How IT security leaders can unlock the potential of their teams
Introduction
We’re all aware of the analogy of a domino effect. One factor can have an impact on another, and another, and another. And, of course, this can work in both directions. But the starting point is always critical to deciding the eventual outcome. In cybersecurity this theory is being played out among organizations that are yet to fully achieve the digital protection that is required. Traditionally, decision-makers have been hindered by financial restraints, which may have contributed to IT security teams that were either overworked or underwhelmed in their roles. This then leads to the potential of more errors, less conducive threat intelligence processes, and higher rates of employee turnover. The negative domino effect in full display.
In this fourth report in our IT Security Economics series, we explore each stage of this effect: the contributory reasons on both sides of the worker dynamic; the ramifications for businesses and their cybersecurity status; and, most importantly, how to point those dominoes in the other direction.
We study how cybersecurity is managed across enterprises and smaller businesses. Do they have dedicated IT security departments? Are tasks and remits siloed and specialized, or overlapping and merged? Is the overworking issue built out of mismanagement or financial restraint? Would outsourcing help to relieve some of these pain points? We even ask what employees are doing when fulfilment levels plummet.
This final report urges technology teams to improve their human touch, to get those dominoes tumbling in a more favorable direction.
Methodology
The Kaspersky Global Corporate IT Security Risks Survey (ITSRS) interviewed a total of 5,266 IT business decision-makers across 31 countries in June 2020. Respondents were asked about the state of IT security within their organizations, the types of threats they face and the costs they have to deal with when recovering from attacks.
Throughout the report, businesses are referred to as either SMBs (small and medium sized businesses with 50 to 999 employees), or enterprises (businesses with over 1,000 employees). Not all survey results are included in this report.
Key findings
- Half (52%) of enterprises have a dedicated IT Security department while some further diversified the workforce – 20% have an internal security operations center and 14% employ a special malware analysis team
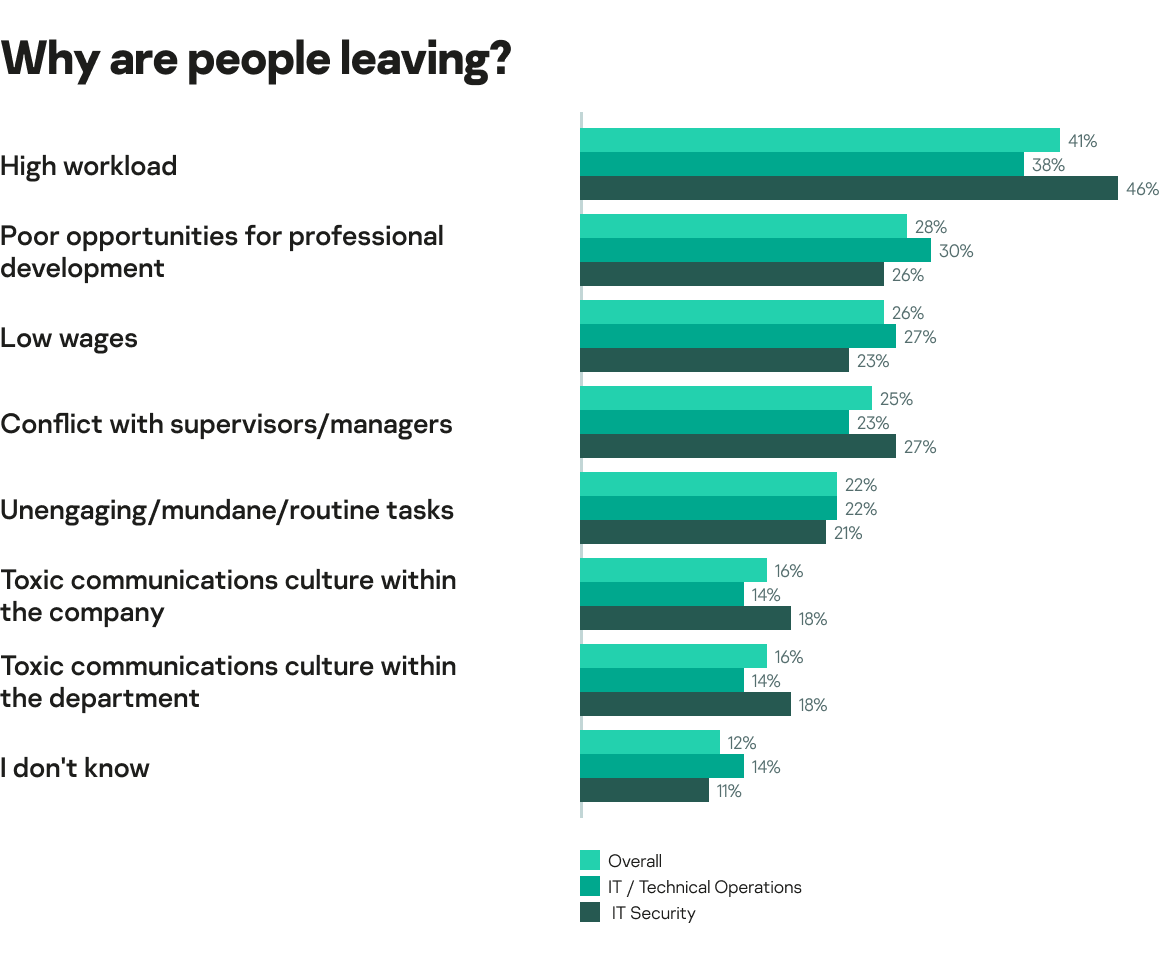
- High workloads (41% overall and 46% in IT security roles) is the primary reason given for leaving a department
- 69% of businesses are planning to use MSPs and MSSPs in the next 12 months. Among the main drivers are a need for special expertise and improved cost effectiveness (41%)
- IT security specialists spend as much as six hours each week on non-work activities. The most widespread distractions are reading news articles, watching YouTube or TV series’, and even exercising
- While more than half (66%) of threat intelligence analysts participate in a professional community, only 44% of them have ever shared their insights with peers
The composition of IT security teams
In order to gain a full understanding of the impacts of how cybersecurity is managed within organizations, and why certain behaviors occur as a result, it is important to first understand the make-up of IT security departments. The structure of IT security teams varies across different businesses, which informs a certain level of flexibility across capacities, capabilities, outlooks or team dynamics. These, in turn, may well dictate whether a managed (security) service provider (M(S)SP), enhanced training, structural changes or a change of strategy are required.
Perhaps unsurprisingly, there is a small difference between enterprises and SMBs in terms of having a dedicated IT security department, first and foremost. More than half (52%) of enterprises have this committed function, while only 45% of SMBs can boast the same capacity. Conversely, only 44% of enterprises have a security function that is managed as part of a wider IT department, compared to 50% of SMBs who rely on this particular set up.
“Optimal structure depends on the industry. Usually, in companies where acceptable risks are higher, cybersecurity is a part of IT. This can include manufacturing or hospitality, and mainly small businesses. In verticals where risks are critical and they are more regulated, cybersecurity often works as a separate department. In the latter case, the benefit is that it complies with the principle of segregation of duties, meaning that those who create IT systems and those who control their security are different people. Otherwise, employees who have left vulnerabilities may not be interested in finding and fixing them.
“However, in smaller companies, such separation can slow down processes. In IT companies, there is the option of a separate information security department which is responsible for the infrastructure, but an information security specialist is also included in each team responsible for development. And this option works well,” comments Andrey Evdokimov, Head of Information Security at Kaspersky.
Complementing the structure component is the sheer volume of employees directed towards IT security. Again, the statistics aren’t necessarily surprising, but they do underline the capacity problems that a smaller business, in particular, might face as infrastructures evolve and expand. A combined 58% of SMBs have 25 or fewer employees within IT security and 35% of these have fewer than nine. For enterprises the spread is much more even, with 14% containing as many as 250-499 employees across their IT security function; but similarly, 14% also only contain between 10 and 25.
“There are two ways to calculate the optimal size of an IT security department. In IT companies, it often depends on the number of computers, servers, etc. It can also be a percentage of the number of users, because it is the users who generate most of the events. In both cases, typically, the ratio is one security specialist for every 10 IT professionals,” adds Andrey Evdokimov.
Finally, it’s important to understand the specific arms and teams responsible for managing IT security across each organization. Enterprises are likely to be blessed with a CISO (46%), as well as additional tailored units including risk and compliance groups (46%), a security operations center (SOC) (20%), dedicated threat intelligence teams (16%), or a malware analysis team (14%).
“SOC requires at least five people to operate: two employees who are responsible for monitoring; one for investigation; a person who will combine the functions of an architect and an engineer; an administrator; and an SOC manager. This way, SOC would be able to cover business hours and five-day work weeks. For round the clock operations, one needs five employees for monitoring, two people for investigation, as well as an administrator and manager,” comments Sergey Soldatov, Head of Security Operations Center at Kaspersky.
The workload-turnover balance
The above capacity differences are vital as they inform the ultimate dynamics, behaviors, satisfaction or commitment of the workers involved. Historically in the sector, a lack of IT security specialists has been compounded by an ever-increasing number of expectations and tasks, to create an unfavorable cybersecurity framework. If people or teams are feeling overstretched then their enrichment and empowerment levels are likely to fall, causing an ultimate security concern should tasks not be completed effectively. It exposes the delicate relationship between human nature and technology.
You only have to look as far as the reasons why people have left organizations to make this connection and to see that the above trend is still a concerning factor. Beyond professional development stagnation, money, conflicts, or job role dissatisfaction, it is high workloads (41% overall and 46% in IT security roles) that the majority of people state as the reason for their colleagues to leave a department.
“Indeed, turnover is a pressing issue. There is a lack of IT security employees who are above average level, and especially experts and architects. It is a very good case if such a person has worked in the company for four-six years. That’s why I recommend to assess how people can be motivated to stay in a company at hiring stage. In my opinion, the best way here is to give new, non-standard tasks. When prospective employees are doing the same thing all the time, they will quickly get bored and leave.
“For faster onboarding, employees should undertake real tasks from the very first days of working. An approach where one initially reads the documentation and understands what they are working with, no longer works. Newcomers should be immediately involved in projects together with a person who will advise them, but they should have their own sphere of responsibilities. This ensures adaptation by letting employees feel that their contribution is valuable and important. And this helps both employee and employer find out whether they fit each other’s expectations,” comments Andrey Evdokimov.
“In SOC, shift work helps to avoid overworking. Good working conditions, including high wages and benefits, social programs, a healthy corporate culture and relationships in the team, also contribute to retention.
“Of course, staff can still leave the company. To quickly adapt new employees, a specific onboarding plan is needed: what to read, and what courses to watch (for example, we record internal seminars and these recordings are then available to new team members). And for sure, it is necessary to involve an employee in real tasks as early as possible with a dedicated mentor who will help to analyze difficulties,” adds Sergey Soldatov.
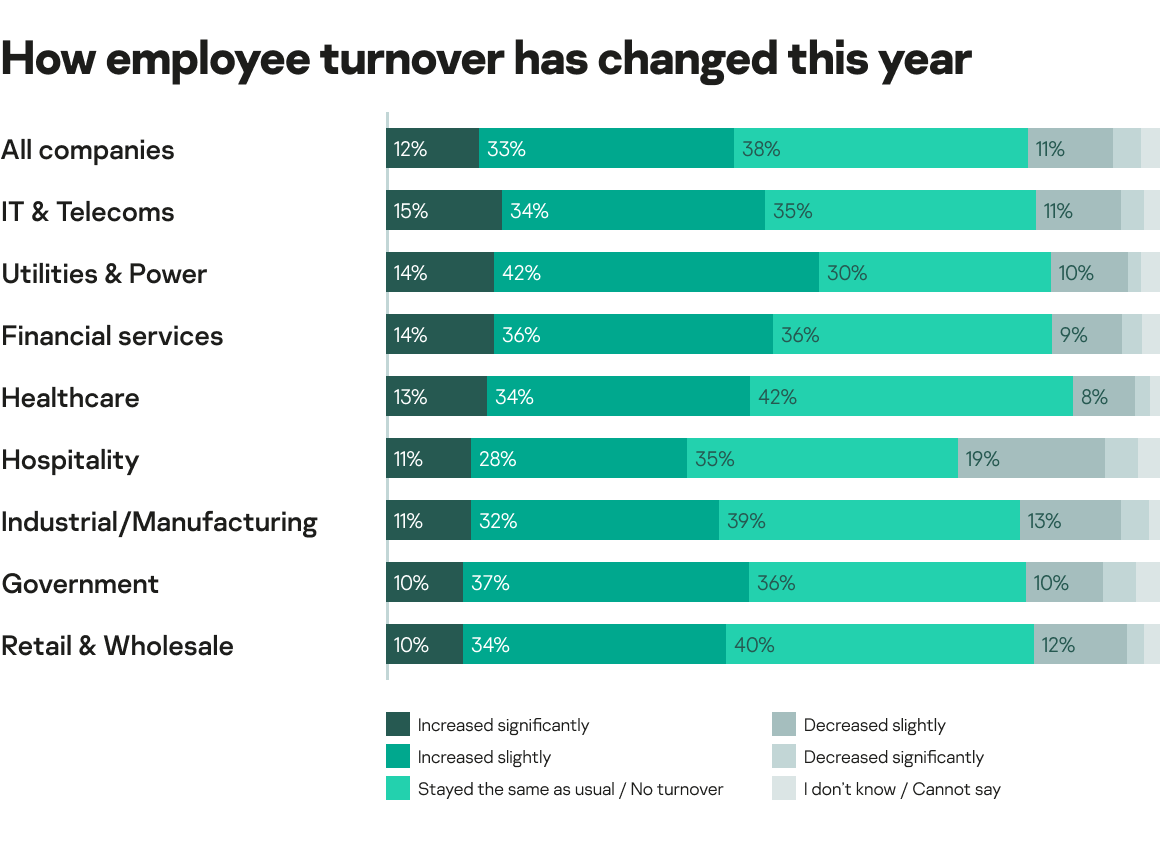
The problem is exacerbated further when analyzing that employee turnover across 45% of all companies is estimated to have increased over the past year, while only 12% have noted a decrease in turnover. Perhaps ironically, IT and telecoms organizations are actually ahead of this curve, with 49% of IT teams in this sector experiencing that same increase in turnover.
The vicious cycle element comes from the fact that an increase in turnover adds extra strain to existing employees’ workloads – the very factor that is forcing that extent of turnover in the first place. Almost two-thirds (61%) of businesses reported at least some – if not a significant – increase in IT or IT security workload as a result of employee turnover. And the departure of key workers contributes additional strains. For instance, as many as 56% of companies have experienced a situation where employees don’t return their corporate devices after departing, while 51% have had cases where ex-employees actually used corporate data after leaving, to the extent where it went public and caused reputational damage. Therefore, it’s clear that the workload issue’s trigger effect needs addressing.
Is outsourcing the answer?
It’s not all doom and gloom, however. That cycle can be reversed. And many are realizing that a way to do so is to relieve pressure from their teams through outsourcing. While this development has yet to take hold across the IT security landscape at present, respondents are at least acknowledging the issue at hand, and the role that an MSP or MSSP might play in supporting them.
As many as 69% of organizations across the board are planning to use an MSP or MSSP over the next 12 months. While this may indeed benefit the workload-turnover balance, that isn’t necessarily the rationale behind organizations’ outsourcing efforts, however. The majority (71%) actually stated that they think outsourcing could reduce security-related costs. This figure is compounded by 22% (SMBs) and 26% (enterprises) who actually stated outsourcing IT security functions as a top reason for reducing their IT security budgets.
“It is more efficient to do unique tasks yourself, and outsource typical standard activities. Also, if a company has a high level of internal competence and provides great effectiveness and efficiency, this task should not be given to third party. On the contrary: if a company doesn’t know how to do something productively, it may be worth outsourcing it to subcontractors. However, take into account that in a high-tech service, to understand and evaluate outsourcers’ work, a company should have some expertise in this field.
“When choosing an MSSP, I would advise to pay attention to references, to confirm outsourcers’ expertise. For an MDR provider, I recommend to consider the following factors: the number of customers (the more customers, the more experience the provider has), a large research potential confirmed by their own research, and usage of their own tools,” comments Sergey Soldatov.
“Commonly, SOC and forensic, training, security assessment, TI analysis, consultations on data legislation in various countries, audits, and preparation for certification are outsourced. In general, if it is a narrow specialization, it’s worth outsourcing to third parties. Development, change and implementation of IT security systems – e.g. firewalls – can also be subcontracted. However, it’s not recommended to outsource management of these systems, as there are risks that security could be compromised,” adds Andrey Evdokimov.
However, 41% did also list requirements of special expertise among their prime reasons for using M(S)SP security services, as a sign that the employee and skills element is also a prominent factor. Other reasons on top of financial effectiveness and specialty requirements included the complexity of business processes (41%), scalability (34%), compliance requirements (38%) and the efficiency of delivering cybersecurity solutions (50%); further indicating that organizations are assessing M(S)SP usage beyond the cost factor. However, this whole consideration is still very much a burgeoning recognition – only 2% of both SMBs and enterprises are currently involving an outsourced managed service provider or managed security service provider in their IT security operations.
“MSSP usage is limited now and very few businesses decided to completely outsource security. This can be expensive due to the fact that processes in the organization are not standardized, and because there are legacy systems. So, third-party contractors will need to understand these specific environments, which increases the cost. With the expansion of cloud applications and standardized systems, more business will completely outsource cybersecurity,” adds Andrey Evdokimov.
All in a day’s work
We have established that an overworked team may not always enjoy or remain in their roles as long, but how does it affect their day-to-day productivity? It is important to also assess the ways in which people display their displeasure, rather than just labelling them ‘stressed’ or ‘unfulfilled’ or ‘overworked’.
In this case, we set out to establish the human behavior side of this dynamic more thoroughly. To explore the routine of IT security specialists gives even more insight into what tasks they’re solving when hard at work, what they like to do when they’re on their breaks from that work, and to what extent those lines become blurred. The shift to working from home may have also made it more difficult to distinguish personal and working time.
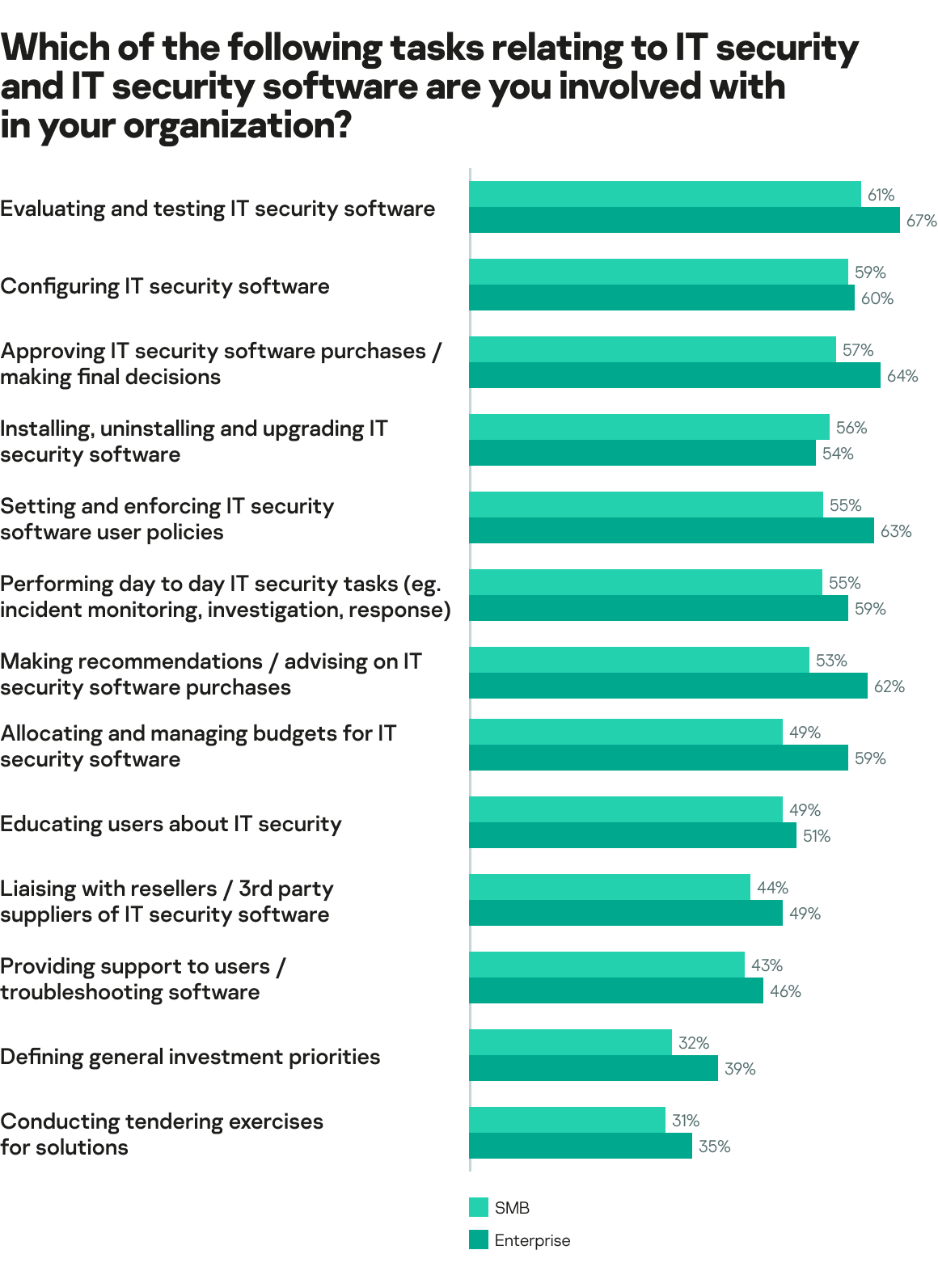
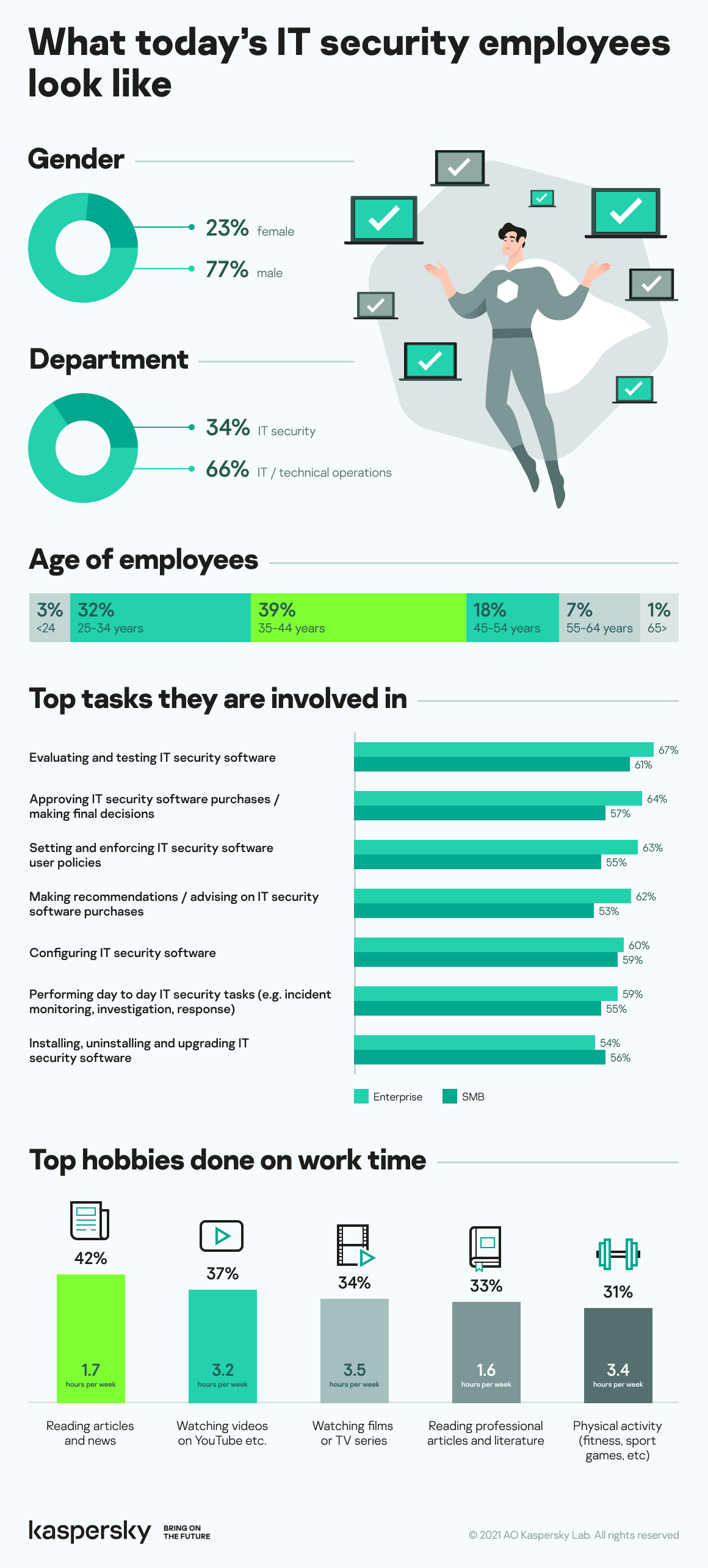
Firstly, addressing the more formal business side of the equation, employees from both SMBs and enterprises were asked to establish the key tasks relating to IT and IT security that they were involved in.
Presented in order via the below tables, there are familiarities across the two spectrums in that the evaluation and testing of IT security software topped the charts in both cases. For enterprises, key activities were then to approve IT security software purchases and to set and enforce IT security software user policies. For SMBs, while they are also largely tasked with approval of IT security software purchases, they also participate in the installing, uninstalling and upgrading of IT Security software more than in enterprises.
Analyzing more generally, and higher percentages in nearly every case were seen across enterprises, which is perhaps a surprising statistic. The general thought might be that SMBs need to share resources and merge task remits more than larger companies, and this perhaps suggests that those larger enterprises are still learning how best to deploy specialist skills as part of the overall function.
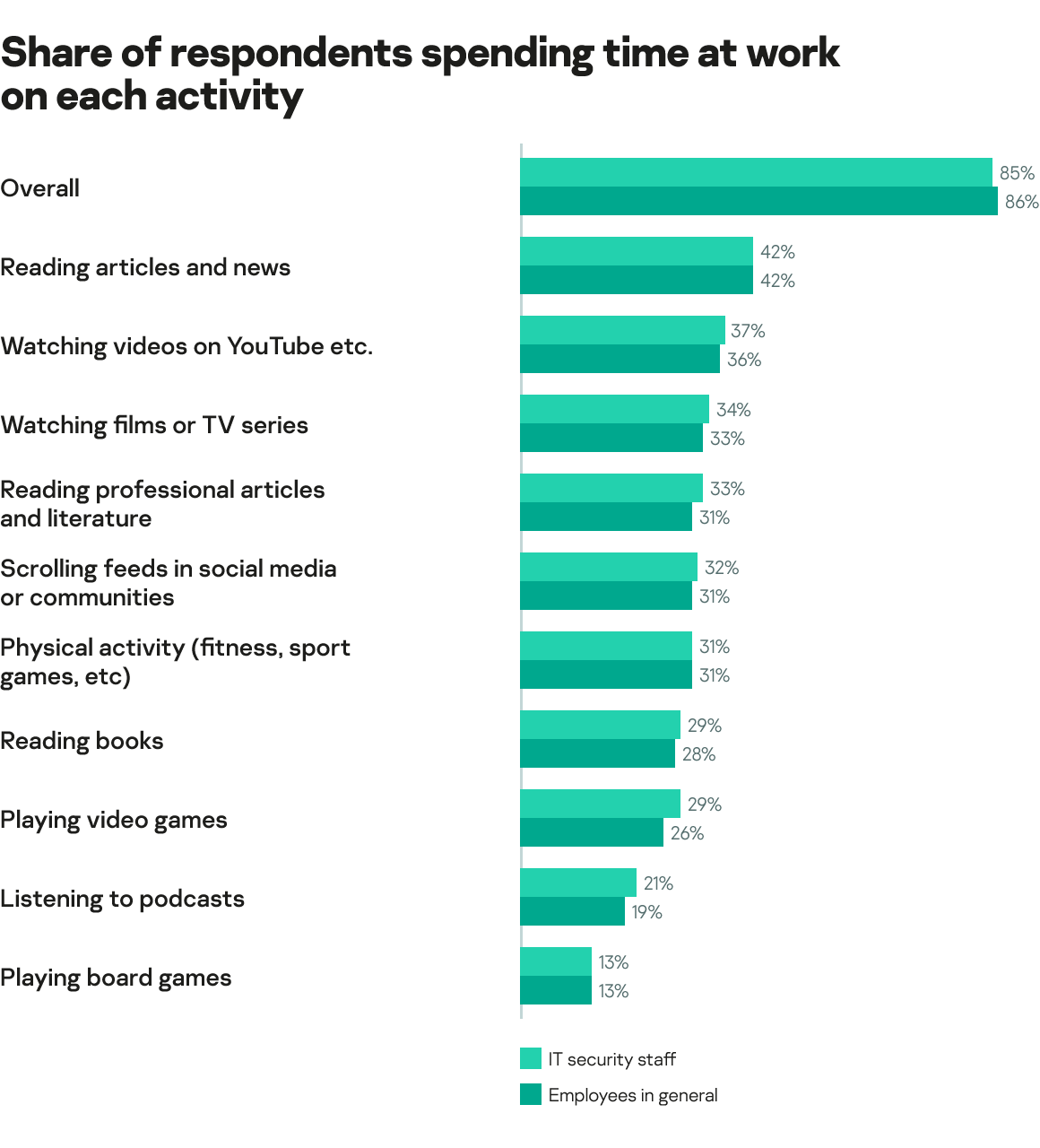
Then comes the ‘off-duty’ elements. Or, more appropriately, the ‘non work elements while on-duty’, based on the findings among respondents. As many as 86% of all employees, and 85% of IT security staff, admitted that they spend time at work engaging in at least one form of non-work activity. Typically, IT security employees spend six hours on this (median value was used. Median separates a sample in a way that one half of respondents chose option that is larger than it and the other half chose smaller one. We used this method to depict a typical routine, as the average number was heavily affected by the few people who spent much working time on their hobbies). Hobbies being undertaken during work hours among IT security employees include reading the news (42%), watching videos on YouTube (37%), watching films or TV series’ (34%), doing physical exercise (31%), or even playing board games (13%). The overriding reason given across both levels of organization was that they needed a break between work tasks (48%). This number was highest (52%) among enterprises, supporting the earlier idea that larger organizations haven’t quite worked out how to distribute people’s time and efforts yet.
“I don’t think it’s an issue that an employee is distracted when working remotely. The workday has become longer, so people really need a break. And working hours are now very much blurred – we can start working earlier or some tasks can be postponed to non-working hours if it is more convenient for an employee. It’s completely fine if an employee watches a movie during working hours, and if they then do the work in the evening. There should be control over task performance, not how many working hours are spent on a hobby. In addition, it may be normal for people to watch YouTube, as it may give insights into how to solve a problem. It is also worth giving employees interesting tasks so that they do not burn out. If work is not interesting for someone or if there is a lack of task management, an employee will find a way to do something different, even from the office,” notes Andrey Evdokimov.
“Employees should have goals, KPIs, objectives and metrics that characterize the quality and speed of their work. If performance is not affected, there are no problems with the fact that a person is distracted from work. If efficiency has fallen or differs from colleagues, it should be paid attention to. The aim of the manger is to inform employees about poor productivity as early as possible so they can find ways to solve the issue,” continues Sergey Soldatov.
Sharing is caring
Human behavior can be channeled in many different ways. As we’ve already documented, some individuals’ attitudes or tendencies are quite industry-general, with the notion of overworking leading to discontentment quite familiar. However, there are also aspects of business behavior that directly concern the sector you operate within. From a cybersecurity perspective this led to analysis into how companies perceive their own levels of professional responsibility.
Having access to the most up-to-date information regarding threats is, of course, critical for a security department. This is why more than half (66%) of respondents with threat intelligence analysis responsibilities participate in a form of professional community. It includes subscription to vulnerability databases (61%), taking part in professional forums and blogs (45%), as well as receiving threat intelligence from paid (42%) and free (33%) feeds.
However, when it comes to the notion of sharing, another interesting aspect of team behavior comes to the fore – a preference among organizations to keep their workers’ findings secret, rather than share them. Half of respondents (52%) said their employers did not permit them to share threat intelligence insights with external communities. This means that fewer than half (44%) had actually shared potentially critical insights beyond the confines of their own business – 77% of those who were permitted to do so, and 8% of those who were not.
“Of course, there is a need to share threat intelligence. It includes not only indicators of compromise such as hashes or C&C servers, but also the tactics and techniques, motivations and typical penetration vectors, etc. Any information about a threat will help your peers to investigate an attack and plan an effective response.
“However, there must always be a balance. It’s just like in a criminal investigation – once underway, everything must be kept secret so that the perpetrator does not disappear. And when it is clear who committed a crime, the entire organized criminal group must be immediately caught. Likewise, in the cyber world, until you know whether a response’s actions will be successful or not, you can’t reveal that a company is doing something, since attackers will easily understand that they were detected and go underground,” explains Sergey Soldatov.
“It is worth adding that when you find a first piece of information but do not figure out that the attack was mitigated, publishing something gives a clue to attackers regarding what you know about them and they can adapt their work. Once you have all the information, you need to share it,” agrees Andrey Evdokimov.
Bringing this finding back round to the department’s dynamics, it has also been found that external help can decrease workloads. Among those who have ever asked internal communities for help, 41% revealed that a high workload was the eventual reason they left the business. Keeping critical threat intelligence secret not only harms the information being circulated in the wider sector but it also avoids the opportunity to relieve stress from your team.
That being said, it is still vital that threat intelligence analysts are able to discover and study new malicious objects, even if their peers are not able to share findings. Free access to the Kaspersky Threat Intelligence Portal allows this to happen. It also provides a private submission mode to ensure that information about shared samples will be not available to other community members.
The changing face of IT security
As illustrated throughout this report, when it comes to the IT security specialty, the road to improvement begins with a change of mindset or prioritization. And we are already seeing proactive signs that will hopefully create a positive snowball effect to undo some of the more negative aspects highlighted.
More so now than ever before, signals of intent are being made explicit. Almost three-quarters (71%) of all businesses believe that investments into IT security will grow over the next three years. Even more importantly, the reasons for doing so and the implications on the workers themselves seem to be gaining precedence. Among those earmarking future increases in IT security investment, 39% of SMBs have stated improvements to internal specialist expertise as the main reason. This number rises to 41% among enterprises, which is a very encouraging sign given the current crossover of task allocation that currently exists.
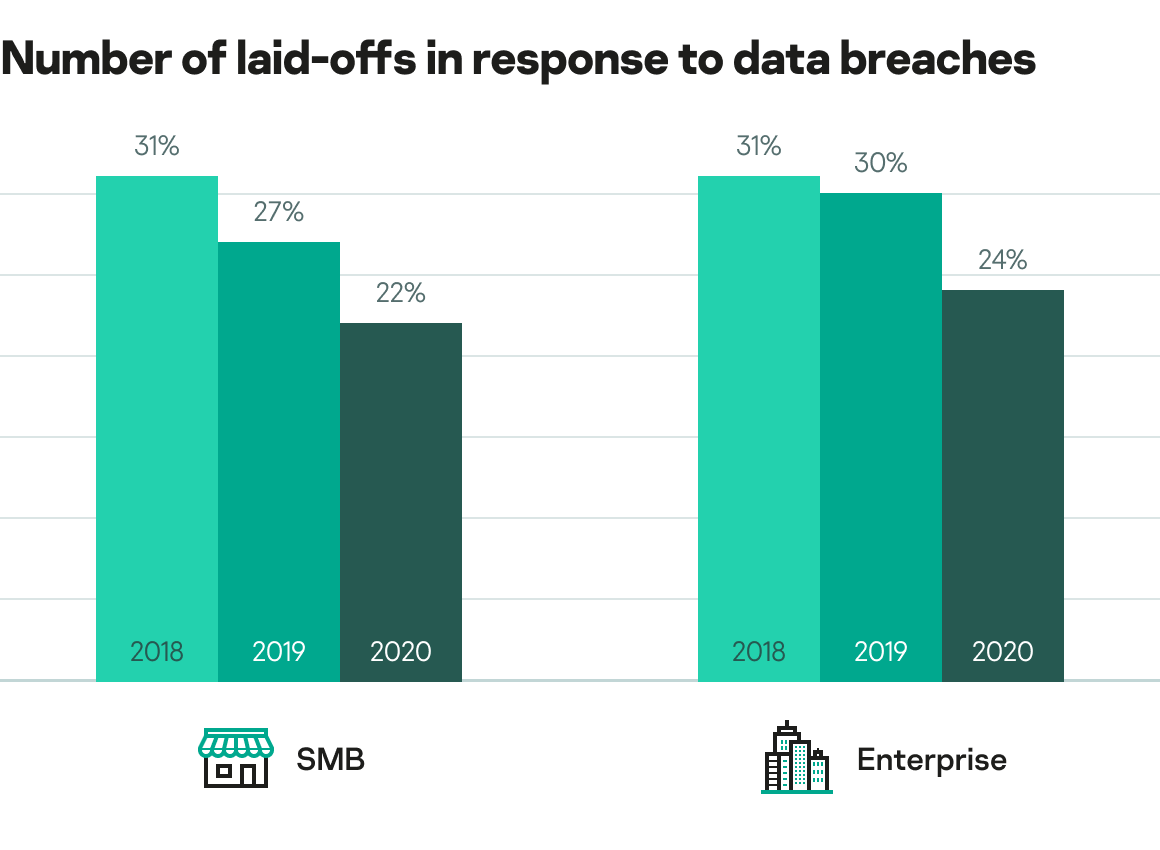
Final evidence of a change in attitudes can be found across companies’ loyalty towards workers. Even following a data breach, the reaction of laying off employees has dropped for both SMBs and enterprises. Fewer than a quarter (24%) of enterprises would now lay off employees in response to a data breach, in comparison to 31% in 2018, while only 22% of SMBs would take this course of action now compared to 31% two years ago. Across the board, this suggests a preference towards upskilling, self-reflecting and a strive for improvement, rather than changing personnel in the hope that it won’t occur again in the future.
These may seem like small, incremental changes, but the knock-on effect could be significant. Just as the aforementioned negative cycle can be started by a lack of employee empowerment, the opposite effect can be achieved by these gestures of positivity. By harnessing the best of human nature, the result can be a more structured, transparent, collaborative and secure business landscape in the years to come.
To find out more and learn from Kaspersky’s other IT Security Economics reports, follow #securityeconomics on social media.