The story behind the post is plain and simple: yet another bad guy or a group of bag guys have decided to spread their malicious browser extension using Facebook. While their methods are blunt and obvious, a whopping 17k (and counting!) users have been caught into this scam.
Let us take you through the infection method step by step and ask some questions along the way. Please, answer them honestly. In the end we’ll see if you may have fallen victim to a scam like that before reading this post. You sure wouldn’t after.
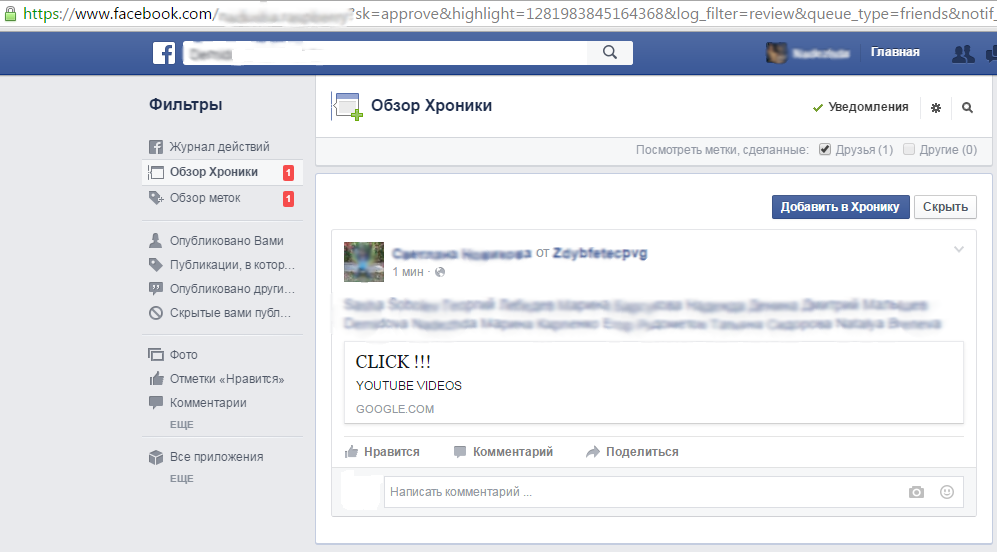
So, the malefactor starts by hijacking several Facebook accounts. On their behalf the criminal posts a link to something that is supposed to be a YouTube video suitable for adults only. The bad guys also tag about a dozen friends of each of those accounts. The resulting post looks like that:
Question #1: Would you click on that link?
Now if you said no, we suggest that you develop some useful, good paranoia. If a freind of yours wanted you to click on a link, he would surely give you a better description as to why you should click.
If you see a post like that, your useful paranoia will suggest that it’s 99% certain that there is something wrong with it. There are two possible solutions: either do not click on the link, or click and be extremely cautious about what you do next.
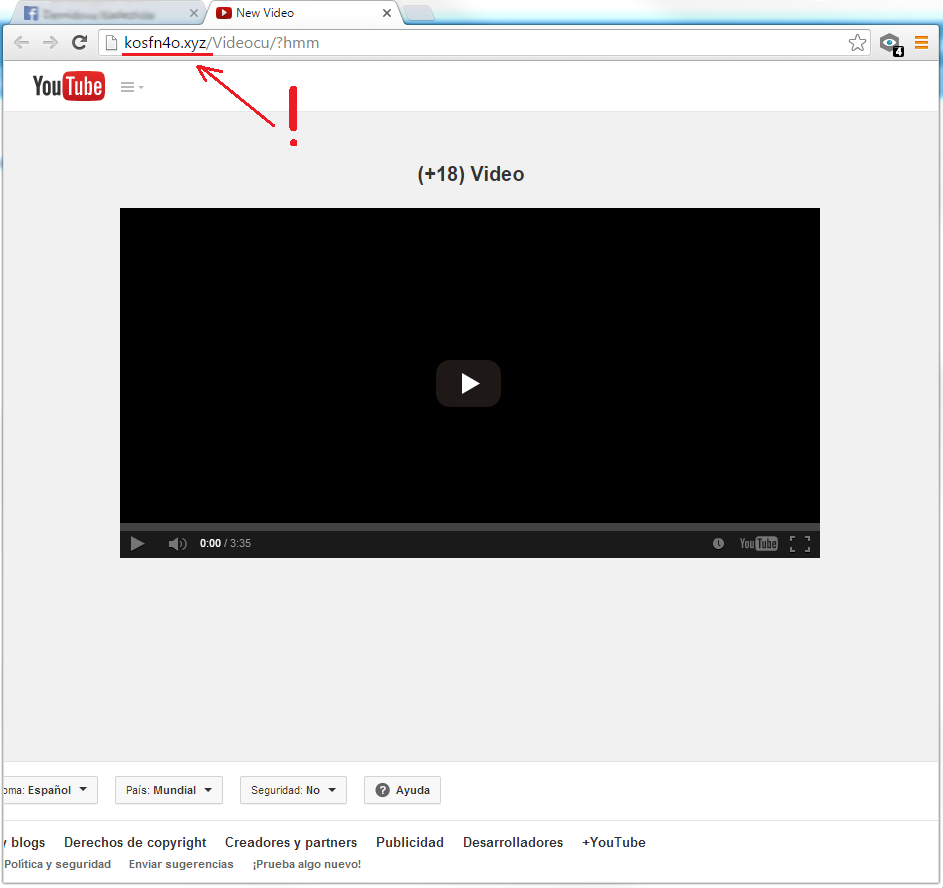
It turns out that more than 17k people actually clicked. The link brings you to the site with an embedded video. The site looks like that:
Question #2: Does that site look like YouTube to you?
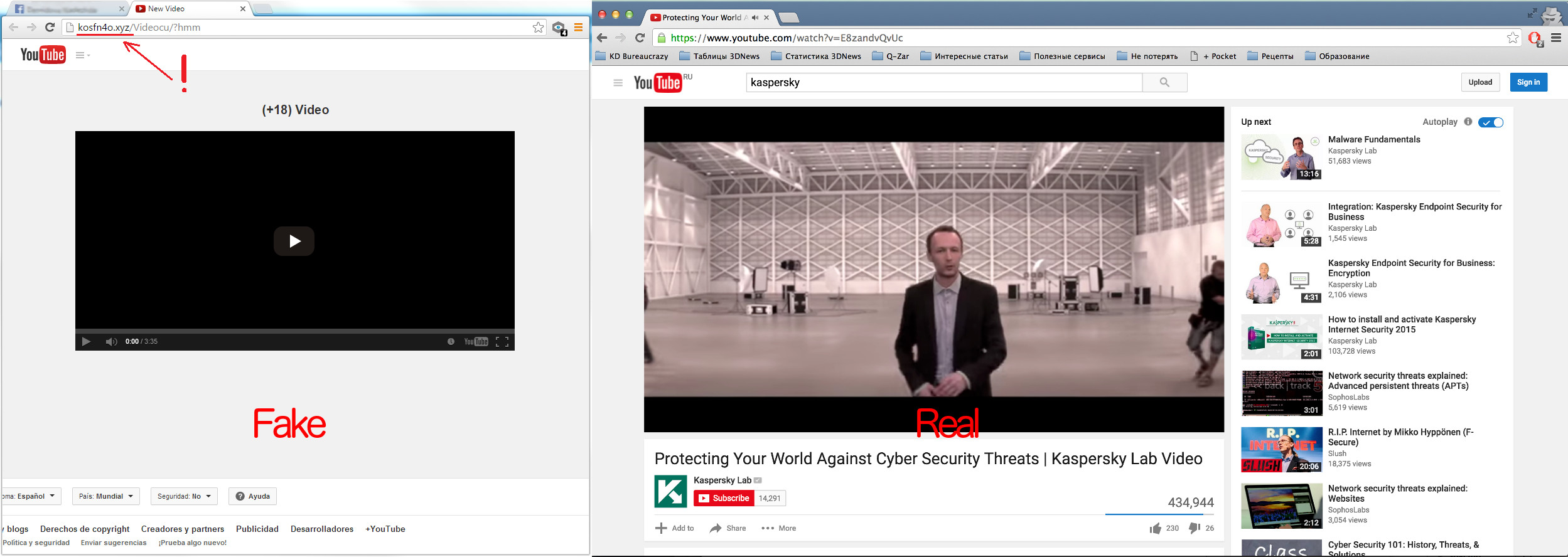
Well, the best way to answer that question is to compare the actual YouTube page and that page. Like that:
Ouch, that wasn’t YouTube. The real YouTube seems to have more a lot more content on the page, and a quick look at the webpage’s address could have solved all of your doubts. So if that page is not YouTube, why would someone try to design it to look as if it was YouTube? The answer is plain, simple and bitter tasting: to fool someone and to cause them harm.
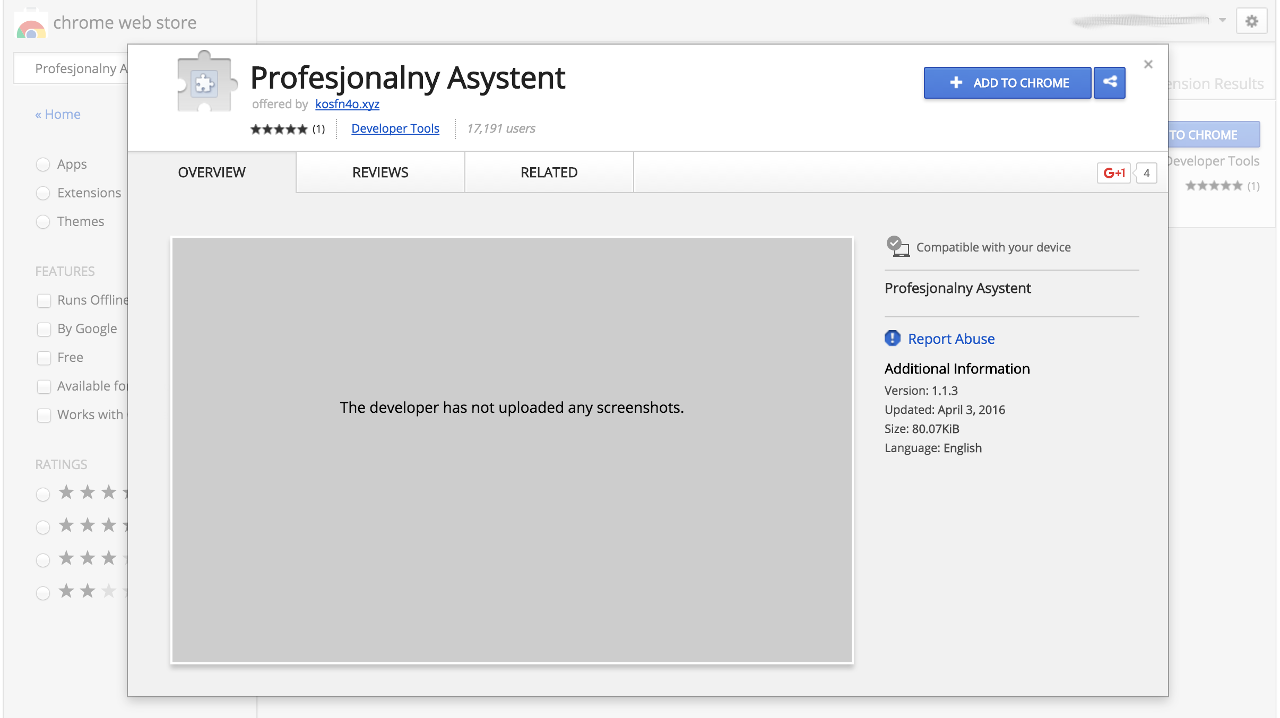
The video would not play, and the page would suggest that you install a browser extension in order to play it (in this particular case the extension was called ‘Profesjonaly Asystent’, which means ‘Professional Assistant’ in a rather bad Russian transliteration).
Question #3: If a page suggests that you install a browser extension, would you do that?
We’ll spoil “surprise” for you: the extension is malicious. Please, don’t install it. A few hours before that publication went online Google has finally removed the extension from the Chrome Web Store. But it has been there for almost a week – with no description, no screenshots and only one rating (probably, the developers themselves have rated it with 5 stars of 5). This extension does not tell you what it does — so why would you install it?
When installed, that extension has access to all the data the user inputs in their browser, including their logins, passwords and credit card information — as soon as they type it in on some site. So the extension steals that data.
The other thing it does is posting the same link to the same video on the victims Facebook page and thus continuing to spread the malware.
So, there were three moments when being a tiny little bit paranoid could have saved a user from losing their private data. Maybe calling it paranoia is too much, maybe we’d better call it common sense. So, now you know what to do in order to avoid this particular infection. But there are others of its kind. What can you do to stay protected?
7 simple steps to avoiding Facebook #phishing attempts – https://t.co/Qj68bST6HQ pic.twitter.com/V6rinEa2jI
— Kaspersky (@kaspersky) April 24, 2015
1. Learn about the types and variations of Facebook scams. There are several typical methods how the malefactors can try to trick you into installing something on your device — you’d better know these methods and not fall for them.
2. Check the list of installed browser extensions. Are you sure you know what each of them is for? If there are some unknown extensions — be sure to get rid of them.
3. If you see a friend of yours post something like the thing described in that post, please, notify them. They probably got hacked and we believe they would be grateful that you’ve warned them.
4. Install a good security solution. Kaspersky Internet Security detects malicious browser extensions and deletes them before they can do any harm to you.
 18+
18+

 Tips
Tips