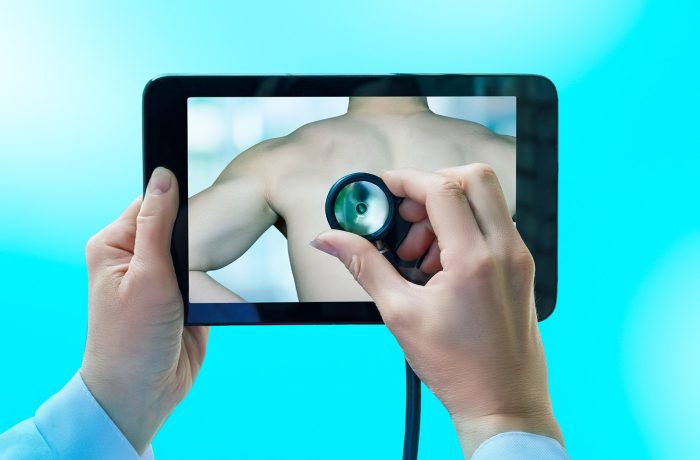
Is telehealth actually safe?
Telehealth services and apps are blowing up in popularity right now, making the availability of medical services better than ever. But just how safe is telemedicine, and what kind of risks does it carry?
1402 articles
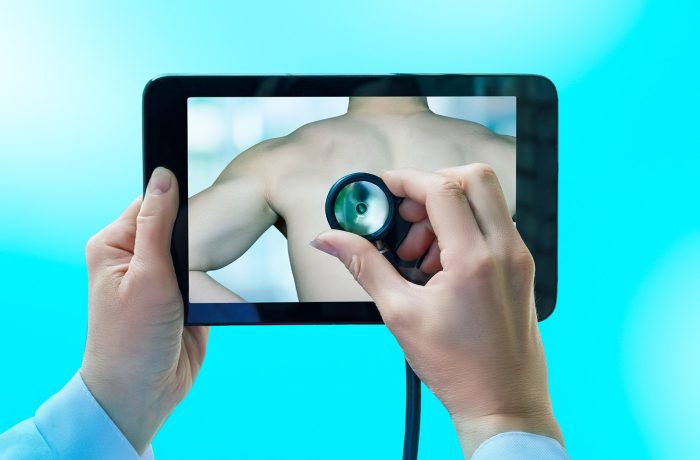
Telehealth services and apps are blowing up in popularity right now, making the availability of medical services better than ever. But just how safe is telemedicine, and what kind of risks does it carry?

The new CrystalX remote access Trojan looks like the prank viruses of the 90s on the surface, but it causes a lot more damage. It spies on all that’s happening on your computer, steals cryptocurrency and accounts, and gives the attacker full control over your device. We break down how it works, and how to avoid becoming a victim.

Personal backups and home NAS are now in cybercriminals’ crosshairs. We break down exactly how hackers encrypt your data — and how you can stop them.

Researcher Niels Provos’ prototype IronCurtain architecture: a system designed to restrict the actions of AI agents through isolation and security policies.

How open-source security solutions became the starting point for a massive attack on other popular applications, and what organizations that use them should do.

We break down the BeatBanker trojan attack, which combines espionage, crypto theft, and mining with inventive ways to dig its heels into a smartphone.

We’re diving into why mental health apps have become a headache for their users, and how to minimize the risks of medical data leaks.
A browser-in-the-browser attack, theoretically described in 2022, has been adopted in real-world phishing. We break down how it works, and how to spot a fake authentication window.

What corporate security teams should do about the “viral” AI agent.

Today we’re diving into the OpenClaw AI agent — formerly known as “Clawdbot” and then “Moltbot” — to prove once again that secure AI is still a long way off.
Breaking down core cybersecurity terms that colleagues often interpret differently or incorrectly.

Learn how to spot deepfakes in photos, videos, voice messages, and video calls in real time.

Detecting attacks related to compromised accounts with AI and other updates in Kaspersky SIEM.

NFC relay attacks, pre-installed Trojans, and other nasties ruining the Android experience in 2026.

Our Android apps are no longer available on Google Play. We explain how to download, install, and update them by alternative means.
Generative AI has taken sextortion techniques to a whole new level — now, any social media user can become a victim. How can you protect yourself and your loved ones?

Eight digital New Year’s resolutions you absolutely need to keep.

We’ve identified a new infostealer named Stealka, which masquerades as pirated software and game mods. It targets data stored inside browsers, locally installed applications, and crypto wallets.

We break down a new scam that leverages Telegram Mini Apps, and explain how to avoid taking the bait.

How to eliminate the threat posed to organizations by ownerless servers and services, outdated libraries, and insecure APIs.

We follow the trail of a phishing attack to break down, step-by-step, what happens to the data stolen from users.