[Updated on June 28, 2017]
Typically we don’t cheer bugs. However, today we’ll make an exception.
You see a bug or flaw in the code of Petya ransomware has allowed a developer to create a tool to unlock a user’s device without paying the ransom.
Last month, we alerted you about Petya and its pension to destroy devices. So I’d say that a cheer or Internet high-five is well deserved for the user identified as @Leostone on Twitter.
#petya #ransomware #defeated
Get your disks back here: https://t.co/vXH2ny6jdk— leostone (@leo_and_stone) April 9, 2016
With the avatar being an egg, one would have to wonder – does this decryptor actually work? To find out, we reached out to our research team.
The team confirmed that the tool really works. But, there a few issues. First, @Leostone made the decryptor as a webpage that can generate keys for you to decrypt the data. And that page has certain issues with availability at the moment — it seems that it’s hosting provider probably couldn’t handle all the ‘happy Petya customers’ that immediately wanted to get the cure.
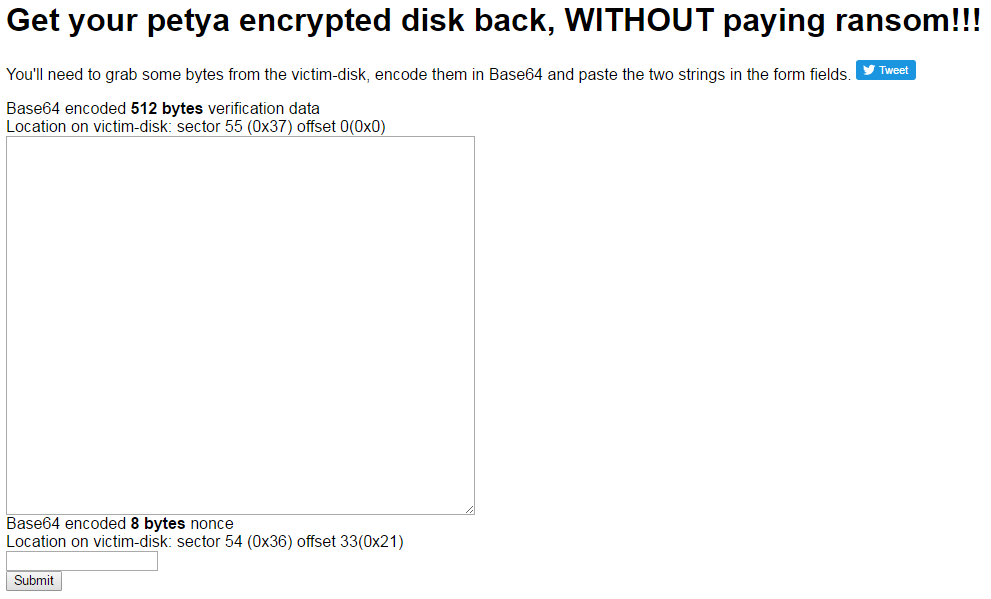
Second, it requires that you remove your hard drive and insert it in into another PC. Than you have to extract some special data from its certain sectors and, using a Base64 decoder, decode. Upload it to the site and — voila — you have the key you can now feed to Petya. And it will decrypt your hard drive back.
As you can see, the procedure is quite complicated and requires certain skills. Another Twitter user, Fabian Wosar, made it easier for you, as he has created a special utility called Petya Sector Extractor that does the dirty part of the job. You still have to remove your hard drive and find another PC to stick it in, but then the utility will extract the required data and process it. The only thing you have to do after that to get the key is input the data that the utility gave to you into the forms on the @Leostone’s webpage.
Our research team also notes that this tool exploits a flaw in the Petya programing. Much like companies with patches, in a week or so we will probably see a newer version of Petya that fixes the flaw that allows the data to be decrypted.
If you’ve fallen victim to Petya and don’t want to pay the ransom of approximately $480, you may want to give the tool a try, you can access the site at: https://petya-pay-no-ransom.herokuapp.com/. The Petya Sector Extractor can be downloaded here. Even with these links, you will need some technical know-how. The team at Bleeping Computer walk you through all of the steps and tech that you will need.
Update from June 28, 2017
If you’re looking for information regarding the new Petya / NotPetya / ExPetr ransomware outbreak, we have a dedicated post with advice on how to protect your files.
 Patya Ransomware
Patya Ransomware

 Tips
Tips