To steal corporate e-mail credentials from company employees, attackers must first get past the antiphishing solutions on the company’s e-mail servers. As a rule, they use legitimate Web services so as to evade notice, and increasingly, that means Google Apps Script, a JavaScript-based scripting platform.
What is Apps Script, and how do attackers use it?
Apps Script is a JavaScript-based platform for automating tasks within Google’s products (e.g., creating add-ons for Google Docs) as well as in third-party applications. Essentially, it’s a service for creating scripts and running them in Google’s infrastructure.
In e-mail phishing, attackers use the service for redirects. Instead of inserting the URL of a malicious website directly into a message, cybercriminals can plant a link to a script. That way, they can bypass the mail server-level antiphishing solutions: a hyperlink to a legitimate Google site with a good reputation sails through most of the filters. As an ancillary benefit to cybercriminals, undetected phishing sites can stay up longer. That scheme also gives attackers the flexibility to change the script if necessary (in case security solutions catch on), and to experiment with content delivery (e.g., sending victims to different versions of the site depending on their region).
Example of a scam using Google Apps Script
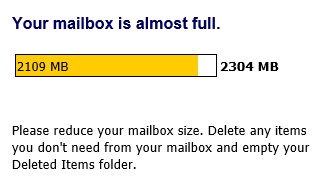
All the attackers have to do is get the user to click a link. Recently, the most common pretext was a “full mailbox.” In theory, that seems plausible.
In practice, attackers are usually careless and leave signs of fraud that should be obvious even to users who are unfamiliar with real notifications:
- The e-mail is apparently from Microsoft Outlook, but the sender’s e-mail address has a foreign domain. A real notification about a full mailbox should come from the internal Exchange server. (Bonus sign: The sender’s name, Microsoft Outlook, is missing a space and uses a zero instead of the letter O.)
- The link, which appears when the cursor hovers over “Fix this in storage settings,” leads to a Google Apps Script site:
- Mailboxes do not suddenly exceed their limits. Outlook starts warning users that space is running out long before they reach the limit. To suddenly exceed it by 850MB would probably mean receiving about that much spam all at once, which is extremely unlikely.
In any case, here is an example of a legitimate Outlook notification:
- The “Fix this in storage settings” link redirects to a phishing site. Although in this case, it’s a fairly convincing copy of the login page from Outlook’s Web interface, a look at the browser’s address bar reveals that the page is hosted on a counterfeit website, not in the company’s infrastructure.
How to avoid taking the bait
Experience shows that phishing e-mails do not necessarily have to contain phishing links. Therefore, reliable corporate protection must include antiphishing capabilities both at the mail server level and on users' computers.
Additionally, responsible protection needs to include ongoing employee awareness training covering current cyberthreats and phishing scams.
 phishing
phishing



 Tips
Tips