
Trending cyberthreats at the Olympic Games
How to keep your money and data safe during the 2016 Olympics: All of the risks you need to know about, in one post.
691 articles

How to keep your money and data safe during the 2016 Olympics: All of the risks you need to know about, in one post.

You aren’t the only one to catch the PokémonGo craze. So have criminals.

An Indian-speaking threat actor, Dropping Elephant chooses targets mainly in the Asian region, paying particular attention to Chinese government/diplomatic organizations – and also to foreign embassies and diplomatic offices in China.

A new APT group is seen to have been exploiting hotpatching, a now-deprecated feature in Windows operating systems, to carry out their attacks.

Do you know how many companies are actually tracking you when you visit a single website? The answer may surprise you.

Locky and Petya ransomware strains took the world by storm when they shouldn’t be successful at all.

Instead of writing their own malicious tools, criminals are increasingly using the off-the-shelf malware, and more and more often – totally legitimate software.

Internet-trolls are back in the game: 2ch anonymous hacked hundreds devices and streamed video from victims’ homes for the kick of it.

We talk about ever-present connectivity. What does that mean for raising kids?

Users also want and expect access to data 24/7, with no barriers or lag times.

Kaspersky Lab has developed a new solution to provide industrial cybersecurity – Kaspersky Industrial CyberSecurity.

They say Facebook severely violates users’ privacy. Is it true and why European authorities claim that?

As new technologies become increasingly pervasive, we are starting to reconsider our vision of many things. Kaspersky Lab CMO Alexander Erofeev contemplates the ways the Internet transforms our views on privacy.

While the popular notion is that Macs are virus-proof, it is actually quite a myth. These computers can catch viruses and Ransomware.
Kaspersky Lab launches two new enterprise solutions for preventing the most sophisticated cyberthreats organizations encounter worldwide.

Targeted attacks are visibly commoditizing, choosing cost efficiency over sophistication. If a combination of social engineering, tweaks to widely-available malware and legit apps can do the trick, why bother to create something original and exquisite?

At The SAS 2016, Kaspersky Lab researchers discussed the newly discovered Poseidon Group. A custom APT boutique chasing commercially valuable data

Tax season means that more folks than the IRS are after your money.

We all know that security is low on the IoT totem pole. However, here’s to hoping these 5 items stay secure.

Late in December, the term “whaling” mildly spiked in cybersecurity-related media outlets. The term isn’t exactly new, but it isn’t encountered as often as “phishing”.

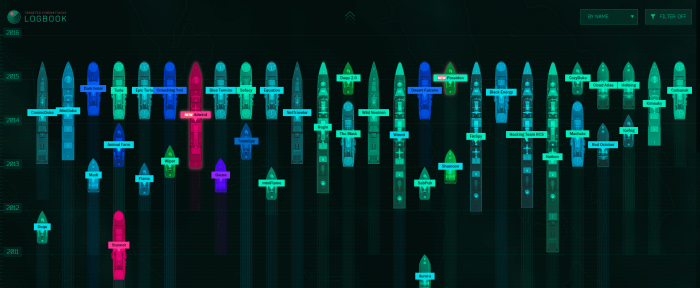
Konstantin Goncharov recaps the most significant security events of 2015.