Loyal Kaspersky Daily readers are already aware of the recent mobile security trends: the hottest topic among cybercriminals are mobile banking Trojans. When you do your banking on a smartphone, thieves can intercept everything they need to steal from you – usernames, passwords, even one-time passwords being sent via text messages. However, until recently, these threats seemed to be relevant only to Androids– due to strict application restrictions in iOS and its curated app store, iPhone users rarely met mobile threats other than phishing. Now it turns out that iOS is not that safe after all. The SSL bug dubbed “goto fail”, which is fixed in iOS 7.0.6, enabled hackers to intercept or modify the content of seemingly secure encrypted communications. But it’s definitely not the end. A security company FireEye published the research, which describes the method of intercepting all keyboard- and touchscreen-related events in iOS, effectively making it possible to create a keylogger on an iOS device without a jailbreak.
The principle is simple – a rogue application (it can disguise itself as something innocent, e.g. a music player) can enable background monitoring on the iOS 7 device and record all touchscreen events on the smartphone. Each event is a simple message like “User touched the screen at X, Y coordinates”. As the iOS keyboard is 100% standard, it’s easy to figure out which letter corresponds to these coordinates. The demo application, created by FireEye, sends the data to the remote server, where it is translated to actual keypresses, making hackers able to log all keystrokes on the iPhone. If you type your password, it will be immediately uploaded to the hackers’ database, possibly leading to every negative consequence you can imagine. The app keeps monitoring users’ keypresses even when the “background app refresh” is disabled in the iOS settings. To get rid of this spy, the user has to disable background monitoring and manually terminate all suspicious or unneeded apps via the task manager.
Luckily, this flaw was discovered by responsible researchers, who immediately reported it to Apple and are now helping Cupertino fix the issue. However, the update is not yet available to end users as we write.
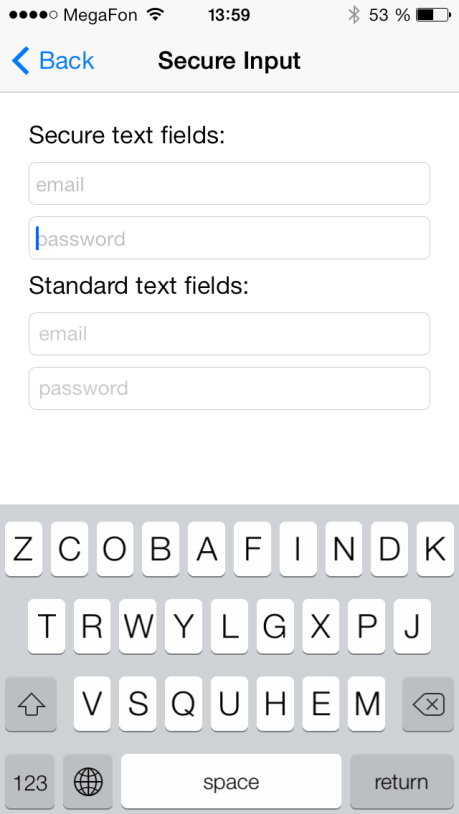
Due to the restricted nature of the iOS platform, there is not much you can do about the vulnerability. The aforementioned technique is very inconvenient as it makes multitasking useless. There are some third-party keyboards with alternative keymaps in the App Store, so you can type sensitive data into these apps and copy-paste it to banking apps or sites. However, this won’t guarantee the data’s safety. To achieve much better protection, security measures should be implemented by the banks themselves. This is where Kaspersky Lab comes into play. A recently announced Kaspersky Fraud Prevention platform can be used to strengthen the defenses of mobile banking apps by adding several security layers on top of existing banking app functionality. One of the layers is called Secure Keyboard and addresses the keylogger issue. If your banking app uses Secure Keyboard for sensitive data, letters on the screen are placed in a random order, making it impossible to translate keypress coordinates to a specific letter. This effectively renders the described technique useless, protecting your data from criminals.
There are other technologies available that protect both desktop and mobile devices from financial threats; you can explore some of them on the Kaspersky Fraud Prevention page.
 cybercriminals
cybercriminals

 Tips
Tips