Have you ever wondered why computer viruses are called just that – ‘viruses’? Well, actually, today the word viruses is used somewhat misleadingly to refer to most ‘any type of malicious program, or is used to describe any bad thing that a program does to a computer’. I took that from our encyclopedia, btw.
However (still from our encyclopedia), ‘strictly speaking … a virus is defined as program code that replicates‘ and spreads – much like a biological virus like, say, a flu virus does.
The strange thing is – viruses defined as such all but disappeared umpteen years ago out in the wild. These days it’s all about malicious programs that don’t so much replicate as have really nasty functionality that might steal data from a computer or totally wipe that data: for example, a Trojan. Yet still to this day, if you ask someone to put ‘computer security technologies’ into images, most often those images will show things like scientists in lab coats hazmats conducting quarantine shut-downs, test tubes in hand – though those are only needed when dealing with biological viruses.
So, you get it: computer viruses have died out. But the methods of analysis that were used for their detection and disinfection (eek: one more faux-import from the microbiology world!) remained, kept developing, and are still to this day helping tremendously in the fight against modern-day viruses malware. One such ‘old school’ technology is the emulator.
Briefly, emulation is a method for uncovering previously unknown threats, whereby a file that’s acting suspiciously (unusually, atypically) is launched in a virtual environment (’emulated’ environment) that imitates a real computer. Once there, the antivirus* observes the behavior of the file (on the fly; more on this later on) and if it finds any dangerous activity, it isolates it for further investigation.
Can you see the analogy with microbiological virology? Why inject a patient who may have a certain disease with a potent antidote with lots of side effects, when the patient may not have it at all? Better to emulate it in vitro and see what’s really afoot first; then administer the appropriate medicine.
The main challenge though is the same as in microbiology: it’s crucial to make the emulated environment resemble a real one as closely as possible. Otherwise malicious files might realize it’s a set-up and act all innocent as a consequence. Well we’ve been doing emulation for several years decades now, so – without any undue false modesty – we really are way ahead of the competition on this. We got this!
The first emulator in the world was developed by moi back in the DOS era in 1992. Soon experts around the world started to rave about the detection rate of our antivirus (yes – back then it was still an ‘antivirus’), which ripped up the competition in independent tests, partly thanks to the emulator.
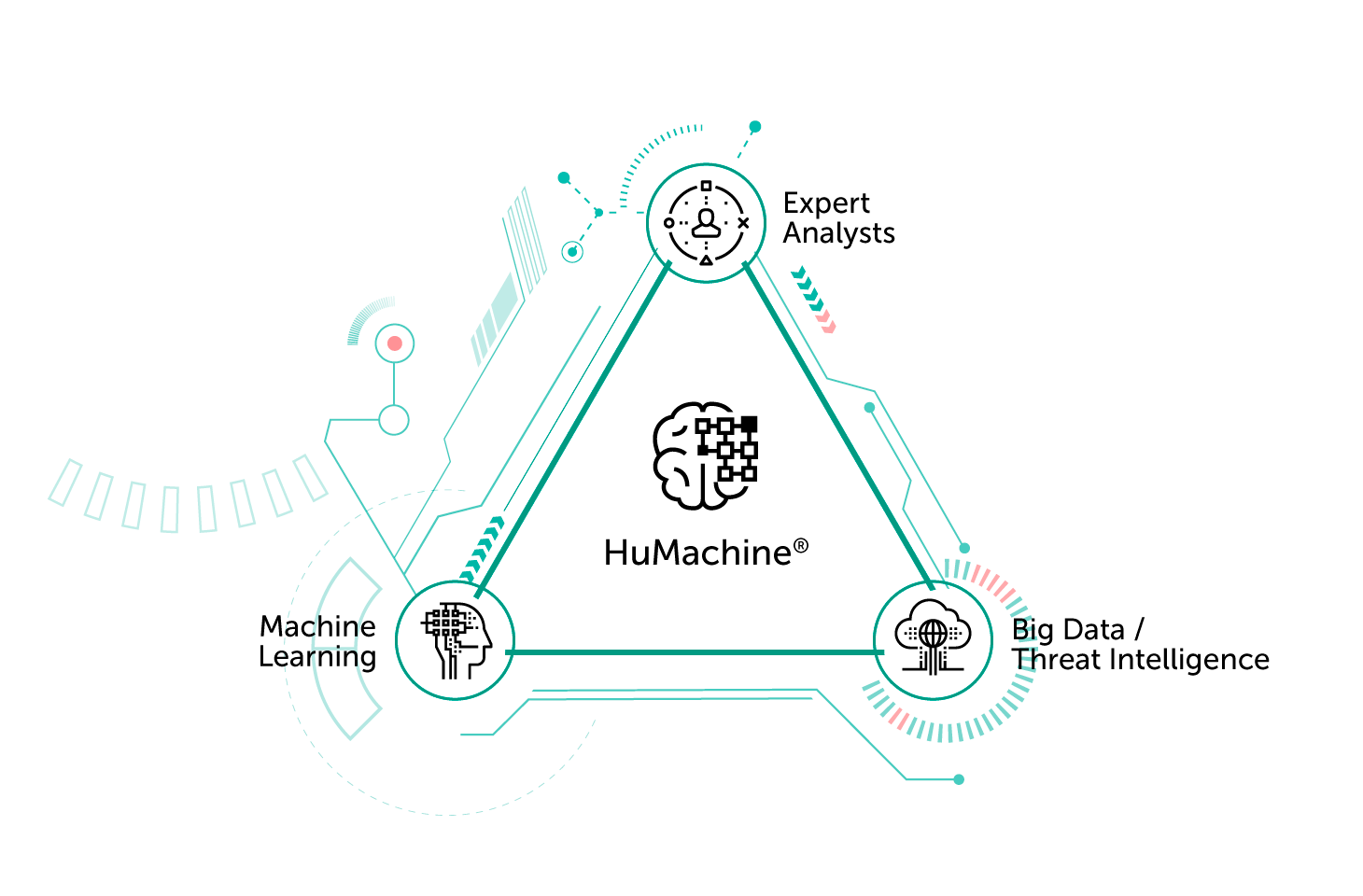
Time passed, and the threat landscape started to get more complicated: viruses generally left the stage, replaced by network worms, Trojans and other complex pests. Meanwhile, the variety of computer/mobile/IoT/all other digital technologies rose too, as did the rise in the competency of the emulator. We fitted it to our KSN security cloud, taught it new programming languages, made it familiar with new browsers and other OS objects… all in order to help us automatically catch never-before-seen types of malware. No AI BS, just lots of working hard and working smart – what it takes to come up with real HuMachine innovations :).
Today, few competitors can boast such technology, and it’s no wonder: emulation is a very difficult task that requires many years of expertise, time-consuming integration into ‘frontline combat’ products, and constant development. However, many newcomers to the cybersecurity industry prefer to invest in blah-blah-blah marketing. In the short term, this approach can give a substantial push to business development, but you can’t fool users for a long time: eventually a major foul-up will occur, and that will be it – cover story blown. Put another way, if a cybersec company has its own emulator, you know the level of expertise and maturity of the developer are both impressive. And vice versa: no emulator = little expertise, little experience, and won’t be around for long.
But I digress…
So, though we’ve been forever improving our emulator, on the other side of the barricades the cyber-thugs have hardly been twiddling their thumbs. They’ve been actively protecting their business and cyberespionage operations, and that includes even attempting to protect themselves against our emulator.
The most advanced threat actors use a variety of anti-emulator tricks to recognize the ‘test tube’ environment, for example by launching an undocumented function, checking the authenticity of requests to change processor registers, analyzing error codes, searching for specific code in memory, using ‘logic bombs’ that put the emulator into an infinite loop, and so on. If the malware senses something suspicious, it brings malicious functions to a screeching halt and comes over all butter-wouldn’t-melt-in-its-mouth’.
Thing is, we’re well aware of these tactics and so stay ahead of them, forever fine-tuning the emulator against these tricks and also improving it in other ways (primarily, reducing resource intensity). For example, to speed it up we use different limiters, optimizers, and configuration profiles, which can even completely disable the emulator in certain conditions when the delay is as bad as the BSoD.
Meanwhile, the other day our patent warriors brought us good news from the emulation front: we received a patent (US10275597) for a program-code emulator that can interpret unknown objects! As far as I know there’s no such feature in any competing product: to protect against malware’s anti-emulator tricks, competitors have to rework their whole emulator, which, of course, is not a quick process. We, on the other hand, have taught our emulator to update itself on the fly from a local database! So yes, it’s a very useful feature, and there’s no reason not to tell you about it, because knowledge of how we protect you is power! :)
Now, some files are not distributed in machine code, but directly in source code. To execute them on a computer an interpreter is required (for example, JavaScript or VBA), which translates this code in real-time into machine-friendly language. And – you guessed it – malware also often resides in such files.
To detect unknown threats of this type, many years ago we created a program-code emulator that checks files ‘in a test tube’ before they are executed. However, emulating the entire interpreter is too resource-intensive: the delay in processing web pages with scripts would make for many a frustrated internet user. Therefore, emulators usually recreate a compromise version of the virtual space, which is acceptable both in terms of performance and quality of protection. But what happens when the emulator encounters an unknown object, method, or function in the code, the interpretation of which is absolutely crucial to performing full-fledged analysis of the file?
We solved this problem another way – with the help of a ‘smart’ interpreter that’s able to quickly learn how to emulate such objects. During an update via the KSN cloud, the product receives auxiliary code in the language of the object being analyzed (JavaScript, VBA, VB Script, AutoIt…) and, ready with the new knowledge, returns to checking the file. In difficult cases, when the auxiliary code has yet to come through, the task is automatically transmitted to our analysts, who develop that code and promptly add it to the database.
As a result, users have at their disposal not only strong but also super-speedy technology that’s able to quickly respond to cyberthreats – without waiting for the re-release of the entire emulator. Bingo!
* ‘Antivirus’ is another archaism of the era of computer viruses. Modern antiviruses protect not only against viruses, but against all kinds of malware. They also contain a great many other useful security functions: for example, a password manager, VPN, parental control, backup, and much more. So, to be more accurate, today a good ‘antivirus’ should really be called ‘anti-this, that and everything; protecting me, the family, all our devices, all our data – and with all the bells and whistles on it too!’ Hmm. Doesn’t quite roll off the tongue, does it?
 products
products

 Tips
Tips