April 2014 was destined to be the month ‘when Windows XP’ died, but this didn’t happen. Instead it’s known as ‘Heartbleed’ month – thanks to the huge bug discovered in OpenSSL software. Everything else that happened in the field of cybersecurity in April was nowhere near the same scale of this particular problem. However, there were a number of events that still deserve attention.
Signed, disguised, malicious
A new variant of the infamous ZeuS Trojan was discovered. It disguises itself as an Internet Explorer document and uses an authentic digital certificate to infect a system with a stealthy rootkit. The infection is done via a relatively simple Man-in-the-Browser type of attack. The presence of a valid certificate is the key difference of the new ZeuS variant, as compared to numerous predecessors, but Kaspersky Lab’s solution blocked this trojan as well as others.
The trial
A few cybercriminals now face trial in the US after using the aformentioned ZeuS malware to steal millions of dollars from people’s bank accounts. A worldwide investigation, initiated by the FBI and conducted in cooperation with authorities from the UK, Ukraine and the Netherlands, preceded the trial.
Read more
A huge e-mail hack in Germany
There was an important announcement made recently by the German authority responsible for information security (BSI). It stated more than 18 million passwords from local and international e-mail services had been compromised. A few months ago a less frightening number of stolen login credentials was released by the same government entity: 16. In the latest batch, 3 million compromised accounts belonged to German citizens.
The officials most likely calculated these concerning figures while they were investigating the underground activity. According to our data, in the first quarter of 2014 more than 20 million online attacks on German users were recorded. These stats are provided by the users of our products who are, obviously, protected. In a case where a PC or Android device is not protected, these attacks often lead to stolen passwords, amongst other things, and as BSI confirms, this number could be in the millions.
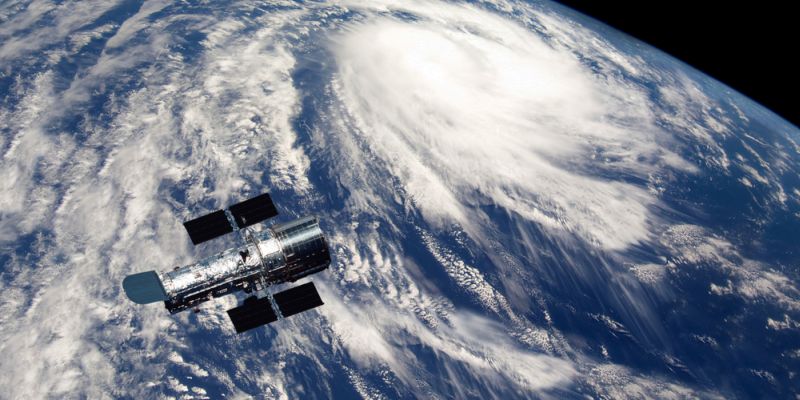
Hacking in space
Experts from IOActive researched the vulnerabilities in the software that controls space satellites. The vulnerabilities, allegedly, allow interrupting data transmissions between a satellite and a client – such as a ship, an airplane, an industrial site or your local ambulance.
Specific types of satellites were not mentioned, but some brands were named, like Harris Corp., Hughes, Thuraya, Cobham, JRC and Iridium. Information regarding the security gaps was sent to the relevant CERTs. Following that, only Iridium responded and took action, making this yet another case of a critical infrastructure that is less protected than some consumer-grade hardware and software.
 cybercriminals
cybercriminals


 Tips
Tips