Fortnite? Overwatch? League of Legends? If you’ve heard of these games but don’t know an aim-bot from a wall-hack (let alone ESP), read on to understand why some ordinary folks feel like a fish out of water in competitive matches — and why that matters.
As of 2018, video games represent one of the most lucrative businesses in the world, generating more than $43 billion in revenue in the United States alone. An entire media ecosystem has sprung up around the gaming industry, with e-sports or electronic sports tournaments broadcast on cable television attracting nearly 400 million viewers each year. Streaming platforms such as Twitch and Mixer add even more viewers to the mix.
Contrary to stereotypes involving teenage boys and young men, ESA (Entertainment Software Association) research indicates that in the US the average gamer is 34 years old, and women represent 45% of the demographic. A leading factor when deciding which video game to purchase these days is online game-play capability, which enables developers and publishers to charge a subscription fee and provides players with a competitive arena to test their abilities against ranked opponents.
Video game cheats are nothing new, but now, among the great variety of performance enhancing cheats we are seeing cheats that demonstrate malwarelike behavior, using evasion features and techniques that rival those of advanced persistent threats.
What is video game cheating, and how does it affect the industry and other players?
In the context of today’s massive multiplayer and online games, cheating can give a player unfair advantage over actual opponents. It spoils the fun for everyone and causes direct (by cheating) and indirect (through attrition) financial losses for game companies that can’t seem to stop them.
No one taxonomy exists for the classification of cheats, but very broadly, two categories of cheat exist for online video games: exploitation of technical vulnerabilities in the client, the server, the environment, or the game; and fraud through compromise of the privacy or security of other players, or by insider manipulation. Unsurprisingly, these two kinds often go hand in hand.
A gray market emerges
For years, stolen game items or credentials were available even at well-known auction sites such as eBay. Nowadays, specialized virtual item websites have emerged to serve players seeking shortcuts to level up or obtain game items. The economy includes virtual sweatshops in which someone else takes over the player’s account to perform dull or repetitive tasks — and that’s only the tip of the iceberg. In addition to selling cheats, some online communities trade and resell hacked accounts for games, VPN providers, and pornography websites.
In addition to selling cheats, some online communities trade and resell hacked accounts for games, VPN providers, and pornography websites
One of the most infamous cheats serves to show the magnitude of the cheat market: WoWGlider, a bot developed by MDY Industries for the game World of Warcraft, which at its peak gathered 12 million players in a virtual world. WoWGlider sold more than 100,000 copies for $25 each, making this single cheat a multimillion dollar enterprise.
As with ransomware, sometimes fighting cheat developers using legal resources means a long and tedious process under the laws of more than one country — and even if the immediate result is positive for the game publisher, nothing stops other individuals from taking up the torch, promptly replacing one cheat with another.
Surfing the ban wave
During January 2019, Valve Corporation, creator of the digital distributor platform Steam and popular games such as Counter Strike, Dota 2, and others, banned more than 1 million accounts in what is known as the biggest ban wave ever to hit Steam (so far).
Still, communities are riddled with messages complaining about the number of cheaters increasing and ruining the game.
Valve’s digital download market and community registered 125 million users as of 2018, remaining the dominant PC games distribution platform. Steam offers publishers and developers a straightforward and familiar environment for monetizing their creations.
One of the features that helps Steam maintain its lead as an online gaming platform is the VAC (Valve Anti-Cheat) system, which seeks out cheats installed on users’ computers and bans those users. Even if new accounts are easy to obtain, unless the user provides some form of verifiable information such as a credit card or a phone number, the platform’s functionality will be greatly reduced.
The way anticheating engines work remains unclear; security through obscurity appears to be an essential component to keep cheaters in the dark about how detection is being made. However, even doing a simple Web search has caused some anticheating solutions to prohibit players from joining a game after memory scans detected words such as “cheat” and flagged the suspicious activity. Valve’s VAC was accused of inspecting DNS queries made by the user, even prior to launching any game from the platform.

VAC will monitor running software, and if it detects Powershell, Sandboxie, Cheat Engine, or other denied utilities, it will prohibit the player from joining an online match
Anticheating tactics include full memory scanning, process analysis, code inspection, and more. Naturally, users have raised concerns over privacy issues when they learn about how the components work or how much of their information is being sent to third parties.
Dissecting malwarelike cheats
When considering the network architecture of online games, some elements have to be handled by the client to speed up processing and reduce the lag between when an action is sent to the server and when a response is received and rendered on the display.

A wall-hack and aimbot from a cheat provider that sells time-based subscriptions for different games. A monthly subscription can start at about $20, going up to $100 for a lifetime membership
This leaves the door open to client-side cheating, where the player can modify game files, memory variables, or even use different graphic card drivers to reveal information that was previously hidden by the game client. Such is the case with wall-hack or ESP (extrasensory perception) cheats, in which the player is able to see opponents through walls and can exhibit godlike abilities simply by having more information at hand than other players.
Fortnite, a battle-royale-style game with more than 250 million players, detects the presence of a running debugger when the game is launched and attempts to thwart reverse-engineering activities, warning the user about it. More advanced cheaters now use rootkits that can hide game modifications from anticheating utilities. This creates a dynamic threat landscape in which game developers need anticheating solutions to protect their games, and these solutions could also exhibit rootkit behavior. It’s an arms race between two opposing forces — ironically, not unlike many current video games.
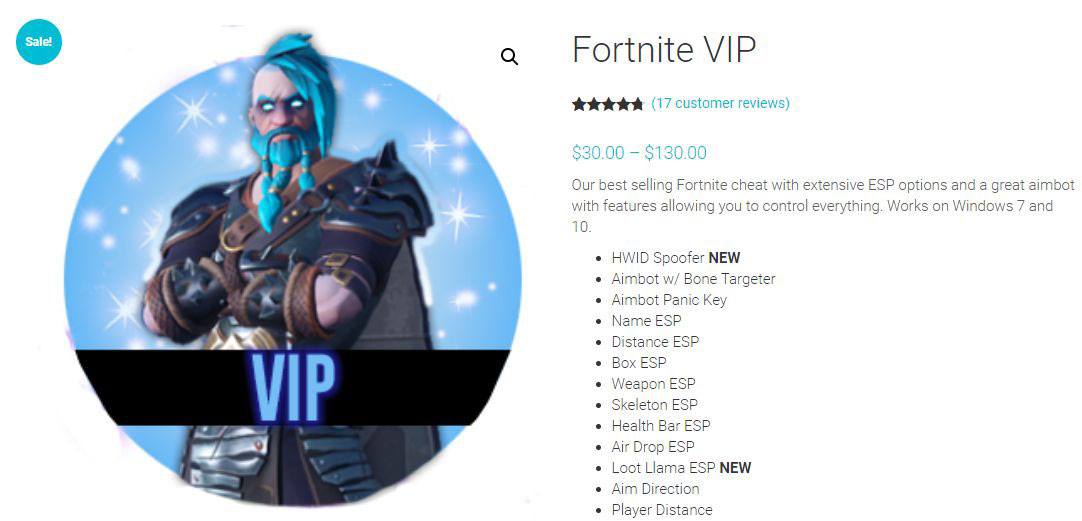
Depending on the game and how customized the cheat is, the price could easily exceed the original cost of the game
Cheats ruin other player’s fun — for starters
The activity of cheating in video games covers a wide spectrum of activities and motivations.
A growing economy is thriving in a niche market, targeting those individuals looking to pay for utilities, hacks, trainers, and modifications that can alter the game’s difficulty at will. Their behavior is sometimes internally justified when the cheating is done to beat the system, not other human players. The social and behavioral ramifications of doing wrong to other players would require a different type of study; its consequences are evident and have a direct impact on the revenue of legitimate companies and honest players.
Monetary estimates of the size of this virtual economy are problematic; legally prosecuting relevant cases reveals only a modest glimpse of this landscape. The problem is likely much bigger than what is currently represented by a handful of examples. The information security community is beginning to take a more proactive approach when it comes to educating and protecting gamers.

Communities are riddled with messages complaining about the increasing number of cheaters ruining the game for players and the reputation of the developers
Providing companies and users the fair play environment they expect requires a multidisciplinary approach, and just as game developers may not possess high-level security skills, security professionals may not be more than passingly familiar with the gaming universe.
Video game developers rely on a variety of common principles to creating compelling and addictive environments that players can’t resist. Considerable effort goes into designing levels, characters, and a reward system that will keep players coming back for more. Cheaters unbalance this delicate equation.
And when players stop playing, and online communities become toxic, a whole industry, and the jobs that depend on it, suffer.
Not all is what it seems
“The cake is a lie.” In the game Portal 2, an Easter egg shows that the motivating reward is not always real. The essence of behavioral game design distilled in a simple phrase.
Cheating is as old as mankind, although adding the technology component produces an attractive scheme in which to study and understand the consequences of this behavior on a massive scale. A wide range of utilities for game modification, some with malware-like abilities, are distributed every day.
The antivirus industry already has experience in dealing with obfuscated code, packed executables, and other common techniques found in malicious samples that can easily be transferred to the gaming ecosystem. Even if not all cheats are created equal or are malicious in their nature, the illegality of these creations is clear even before taking into consideration the security and privacy implications for users.
 gamers
gamers


 Tips
Tips