
What it takes to be a CISO: Success and leadership in corporate IT security
Some comments from Kaspersky Lab’s head of information security on the results of the CISO survey.
783 articles

Some comments from Kaspersky Lab’s head of information security on the results of the CISO survey.

How an analyst can build a threat intelligence workflow to run effective and complex investigations.

Our tools to secure, monitor, and manage customer infrastructure can be integrated with Autotask PSA.

Why SMS isn’t the best choice for two-factor authentication, and what alternative types of 2FA you should consider.

Given the great need for it on the part of our corporate customers – true to the market principles of supply and demand – we decided to come up with a new service for the market – Kaspersky Managed Protection.

Android lets you configure app permissions to protect your data and restrict access to dangerous functions. We explain how to do it and why.

Easy protection for complicated threats.

How businesses globally handle personally identifiable information.
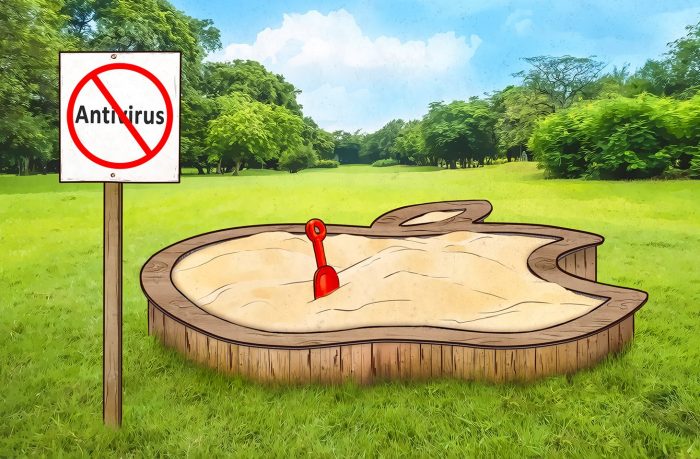
Why doesn’t Kaspersky Lab have an antivirus app for iOS — and what are all those other Internet security suites for Apple mobile devices?

Current status and updates regarding the implementation of our Global Transparency Initiative.

WhatsApp for Android can back up your chats to Google Drive. It’s free, but it may hurt older backups. Here’s how to get it right.
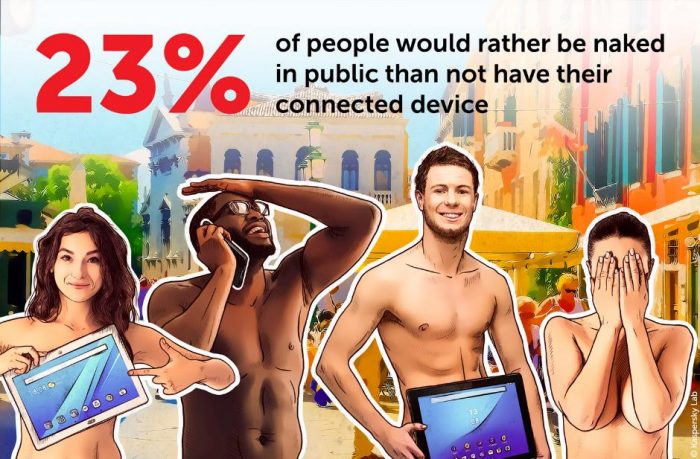
A lack of connectivity can now actually seem worse than many other unpleasant situations.

It makes sense to assess risks and carefully craft a protection strategy before adopting mobile device usage at work.

Any piece of malware can be captured if you know it for what it is — for example, if you use a trainable behavioral model.

Take a stroll through your apps and you’re bound to encounter some unfamiliar names. Where do those unaccounted-for apps on your PC come from, and are they safe?

In this part, we consider mobile malware capable of causing real damage to smartphone and tablet users.

58% of small and medium-size companies use various public-cloud-based business applications to work with customer data.

When I fell victim to sleight of hand and a little bit of fraud, Find My iPhone didn’t save me. Here’s why.

What’s new in the Kaspersky 2019 product lineup? Speed, security, and design improvements.


What is GDPR? What do you need to know about it, and how does GDPR affect you as a Kaspersky Lab customer?