Cybercrime is a rather lucrative business. The number of threats is growing steadily, from meager one-off attacks to global scale APT campaigns. It’s safe to assume that cybercriminals are earning a lot, or at least their effort-to-profit rate is good enough for them to keep going. But how good is it?
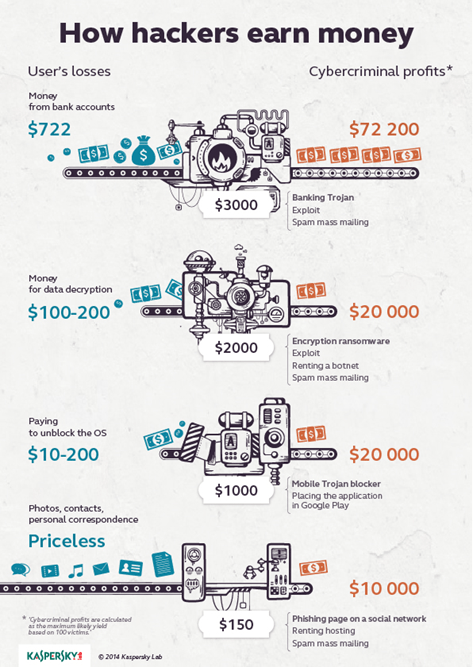
Cybercriminals could be raking in profits up to 20 times greater than the cost of their attacks, according to figures compiled by Kaspersky Lab experts: They compared the cost of the most frequently used hacker tools with the money stolen in a successful malicious operation.
Cybercrime, Inc.: how profitable is the business?
Tweet
It’s important to note that cybercriminals don’t need to be “high-tech” or particularly tech savvy. They don’t even need to have a “script-kiddie” level of cyberskills. All of the tools they require are available at reasonable cost.
“Buying malware is currently not a problem: it’s easy to find them on various hacker forums, and they are relatively cheap, making them attractive,” says Alexander Gostev, Chief Security Expert at Kaspersky Lab.
According to the research, creating a phishing page to mimic a popular social network and setting up a spam mass email that links to the fake site currently costs an average of $150. If the criminals catch 100 people they can net up to $10,000 by selling sensitive data. The victims, in turn, lose their valuable contacts, personal photos, and messages.
A mobile Trojan blocker is much more expensive. It costs, on average, $1000 to buy and distribute the malware. However, the payoff is quite large. The prices that the attackers set for unblocking a smartphone vary from $10 to $200, which means that from 100 potential victims they can get up to $20,000.
Using encrypted ransomware can earn the same, although the “initial investment” will be twice as high – about $2,000. The users’ losses are also higher because the minimum sum of the ransom requested by the fraudsters for decrypting the data is usually $100 per user. Organizations would have to pay much more.
Ransomware is more harmful to its victims on a psychological level: a measly piece of malware that reveals a back-alley criminal isn’t a great experience, especially for smaller businesses.
The most profitable threat is banking Trojans that target money directly. They are pricey, too: about $3,000 per malware, which exploits via spam emails. But in the end, criminals can earn up to $72,000. The average loss for an individual victim – whether it is a person or a business organization – is $722.
Up to 20:1 – that’s the rate of profit to effort from cybercrime these days. However, while the number of cyberattacks in general keeps growing so does public awareness. So certain attacks become obsolete and useless, and criminals have to change tactics, turning their attention to higher-level targets.
Financially-motivated cybercriminals are increasingly adopting #APT-style tactics
Tweet
Some changes have already occurred. According to the latest study, financially-motivated cybercriminals are increasingly adopting APT-style tactics. This trend also means that businesses will primarily be in cybercriminals’ crosshairs.
Also, attacks against ATMs seemed to explode this year, because of frail physical security and the fact that a large number of them still run Windows XP. Microsoft dropped its support of the operating system this past spring.
In 2015 Kaspersky Lab experts expect to see criminals compromising the networks of banks and using that level of access to manipulate ATM machines in real time. In other words, rather than attack individual ATMs, they will attempt to compromise the “brains” of ATM networks: banks.
Another short-range prediction by Kaspersky Lab experts warns about the possibility of attacks against virtual payment systems. They are being increasingly adopted around the world.
How profitable these expected attacks will be depends on how security-aware the targeted organizations are, and whether they would prefer to save on security or take the risks hoping they will not be attacked.
 cybercrime
cybercrime

 Tips
Tips