Password leaks are one of the most annoying problems of the digital age. At first glance, it might seem like no big deal: who cares if someone finds out the password to some old e-mail account that is rarely used and contains nothing of value?
But then you remember that this same e-mail is linked to your social network accounts, not to mention banking and other apps, and it’s now in cybercriminal hands. Besides the anguish of losing money and data, such a leak can cause major headaches for your friends, family and colleagues — after all, a hijacked account can be used to send phishing or scam e-mails in your name to all your contacts.
In this post, we explain how your credentials can be stolen and how to reduce the risk of them leaking. Sure, caution and vigilance play a massive role in it, but there are hi-tech solutions specifically designed to prevent leaks, which often handle threats much better than the naked eye.
Trojan stealers
These stealthy spies, once on your device, usually display no visible signs of activity. After all, the longer they remain under the radar, the more of your data they can steal and pass to their handlers, such as passwords for banking apps or gaming services.
A Trojan can get on your computer or smartphone if you open a malicious file sent by another user, downloaded from a website or copied from external media. Remember that any executable file from the internet is a potential trap.
But even those files that look like non-executables need to be treated with caution. Cybercriminals do their best to fool victims by disguising malicious files as images, videos, archives, documents, etc., and often they succeed. For example, they might change the icon or use a fiendishly cunning filename that mimics a safe format. What’s more, even an ordinary Office document can turn into a trap under certain conditions: a malicious script in the document can exploit a vulnerability in the program you use to open it.
Therefore, to combat such leaks, we recommend installing a security solution that can detect and block spyware Trojans. If you use Kaspersky, you’re already armed with:
- File Anti-Virus that scans the contents of your device and any connected media, and detects malicious files;
- Mail Anti-Virus that blocks dangerous links and attachments in e-mails.
Phishing
Phishing e-mails come in a variety of forms, but the goal is always to lure you to a fake website and get you to enter your credentials. It might be a message saying your bank account has been blocked, or an early-bird offer to subscribe to an online movie theater. Or it might be a phishing link from an attractive stranger on Tinder, a potential buyer of your product on Amazon, or even a close friend (if their e-mail was hacked by scammers).
The standard tip in this situation is to look carefully at the URL: some fake sites have an extra letter in the address, a double domain name, etc. However, that does not always help since modern cybercriminals have learned how to disguise their fakes. For example, in case of a browser-in-the-browser attack, you might see a phishing site with a genuine address.
So it’s better to play it safe and use a security solution that spots phishing attacks and warns you about them. In your Kaspersky application, this is handled by:
- URL Advisor that checks the URL against a cloud database of dangerous sites;
- Safe Browsing that checks the site content for malicious elements.
Browser attacks
Often, passwords get stolen through browser vulnerabilities or extensions. In the first case, specially crafted code on a web page plants spyware on your device. In the second, you yourself install a malicious script under the guise of a handy browser plug-in. After that, when you go to, say, a bank website, this script redirects all traffic through a hacker proxy server, spilling your credentials in the process.
- The Safe Money feature in Kaspersky provides protection against such attacks. It automatically enables Protected Browser mode when you visit online stores or banks, or use online payment systems.
Public Wi-Fi
Attackers can also intercept data (including passwords) sent over the network if you’re using unencrypted or old WEP-protected Wi-Fi. Another variant is when a hacker sets up a public Wi-Fi hotspot with a name similar to an existing network (usually belonging to a nearby cafe, hotel or business center). The inattentive user connects to the fake hotspot and all their internet traffic flows straight to the cybercriminals.
You can avoid such leaks by carefully checking network names, avoiding suspicious access points, and disabling automatic connection to Wi-Fi. Better still, ensure that all your traffic is encrypted, then, even if you do connect to the wrong hotspot, eavesdroppers won’t know what you’re sending or where.
- You can enable VPN Secure Connection in your Kaspersky application in the settings under Privacy. Note that with the Plus and Premium versions, you get unlimited VPN traffic.
Passwords all around
Then of course there are people who write down passwords on sticky notes and bits of paper, then leave them in full view of any passerby. Don’t be like them. It is also dangerous to write passwords in insecure text files on your computer or smartphone, or store passwords in the browser for autofilling.
So what to do instead? After all, infosec experts bleat on about the need for strong passwords that can’t be brute forced. They also don’t stop ranting about never using the same password more than once, because if it gets stolen, attackers will have more to steal from you. Is the solution, then, to create a memory palace full of long, complex passwords? But hardly anybody has such a gifted mind.
An easier option is to use a password manager protected by strong encryption. Simply enter all your usernames and passwords and memorize just one master password for the vault itself.
- In your Kaspersky application, this secure vault is provided by Password Manager. Whatever you do, don’t write your master password on a sticky note attached to the monitor!
External leaks
All of the above is about keeping passwords safe at your end, but leaks often occur in remote internet services: online stores, social networks, crypto exchanges, or any other resource with login authentication. By hacking such a site, cybercriminals can get ahold of a huge user database, plus passwords and other personal data.
What’s more, the owners of such sites are not always keen to report such hacks. Meanwhile, your data gets passed around or put up for sale on the dark web. Infosec experts monitor the publication of such databases and warn users.
As always, however, be careful: here, too, such “experts” might appear to be scammers in disguise. This is a common phishing method: the user receives a message about an alleged leak and is invited to follow a link to a site asking for their credentials supposedly for verification, whereupon the password is stolen for real.
- Your Kaspersky application has a service for checking whether a leak really happened or not. Called Data Leak Checker, it is found on the Privacy tab. It lets you check whether your e-mail is spotted in a stolen database somewhere. If so, you will receive a list of leaky sites, the type of data made public (personal, banking, online activity history and so on), as well as recommendations on what to do about it.
Protection for all seasons
Of course, password theft is not the only misfortune that can befall your digital self. Attackers have all kinds of tricks up their sleeve for stealing valuable data, emptying online bank accounts and causing other harm: spyware, ransomware, fake websites, malicious miners, the list goes on.
But never fear: we keep a close eye on cybercriminal creativity and continuously improve our products to deliver the best protection in the world against all digital threats. So, you can always rely on Kaspersky to warn of danger in good time, block malicious objects and generally keep you out of trouble.
 passwords
passwords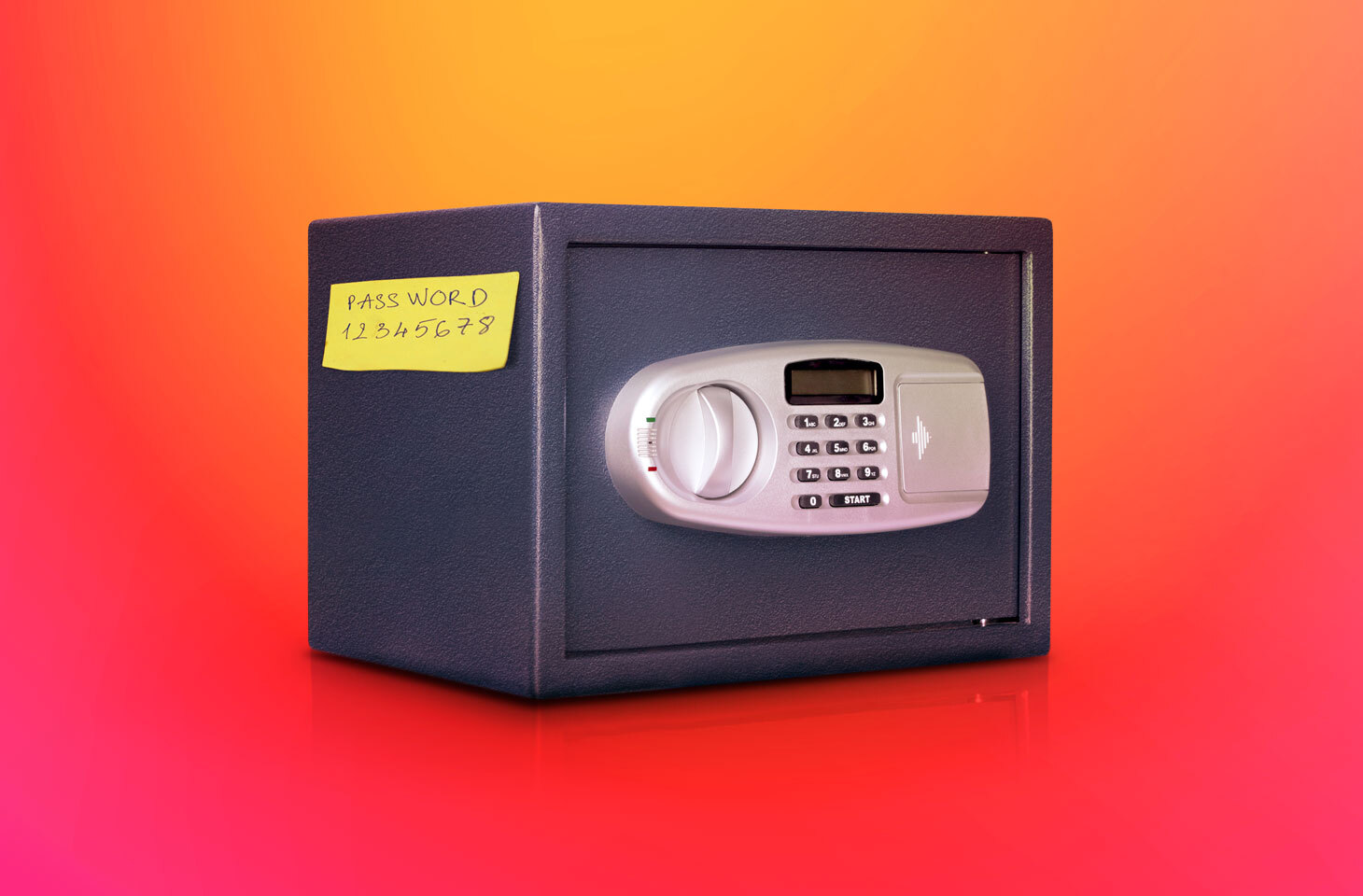

 Tips
Tips