In December 2013 information security incidents proliferated, unfortunately. Even if the number of incidents remained within the average values, their significance, alas, was not moderate. The interests of millions of people were potentially affected. The essential number of the incidents were linked to the Tor network and the Bitcoin virtual currency which have been lately drawing much attention of cybercriminals. But first things first.
A Stuxnet with bigger claws
The infamous cyber weapon Stuxnet turned out to have an earlier and far more aggressive, stealthy, and dangerous version. In late November Ralph Langner, a renowned ICS/SCADA expert and one of the first investigators of the virus, published an analysis of malware Stuxnet 0.5 created as long ago as in 2005, but discovered as late as in February 2013 by Symantec specialists. The malware, like its better-known successor, was written to inflict damage on the rotors of centrifuges for uranium enrichment. But it acted another way, so that the destruction in its case would be enormous. It is hard to explain why a less aggressive version of Stuxnet was deployed eventually. Langner suggested it had been done for political reasons.
The full version of Langner’s report is available here.
Tor, bitcoins and malware
In late November a new crimeware toolkit Atrax was reported, it was cheap (about $250) and multifunctional. Among its features there were extracting information from the browser, mining bitcoins and implementing DDoS-attacks. A few commercial additions have already been written for it including a stealer plugin, an experimental bitcoin mining addition, a form grabber. All of them are costly and sold like Atrax for bitcoins only. Atrax is characterized by utilizing the Tor network for communications; moreover, the kit doesn’t use “suspicious Windows APIs”.
Details are available here.
A zero day belated
Researchers detected attacks targeted at a previously unknown vulnerability of… Windows XP. The vulnerability is also present in Windows Server 2003, but so far a zero day exploit was found only for Windows XP. The exploit allows raising the user’s privileges. Doing it just remotely is impossible, but if the system control has been somehow taken over, this bug can be used to run malicious software and for other attacks.
The detected exploit is distributed as a malicious PDF file to be opened to load malware.
Zombie drones
Shortly after Amazon had announced the prospect of using drones to deliver the goods it was reported that the control of drones can be remotely intercepted. Researcher Samy Kamkar already developed drone-hijacking program called SkyJack. SkyJack is a drone engineered to autonomously seek out, hack, and wirelessly take over other drones within WiFi distance. To date, a Parrot drone that Samy Kamkar modified, is only able to hijack similar Parrot AR 2.0 drones.
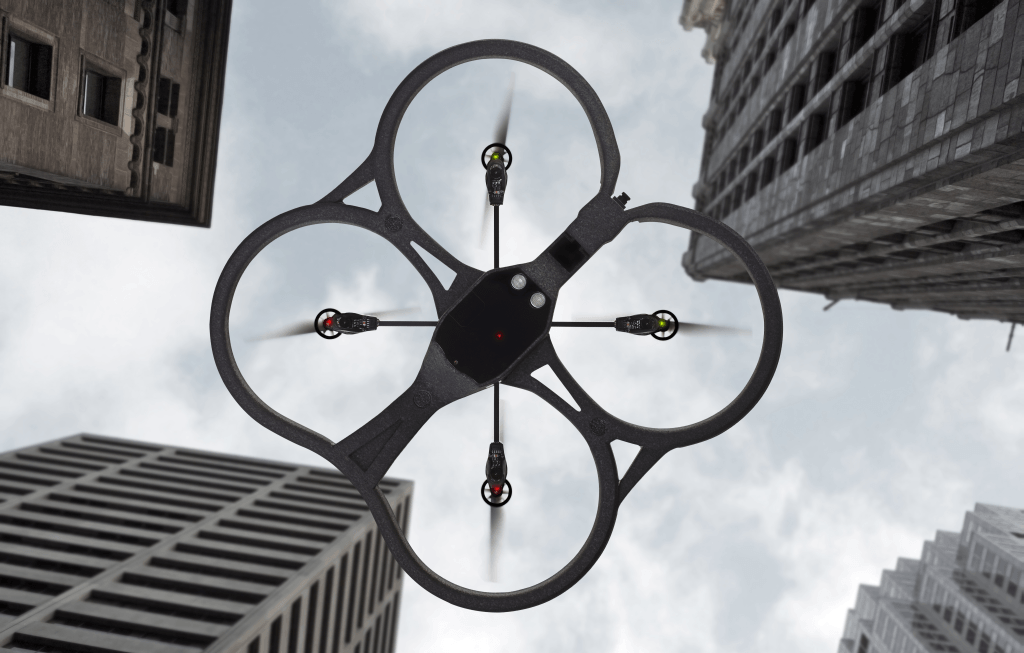
On the software side, Kamkar’s SkyJack buildout calls for the aircrack-ng key-cracking program, which can forcibly disconnect a target drone’s WiFi connection. After that happens, Kamkar’s drone-strike software connects to the drone using the node-ar-drone JavaScript library, which can be used to communicate with and control any Parrot AR Drone 2.0.
Details are available here.
Alarm! Bitcoins leak!
In the first half of December another malware was reported to be associated with bitcoins. Bitcoin Alarm disguises as a utility alerting of the updated BTC exchange rate. It is actually a intricate Trojan designed to steal authentication information and (presumably) bitcoins, too.
A long time ago in a galaxy far, far away….
Alas, the Tor network is often used by hackers since anonymity is dear to them. Researchers at Kaspersky Lab’s Global Research and Analysis Team announced of detecting another malicious campaign nicknamed ‘Chewbacca’.
The ‘Chewbacca’ malware finds running processes on compromised computers, reads process memory, drops a keylogger and is able to move that information off of infected machines.
More information is available here.
The senseless and merciless ZeuS
 The infamous bank Trojan ZeuS started attacking 64-bit systems. Kaspersky Lab’s researchers detected a new version of this malicious program that behaves almost like its 32-bit fellow. It also uses web injections to steal banking details and withdraw money from the accounts, steals digital certificates and can intercept keystrokes. The main difference is that this version of ZeuS works in the anonymous network Tor.
The infamous bank Trojan ZeuS started attacking 64-bit systems. Kaspersky Lab’s researchers detected a new version of this malicious program that behaves almost like its 32-bit fellow. It also uses web injections to steal banking details and withdraw money from the accounts, steals digital certificates and can intercept keystrokes. The main difference is that this version of ZeuS works in the anonymous network Tor.
It is a mystery why attackers needed a 64-bit version at all as only less than 0.01% of users use 64-bit Internet Explorer (and the main purpose of this Trojan is intercepting and changing information in the browser). Apparently, it is some marketing gimmick.
800,000 people impacted
In early November someone broke into the offices of Horizon Blue Cross Blue Shield of New Jersey engaged in health insurance services. The thieves stole two laptops containing the sensitive information of more than 800,000 customers.
The machines were locked to an employee workstation inside Horizon’s Newark headquarters but that cable-locks were not enough to prevent the theft. Horizon Blue Cross Blue Shield of New Jersey said that the laptops are password protected but also admitted that they had failed to encrypt them, which can mean big problems for the aforementioned 800,000 customers.
Target is targeted
Retail giant Target confirmed Thursday that some 40 million customer credit and debit accounts may have been compromised in a breach of its online customer data.
The data theft took place from Nov. 27 to Dec. 15, according to Target, and “may have impacted” 40 million customers. The company has not officially said how the breach occurred, but many experts suspect a compromise of the point-of-sale systems data at brick-and-mortar stores because Target said its online business “was not affected”.
The retailer said it notified authorities and financial institutions immediately after it was made aware of the unauthorized access, and had hired a forensics team to thoroughly investigate how the breach may have happened. The issue that allowed the breach has been identified and resolved, according to Target spokeswoman Molly Snyder.
There is not much official technical information about the incident, but the mere fact urges to protect user transactions in all possible ways, implying that there can never be too many precautions. Obviously, a large network like Target takes special care of protecting its IT perimeter, but a flaw in the defense was found anyway. The smaller retailers and individual shops which spend far less on IT security may be a great deal more vulnerable, hence their customers are vulnerable, too.

 Security digest
Security digest

 Tips
Tips