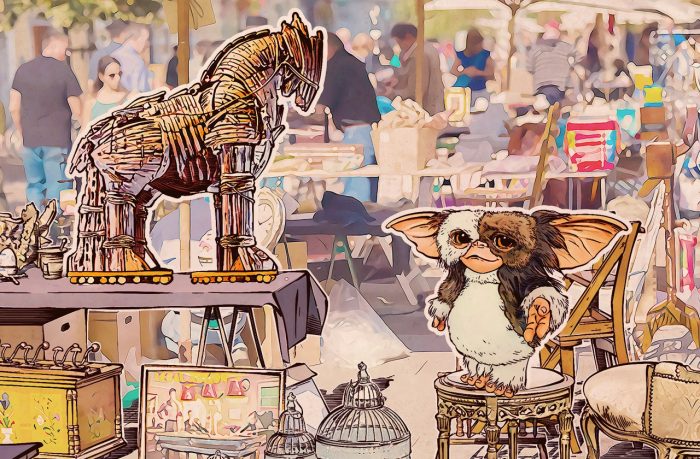
An unconventional Android Trojan does not do anything to your smartphone; instead it hacks the Wi-Fi hotspot the smartphone is connected to.
1391 articles

An unconventional Android Trojan does not do anything to your smartphone; instead it hacks the Wi-Fi hotspot the smartphone is connected to.

Everything you need to know about botnets: how they work, why they are dangerous and how to stay safe.

More than 70% of active Internet users have considered quitting their social networks. What do they have to lose?

Router manufacturers and ISPs are trying to make Wi-Fi set up as easy as possible — and in the security business, we know e-a-s-y spells trouble.

Facebook regularly changes its security settings. Take a look: A useful new setting may have appeared since the last time you checked.

An unwitting army of connected devices caused an insane disruption of major Internet sites. IoT users need to wise up.

Who is responsible when connected devices go on a crime spree?

Careless behavior online can have devastating personal and financial consequences. Here are seven common shortcuts to avoid.

ATMs will soon use fingerprint readers and iris sensors to identify customers. But is biometric authentication as secure as advertised?

Everything you need to know about mobile banking Trojans and how to fight them.

What are older people doing online, and are they aware of the threats out there?

Virtual Desktop Infrastructure is now standard in many organizations. It is as much necessary to set up proper security for virtual systems as it is for the physical infrastructure.

i-Dressup, a community for teenage girls, is actively leaking passwords in plain text.

We have more bad news from the Yahoo hack: Even without a yahoo.com account, you may be at risk.

How criminals use fake Wi-Fi hotspots to steal data, and how you can use our solutions to protect yourself.

Yahoo is expected to announce a “massive” data breach soon. Although the news is not yet confirmed, you should be proactive and check the security of your Yahoo account.

How heuristic analysis and System Watcher work in Kaspersky Internet Security.

Why questions like “What is your mother’s maiden name?” and “What did you do last summer?” don’t protect you.

Our experts recently discovered an app called Guide for Pokémon Go distributed via Google Play. It looks like a single app created to help players of the much-hyped gaming title. But a little while after it’s installed, the app roots the device. Rooting makes the malware capable of installing and deleting additional apps.

Kaspersky Lab’s senior vice president of IT dispenses essential cybersecurity advice for small businesses.