Today, Kaspersky Lab launches two new enterprise solutions for preventing the most sophisticated cyberthreats organizations encounter worldwide: The Kaspersky Anti Targeted Attack Platform and Kaspersky Security Intelligence Services.
A Logbook and a Turning Point
In late 2014, Kaspersky Lab launched its targeted attacks monitoring tool – APT Logbook. If we took a look at it today, it would look like a picket fence:
More and more new attacks are getting discovered and analyzed, and who knows how many are out there still undetected.
2015 marked a turning point for organizations around the globe: perimeter defense alone isn’t sufficient enough to ensure reliable protection. It is something that businesses worldwide were investing for years, and protecting the boundaries from generic attacks remains important, but now businesses also need to be able to detect a targeted or advanced cyberattack in progress as well as predict future attacks.
And that’s where a number of challenges are encountered.
Rising trends
First of all, enterprises’ infrastructure sophistication is growing steadily, which makes it an issue to keep all of its parts visible and gather operational data at once if something goes wrong.
Attacks themselves are not a one-off event: these are processes taking place over extended periods of time.
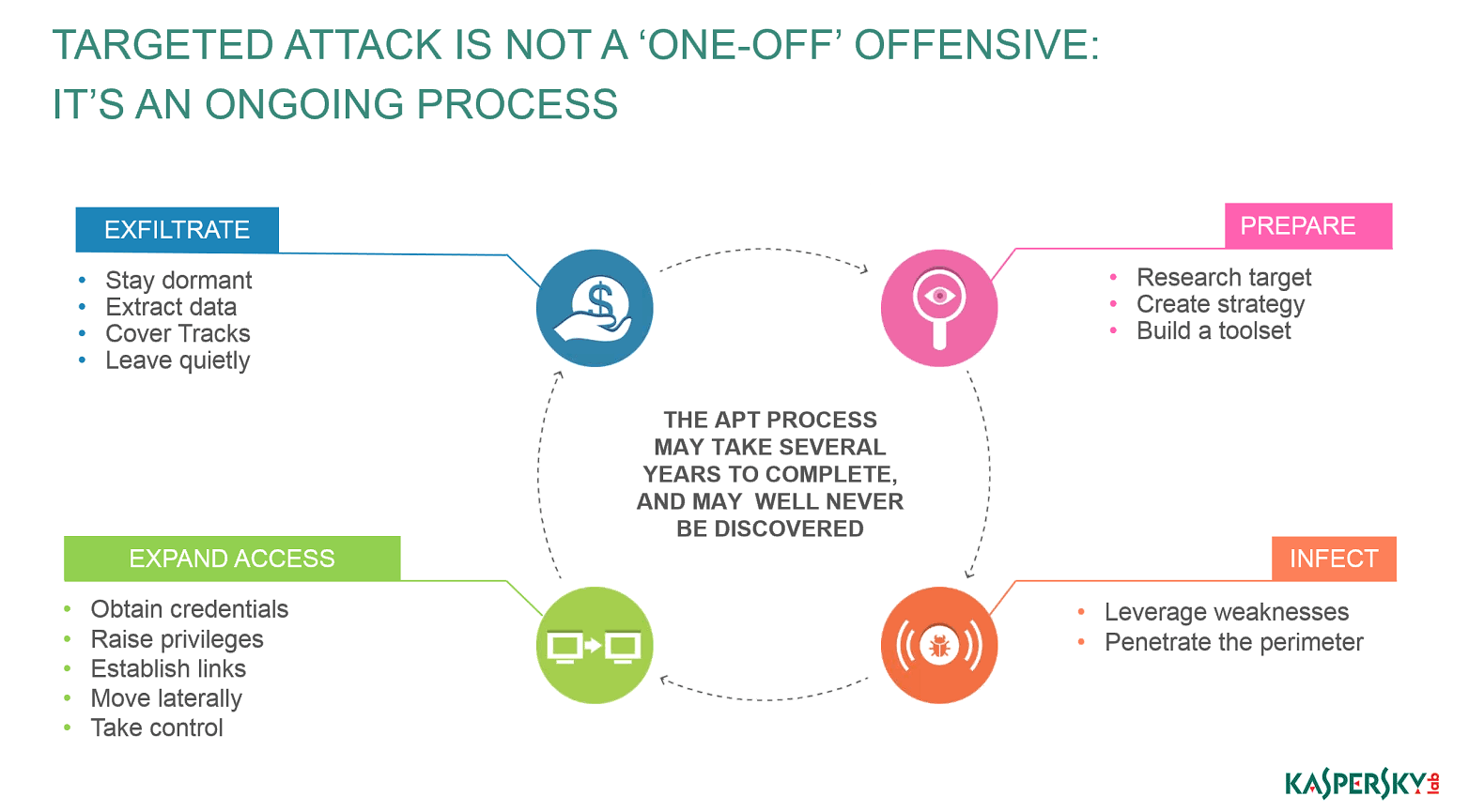
According to statistics gathered by Kaspersky Lab over the last few years, on average a targeted attack may go on for as long as 214 days before it is discovered. Some may stay hidden for up to five years. A large time period may occur between initial penetration and the beginning of immediate malicious activity, such as data exfiltration or money stealing.
Not only do targeted attacks take a long time, they are often extremely sophisticated structurally. Here’s one fictional, but realistic scenario: A bank discovers something is wrong with its ATM. After an examination, the machine turns out to be compromised with a USB sniffer which was used to collect data on the card holders who previously used that ATM. Others besides the clients of this particular bank used the ATM – other banks’ cardholders used it, too. And these other banks systems were later used by the criminals to cash out.
Even deeper research showed that the targeted bank’s ATMs were infected via a previously compromised telecom contractor which partnered with several banks. This telecom company was attacked using plain and simple, but very successful, social engineering. And it took some time for the criminals to find out the appropriate bank to hit.
We can see that the attack chain was long and complex, and that malicious activity could stay uncovered for quite a long time. A usual perimeter defense tool wouldn’t expose it, unless attackers expose themselves somehow.
Most advanced threats are often using basic vulnerabilities, legitimate software, and human factor. The same attack ‘campaign’ may be committed by several actors, and over the last few years more and more often Kaspersky Lab’s experts witness ‘cybercrime-as-a-service’ offers, with some cybercriminals offering their meticulously crafted toolsets to third parties.
The latter then don’t need to be extremely technologically savvy; they just need some money and motivation. Today it’s not a big deal to find an appropriate toolset and infrastructure.
Few attacks, a lot of damage
Countering targeted attacks requires much more than just a strong perimeter: a combination of technology and intelligence is needed, but not every business is willing to invest into such advanced solutions while the perceived probability of the targeted attacks is rather low.
Take a look at the graphic below:
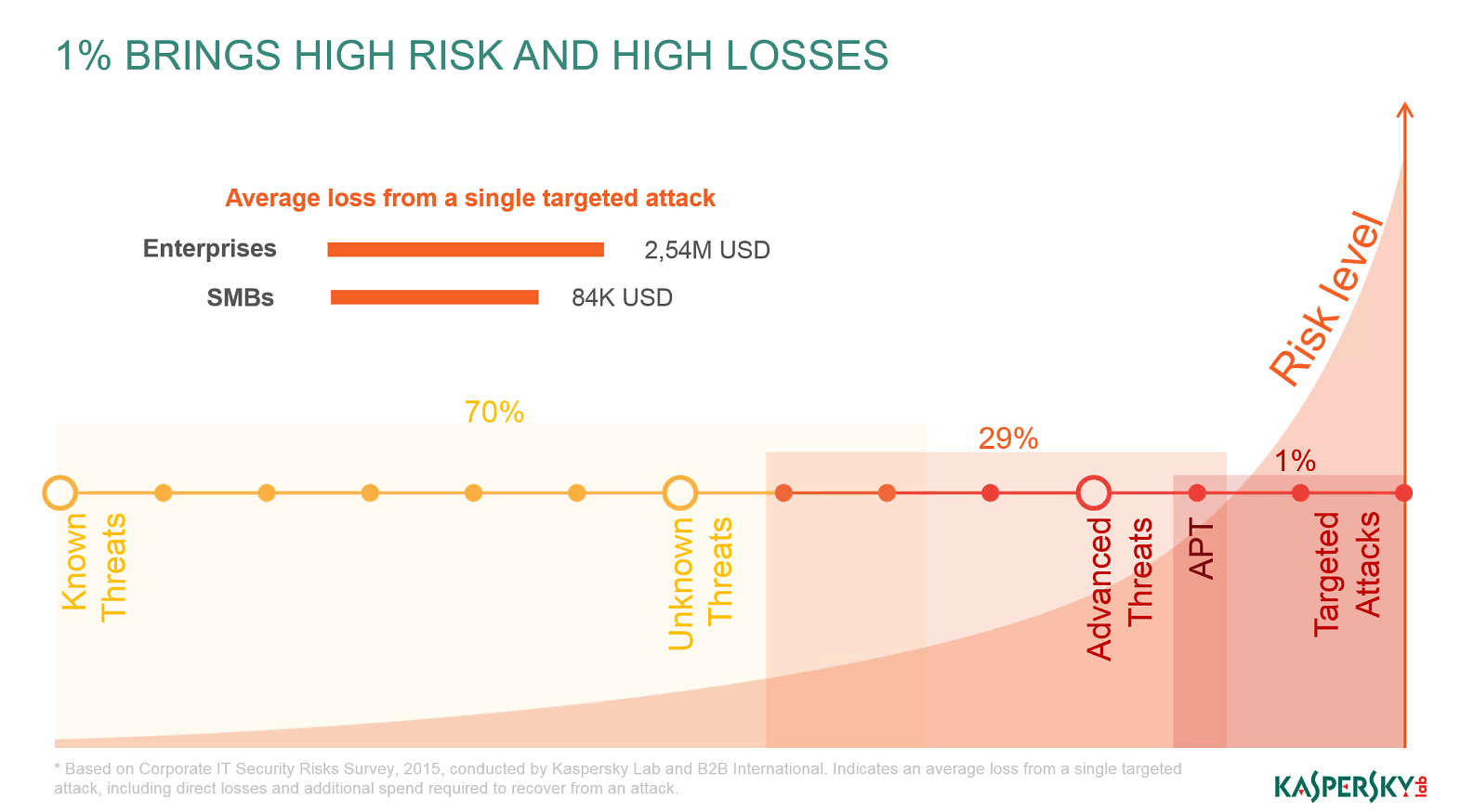
As we see, targeted attacks occupy just 1% of overall threats. But at the same time their risk level is very high, and so is damage.
Enterprises on average lose 2,54M USD per a single attack, SMBs – around 84K USD (data is taken from Corporate IT Security Risks Survey, 2015, conducted by Kaspersky Lab and B2B International). It is also worth mentioning that SMB contractors are often used to leverage attacks against the larger organizations.
Kaspersky Anti Targeted Attack Platform
In order to protect enterprises from these kinds of threats, Kaspersky Lab offers an advanced solution to detect targeted attacks and a range of security services that help businesses respond to current cyber-security challenges and predict future ones.
The main idea behind it is to automate existing technologies and processes, providing a flexible, scalable solution that adapts to the changing threat landscape.
The Kaspersky Anti Targeted Attack Platform is a highly sophisticated solution that enables businesses to detect targeted attacks and other malicious actions through careful monitoring of network activity, web, and e-mail.
This allows for detection of complex attacks at any stage, even when no malicious activity is taking place. Suspicious events are then processed via different engines, including Threat Intelligence, gathering data from Kaspersky Security Network, Targeted Attack Analyzer and Advanced Sandbox, for a final verdict.
The Advanced Sandbox is based on more than 10 years of experience in proactive security technology. It provides a safe, isolated, and virtualized environment for analyzing suspicious objects and detecting their intent. The Targeted Attack Analyzer utilizes data processing and machine learning technologies to assess and combine verdicts from different analysis engines. This is where the final decision to alert the staff is made.
KATA platform also includes Data Acquistion modules, such as Network and Web Sensors, responsible for collecting the data in network and web traffic, E-mail Sensors, those help identifying phishing emails and controlling the transmission of email attachments, and Endpoint Sensors, an optional component, gathering data about events on endpoints, thus increasing the depth of understanding of the overall attack.
These technologies were previously tested and used in-house by Kaspersky Lab. For the first time they are offered to the general market.
The Kaspersky Anti Targeted Attack Platform is available as an independent solution or in combination with expert services aimed at rapid incident detection and response. The availability of these services also enables customers to adapt the solution to specific business needs, thus making it more efficient.
Security Intelligence Services: taking on the attacks before they happen
Kaspersky Lab’s Security Intelligence Services are designed to meet the most frequent demands of large organizations, governmental agencies, ISPs, Telecoms and Managed Security Service Providers. Whereas traditional methods of perimeter defense are no longer sufficient enough, new protection techniques are needed to fill this security gap. A range of services based on Kaspersky Lab’s unique intelligence and expertise had been developed as an answer to this demand.
Security Intelligence Services allow businesses to play ahead of potential attackers. Essentially they cover three main areas. The first of these is Penetration Testing and Application Security Assessment, allowing corporate clients to identify problem areas (i.e. weak spots) and predict the specifics of a cyber-attack before it happens.
Secondly, there is the Cybersecurity Training service, including a workforce awareness program as well as Cybersecurity Fundamentals, Digital Forensics and Malware Analysis/Reverse Engineering training. Given that human factor is one of the most common reasons for the targeted attacks’ success, it is necessary to keep staff aware of what threats it may encounter and how to deal with them.
The third and final type of service is Threat Data Feeds and Botnet Tracking and Intelligence Reporting. The latter offers made-to-order reports on specific aspects of the threat landscape as well as prompt, actionable reports on the latest and most sophisticated threats enterprises may be facing.
For more information on both offerings visit the appropriate web-sites dedicated to these solutions: Kaspersky Anti Targeted Attack Platform and Kaspersky Security Intelligence Services.
 APT
APT

 Tips
Tips