
Busted! Top Prosecutions of May
There was a lot of interesting news about hackers and other cybercriminals, so let’s see who has been busted in May.
1183 articles

There was a lot of interesting news about hackers and other cybercriminals, so let’s see who has been busted in May.

Senior Security Researcher David Emm explains exactly what GameOver Zeus means for you, and how you can keep yourself protected.

Apple has announced new versions of its operating system. OS X and iOS become closer, gradually merging into a single environment. How well is it protected?

May 2014 appears to be very stormy and volatile in regards to information security. Still overshadowed by Heartbleed and Windows XP “official demise” from April, it has brought a lot of troubles on its own.

In recent years, payment and banking services have been drawing closer attention of all sorts of criminals. The number of crimes related to stealing money via electronic communications keeps growing.

A new piece of ransomware is targeting Android users and may be related to the infamous CryptoLocker malware.

The criminals continue their bad business, and law enforcement agencies successfully chase them down. It happens every month, so here are the most interesting cases from April.

Similar to car crash testing, you’re better off avoiding performing PC security tests yourself. Here’s what the pros have to say for a better, more-trustworthy approach.

April 2014 was destined to be the month ‘when Windows XP’ died, but this didn’t happen. The ‘Heartbleed’ bug outshone everything else. Still, there were incidents (unrelated to Heartbleed) worth mentioning.

Banks require new tools to prevent fraudsters from getting to others’ money and Kaspersky Lab’s new Fraud Prevention platform is just the tool to use.

Malware targeting Android devices is increasing, and for the first time, an active Android SMS Trojan targeting users in the United States has emerged.

Last week, we had a look at private messengers; today, we decided to compile a list of good apps to protect you, your iPhone and its content.

The first quarter of 2014 has passed, so Kaspersky Lab’s researchers have released their quarterly report on IT threat evolution for the first three months of 2014. It’s quite an

The concept of mobile malware working in bond with computer Trojans to steal money via online banking is not new, however Kaspersky Lab Q1 report indicates that it quickly gaining “market share”.

There is one somewhat positive outcome from the ongoing #heartbleed scare: the password security issue is back in focus. How big is the ‘adventure’ of changing all passwords going to be?

As reported yesterday, security researchers have found a nasty bug in OpenSSL, which allows reading the memory of systems protected by the vulnerable versions of the OpenSSL software. This effectively

Due to the intensity of recent incidents, we have decided to release our security digests more often. From now on, it will be released every two weeks. Since March 20th

The criminals continue to do their bad business and law enforcement agencies successfully chase them down. That happens every month, so here are the most interesting cases from March. A
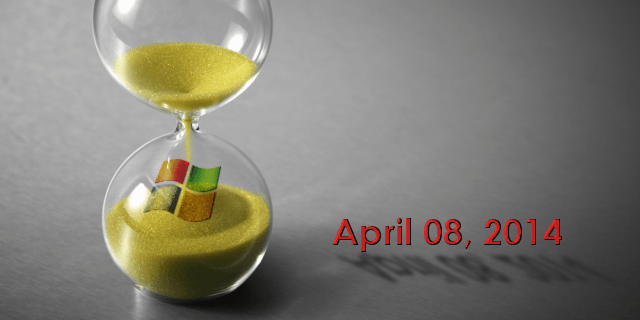
There are just few days left until Microsoft officially stops supporting its operating system Windows XP. This successful and popular operating systems has long become a burden for the company.

March brought with it a host of new security stories, and with those stories came our continued promise to keep you informed while providing protection against cybercriminals. From our interactive