
This Year in Cybersecurity
2013 will be remembered by both security professionals and everyday people for the number of events that took place in information security. Various incidences, from Edward Snowden’s revelations to the
357 articles

2013 will be remembered by both security professionals and everyday people for the number of events that took place in information security. Various incidences, from Edward Snowden’s revelations to the
The Problem We often hear from small business owners that the modest size of their companies provides them with “invisibility protection”. Employees believe that their organization and its activities are

Neverquest is a new banking trojan that spreads itself via social media, email and file transfer protocols. It possesses the capacity to recognize hundreds of online banking and other financial

DDoS attack without head… A powerful and very unusual DDoS attack was discovered in mid-October. The attack was unusual in that it employed a version of the Phantom JS headless

There is an all-too common misconception that in order to become infected with web-propagated malware, you must visit sketchy parts of the Internet’s underbelly or a website within that broad

Sending off emails laden with malicious attachments is one of the most effective and widely relied upon methods for disseminating malware and infecting user-machines. It’s tried and it’s true.

Bitcoin is a digital crypto-currency. It’s distributed. It’s peer-to-peer, meaning that is controlled by the people that use it. There is no central authority controlling it. There are no international

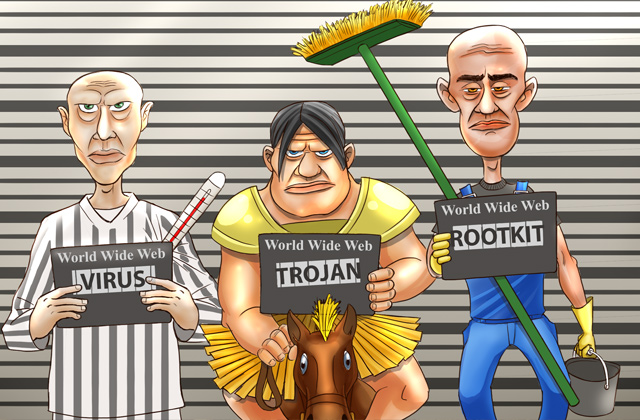
Thousands of new viruses, Trojans, and other malicious programs appear every day. The information about these threats and ways of neutralizing them is contained in the databases of Kaspersky Internet

It’s that time of month again when we catch you up on anything you may have missed in October. So take a peek at some of our top posts from
Do companies need to take care of their personnel’s IT education today? This issue is controversial because on the one hand it is quite difficult to find people nowadays who
At Kaspersky, we take our responsibility to keep you guarded against attacks very seriously, which is why we’re continuously familiarizing you with the latest methods that are out there and

In most cases, the “free” Android applications you download from Google’s Play store aren’t free at all. These developers aren’t just developing apps for you out of the kindness of

Kurt Baumgartner, targeted attack expert and the principle security researcher at Kaspersky Lab, sat on a panel discussing how the global market for trafficking financial information has changed, how it
The question of ordinary users’ awareness of cyber threats and the scope of their knowledge about them may seem philosophical or rhetorical, but only at first glance. The results of

September has come to an end and it’s time to check up on the progress that has been made by police forces and security experts in finding hackers and cybercriminals

Online shopping, online money transfers and online banking save us a lot of time and make our lives easier. However, these same technologies also make life easier for cybercriminals by
What kind of corporate network would be considered secure? Primarily one that is controlled by its operators, or in other words, a network in which the system administrator knows where,
Although we usually talk about the ways to protect information from threats, today we are going to list several proven and popular ways to lose data and, possibly, even money.
Today’s malware is definitely not the only security threat for individual and corporate users, but the tools of detecting and fighting malware remain fundamental in any security solution. There are

The ability of Kaspersky Lab products to protect and secure online financial transactions has earned an AV-Test Innovation Award. The award was given based on Kaspersky Lab’s Safe Money technology,

A modern man cannot imagine his life without mobile devices like smartphones and tablet computers. A portable minicomputer that provides access to the Internet and offers basic features for processing