
Mobile banking Trojans, explained
Everything you need to know about mobile banking Trojans and how to fight them.
1402 articles

Everything you need to know about mobile banking Trojans and how to fight them.

What are older people doing online, and are they aware of the threats out there?

Virtual Desktop Infrastructure is now standard in many organizations. It is as much necessary to set up proper security for virtual systems as it is for the physical infrastructure.

i-Dressup, a community for teenage girls, is actively leaking passwords in plain text.

We have more bad news from the Yahoo hack: Even without a yahoo.com account, you may be at risk.

How criminals use fake Wi-Fi hotspots to steal data, and how you can use our solutions to protect yourself.

Yahoo is expected to announce a “massive” data breach soon. Although the news is not yet confirmed, you should be proactive and check the security of your Yahoo account.

How heuristic analysis and System Watcher work in Kaspersky Internet Security.

Why questions like “What is your mother’s maiden name?” and “What did you do last summer?” don’t protect you.

Our experts recently discovered an app called Guide for Pokémon Go distributed via Google Play. It looks like a single app created to help players of the much-hyped gaming title. But a little while after it’s installed, the app roots the device. Rooting makes the malware capable of installing and deleting additional apps.

Kaspersky Lab’s senior vice president of IT dispenses essential cybersecurity advice for small businesses.

What if you have to transmit sensitive data and the only connection is open Wi-Fi? We’ve got you covered.

We asked more than 3,000 representatives of small and medium-sized companies how they manage to cope with cryptomalware in the constantly changing landscape of cyberthreats.

What lessons can businesses learn from the story of our investigation of the activity of the Lurk gang?

Evgeny Chereshnev, professional cyborg, talks about fascinating new jobs that will emerge in the near future.
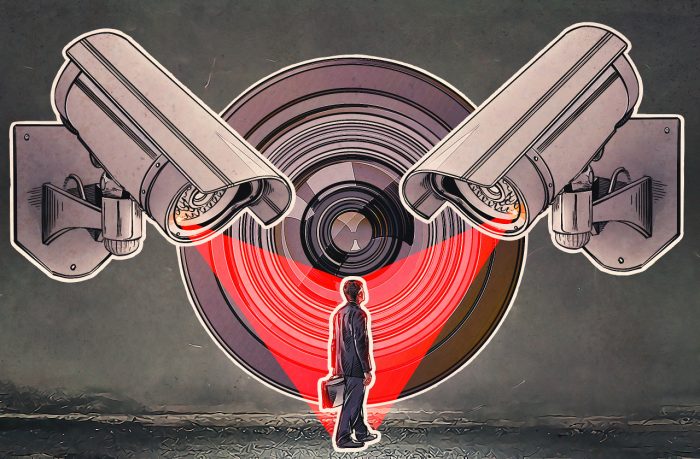
Lynch law, loss of basic privacy, disgusting marketing, digital identity theft — how else can facial recognition be misused?

If you own an Apple device, spend a few minutes setting up your System Location Services. You’ll protect your privacy and lengthen battery life.

Kaspersky Lab’s security experts released a detailed report on Operation Ghoul – a targeted campaign aimed primarily at businesses in the Middle East and Europe.

The changeover from magnetic stripe cards to chip cards cost millions of dollars but promised greater security. At Black Hat 2016, researchers told us that the new cards are nonetheless insecure.

Short-term rental sites are great for travelers and homeowners. The Wi-fi? Maybe not so much.
