
Fake ticket websites exploiting BTS world tour
Kaspersky experts have detected fake websites that steal money from BTS fans during ticket pre sales. We explain how to stay vigilant and not fall victim to the scammers.
4252 articles

Kaspersky experts have detected fake websites that steal money from BTS fans during ticket pre sales. We explain how to stay vigilant and not fall victim to the scammers.

Protecting a security console is more critical than one might think. Here’s the lowdown on control-layer compromise, and how to keep it from happening.
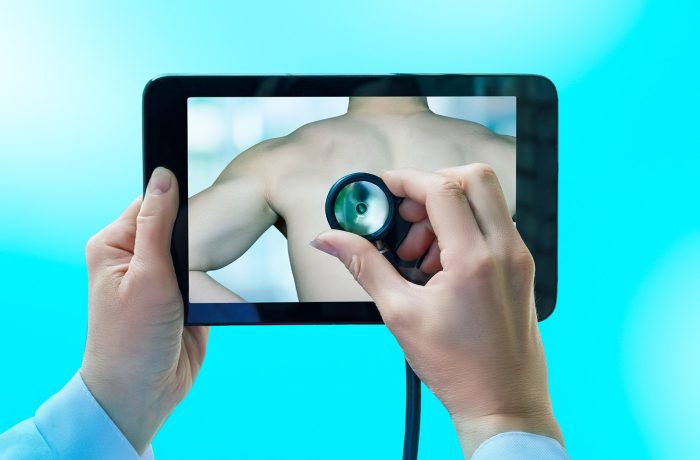
Telehealth services and apps are blowing up in popularity right now, making the availability of medical services better than ever. But just how safe is telemedicine, and what kind of risks does it carry?

How to manage vulnerabilities when developing or using open-source software.

How the AI boom and increasing reliance on open-source components are piling up corporate security debt — and what you can actually do about it.

The new CrystalX remote access Trojan looks like the prank viruses of the 90s on the surface, but it causes a lot more damage. It spies on all that’s happening on your computer, steals cryptocurrency and accounts, and gives the attacker full control over your device. We break down how it works, and how to avoid becoming a victim.

Personal backups and home NAS are now in cybercriminals’ crosshairs. We break down exactly how hackers encrypt your data — and how you can stop them.

Researcher Niels Provos’ prototype IronCurtain architecture: a system designed to restrict the actions of AI agents through isolation and security policies.

In 2025, just as in the year prior, supply-chain attacks remained one of the most severe threats facing organizations. We’re breaking down last year’s most noteworthy incidents.

Spammers have figured out how to hide links to fraudulent sites within surveys created on legitimate platforms. We’re breaking down the ruse and sharing tips on how to avoid falling for it.

How open-source security solutions became the starting point for a massive attack on other popular applications, and what organizations that use them should do.
Cybercriminals are now deploying web applications generated by Bubble, an AI-powered app builder, to hunt for corporate credentials.

Intellexa’s Predator spyware can hide camera and microphone usage indicators on iOS devices. Here’s a look at how it pulls it off.

In November 2025, the npm ecosystem was hit by a flood of junk packages that were part of the IndonesianFoods malicious campaign. We’re breaking down the lessons learned from this incident.

We break down how AI assistant hallucinations can turn lethal, and explain the fundamental principles you need to follow to avoid becoming an accidental casualty of progress.

Threat actors are promoting pages containing malicious instructions for installing AI agents intended for workflow automation.

We break down the BeatBanker trojan attack, which combines espionage, crypto theft, and mining with inventive ways to dig its heels into a smartphone.

We’re diving into why mental health apps have become a headache for their users, and how to minimize the risks of medical data leaks.

Educational institutions are increasingly falling victim to ransomware attacks. We look at some real-world incidents, explain their causes, and discuss how to mitigate risks to academic infrastructure.

Tired of hallucinations in AI overviews, and have no clue as to why or how Copilot suddenly appeared on your PC? Here’s a guide to switching off those intrusive AI features in popular services.
A browser-in-the-browser attack, theoretically described in 2022, has been adopted in real-world phishing. We break down how it works, and how to spot a fake authentication window.