
Why electronic payments get attacked?
While fast and convenient, electronic payments are a risky matter if not secured properly.
1182 articles

While fast and convenient, electronic payments are a risky matter if not secured properly.

WhatsApp has finally released a Web version of its popular mobile messaging service. We take a look at it from the security perspective.

New version of CTB-Locker, a ransomware that uses Tor and Bitcoin to evade detection and takedowns, should be avoided at all costs.

What is the best way to start assessing your company’s cybersecurity issues? First, look around at what you have.
We collected the 10 best tweets related to an IT security event in 2014.

Gaming is enormously popular. Thus, it’s an easy target for cybercriminals looking for a never-ending source of money.

We have constructed a list of promises that you should make to yourself this year to stay safe both online and offline.

The number of corporate-targeting attacks increased this year more than two times compared to 2013. Why?
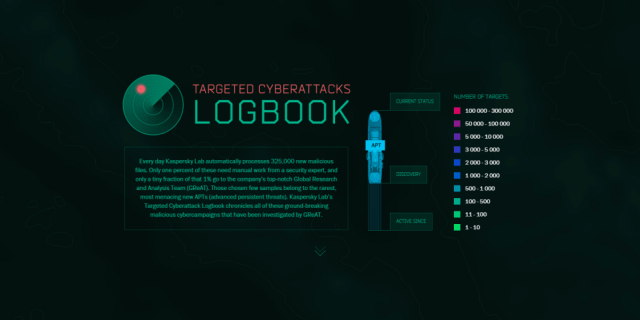
Kaspersky Lab launches “Targeted Attacks Logbook” – a visual tool to monitor known Advanced Persistent Threats. In this post, we take a look at how to handle this pretty instrument.

Kaspersky Lab experts shared their predictions on the evolution of APT. While these predictions may not come true, they are based on facts and trends already observed.

Applying the incorrect settings to your router may lead to serious problems. Here is a short guide to protecting your home Wi-Fi network.

Kaspersky Lab experts analyze the security and privacy trends that emerged in 2014, including anonymous Tor browsing, ransomware, APT attacks and more.

Kaspersky Lab experts make predictions about what trends will emerge in the security industry in 2015.

Ransomware is a common and much-feared problem. Here are ten facts to help in dealing with it.

Kaspersky Lab has gathered stats on the cyberthreats in 2014. The figures are appalling, but they don’t spell out doom and gloom. It is all about awareness.

Disgruntled ex-employees don’t need to have special hacking skills to inflict severe damage on the company infrastructure. Cynthia James reviews a number of scenarios, and ways to prevent attacks of this kind.

Cybercrime is a rather lucrative business. Cybercriminals are earning a lot, or at least their effort-to-profit rate is good enough for them to keep going. But how good is it?

Today’s information technologies are a rather mishmashed system comprised of top-notch innovations interspersed with legacy technologies, some of which have been in use for decades and rarely changed. This “coexistence” of new and old led to the discovery of dramatic bugs that had stayed below the radar for years.

Let’s take a moment to discuss the numerous troubles that our bright, technology-packed future could bring about.

Kaspersky Lab released its new IT Threat Evolution Q3 2014 report, dedicated to the most important security incidents and trends in the cybersecurity sphere. It may seem like attacks are increasing more rapidly than ever, but it’s detection rates that are growing.

Recent news concerning “hacked webcams” or “breached baby monitors” appears to be all over the place. Let’s take a closer look at the situation.