We are now halfway through the first day of Kaspersky Lab’s Security Analyst Summit, a security conference taking place in Cancun, Mexico. So far six presentations have been held, including our own research on the large-scale attack on the banks known as Carbanak. We’ve got much more news to come, so we advise you to follow our special live blog today and tomorrow. But now I would like to focus on the particular quotes from our speakers that are particularly important for businesses.
SAS is the conference of experts, so we have a lot of technical stuff here, even the assembly code popping up in PPTs here and there:
But tech is just the part of the story. At some point every speaker talks about how technology applies to the real world. Here are the most notable examples.
Wise words from @dakami – insecurity isn't coincidence, it's consequence. #TheSAS2015
— Costin Raiu (@craiu) February 16, 2015
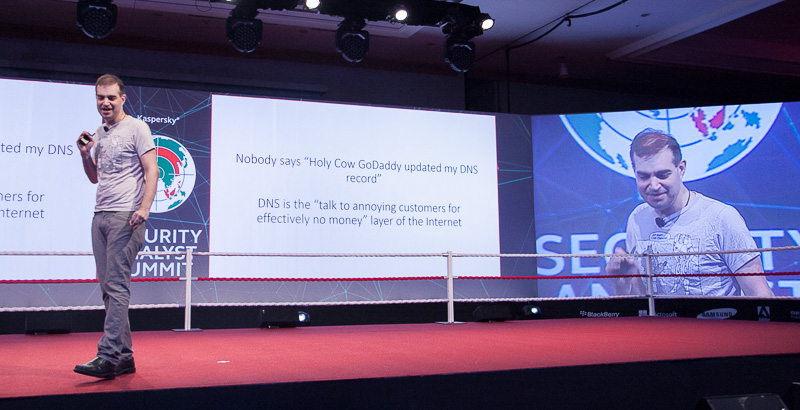
The presentation by Dan Kaminsky of Doxpara Research was very technical and focused on the inherent insecurity of modern internet communications. Internet is indeed broken, but what is the real reason for it? Infortunately, insecure software, network protocols and infrastructure design are cheaper to build. They are faster and easier. That is why broken internet is not a coincidence, but a consequence of an approach when security is not a top priority. More info here.
Broken internet is not a coincidence #TheSAS2015
Tweet
What is the result of loose security? Kris McConkey from PriceWaterhouseCoopers offered a few examples today. The most notable is how much money businesses lose thanks to cyberattacks. Describing the activity of a certain threat actor, he noted how the amount of damage inflicted went up from $10 to $40 million in just a couple of years. Cybercrime gets more and more sophisticated tools at their posession, so the price of a breach for companies increases.
One particular threat actor’s income increased 4 times in a couple of years
Tweet
The best example of a really devastating advanced persistent threat was shown by Kaspersky Lab’s experts Sergey Golovanov and Sergey Lozhkin during there keynote on Carbanak APT.
You can read all details here or here. The most important business aspect of this story is how cybercriminals managed to fully control operations of a victim bank. They could tell ATMs to dispense money at any given time with no card provided. They altered figures in bank’s internal system, inflating their own bank accounts and stealing money. They managed to hide their operations for quite a long time. This is the true example of an advanced threat, that is, first of all, very hard to detect.
What should businesses do? The advice comes from another speaker, Steve Adegbite from Wells Fargo.
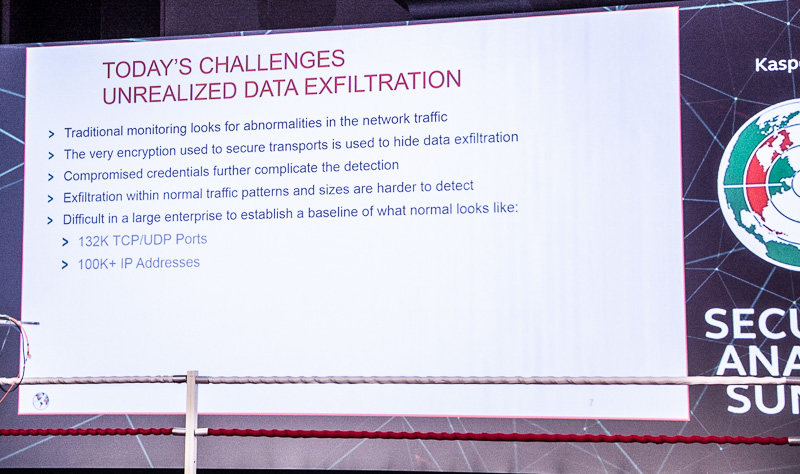
He talked about enourmous challenges that businesses face when trying to protect their sensitive data. Advice? Act like the data exfiltration is already happening or about to take place. Plan you defence strategy accordingly.
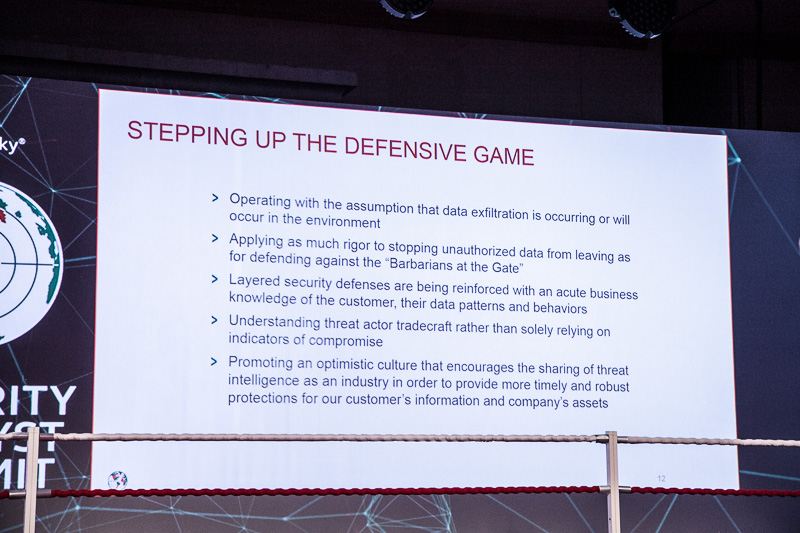
Another key advice is maintaining multiple layers of protection. Understand threat landscape and particular threats that your company is facing. Share information.
Stay tuned for more updates from #TheSAS2015 here at our business blog and Twitter.
 business security
business security


 Tips
Tips