[Updated June 28, 1:30 PM EDT]
Yesterday, a global ransomware outbreak began, and it looks to be as big as the WannaCry story that broke not so long ago.
There are numerous reports that several large companies from different countries have been hit, and the magnitude of the epidemic is likely to grow even more.
Some researchers suggested that the new ransomware might be either WannaCry (it’s not), or some variation of Petya ransomware (be it Petya.A, Petya.D, or PetrWrap). Kaspersky Lab experts concluded that the new malware is significantly different from all earlier known versions of Petya, and that’s why we are addressing it as a separate malware family. We’ve named it ExPetr (or NotPetya – unofficially).
The attack appears to be complex, involving several attack vectors. We can confirm that a modified EternalBlue exploit is used for propagation, at least within corporate networks. More technical info on the attack.
For now, know that Kaspersky Lab’s products detect the new ransomware with the following verdicts:
- Trojan-Ransom.Win32.ExPetr.a
- HEUR:Trojan-Ransom.Win32.ExPetr.gen
- UDS:DangerousObject.Multi.Generic (detected by Kaspersky Security Network)
- PDM:Trojan.Win32.Generic (detected by the System Watcher feature)
- PDM:Exploit.Win32.Generic (detected by the System Watcher feature)
Recommendations for our corporate customers
- Make sure that the Kaspersky Security Network and System Watcher features are turned on.
- Manually update the antivirus databases immediately.
- Install all security updates for Windows. The one that fixes bugs exploited by EternalBlue is especially important.
- As an additional means of protection you can use Application Privilege Control, which is a component of Kaspersky Endpoint Security, to deny any access (and thus the possibility of interaction or execution) for all groups of applications to the file with the name perfc.dat and to prevent the PSExec utility (which is a part of the Sysinternals Suite) from running.
- Alternatively, use the Application Startup Control component of Kaspersky Endpoint Security to block execution of the PSExec utility, but please use Application Privilege Control to block perfc.dat.
- Configure and enable Default Deny mode in the Application Startup Control component of Kaspersky Endpoint Security to ensure and enforce proactive defense against this and other attacks.
- You can also use the AppLocker feature to disable execution of the aforementioned perfc.dat file and the PSExec utility.
Advice for individual customers
Home users seem to be less affected by this threat; the cybercriminals behind it targeted mostly big enterprises. However, effective protection never hurts. Here’s what you can do:
- Back up your data. That’s always a good thing to do in these turbulent times.
- If you are using one of our security solutions, make sure the Kaspersky Security Network and System Watcher components are turned on.
- Manually update the antivirus databases. Seriously, do it right now; it won’t take much time.
- Install all security updates for Windows. The one that fixes bugs exploited by EternalBlue is especially important. Here’s how to do it.
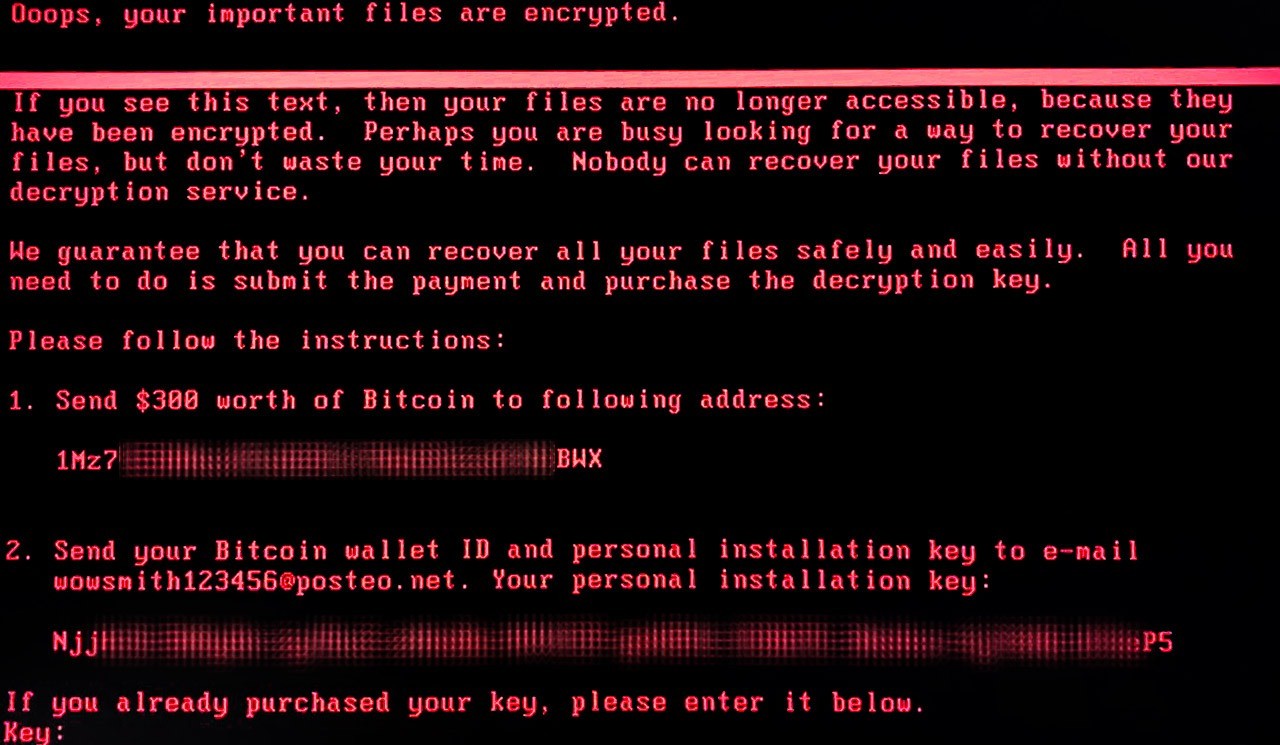
Do not pay the ransom
According to an update seen in Motherboard, German e-mail provider Posteo has shut down the e-mail address that victims were supposed to use to contact blackmailers and send bitcoins, and from which they would receive decryption keys. With the e-mail address blocked, victims won’t be able to pay the criminals or get their files back. At Kaspersky Lab, we do not advocate paying the ransom anyway, but in this case, it’s certainly pointless.
Update: More than that, our experts’ analysis indicates there was never much hope for victims to recover their data.
Kaspersky Lab researchers have analyzed the high-level code of the encryption routine and determined that after disk encryption, the threat actor could not decrypt victims’ disks. To decrypt, the threat actors need the installation ID. In previous versions of seemingly similar ransomware such as Petya/Mischa/GoldenEye, this installation ID contained the information necessary for key recovery.
ExPetr (aka NotPetya) does not have that installation ID (the ‘installation key’ shown in the ExPetr ransom note is just a random gibberish), which means that the threat actor could not extract the necessary information needed for decryption. In short, victims could not recover their data.
Don’t pay the ransom. It won’t help.
 threats
threats

 Tips
Tips