The ‘It wasn’t me’ phrase is not going to fly for users of the Ashley Madison dating site as the personal records of 37 million users have been stolen. Hackers threaten to release the entire database of the site if owners do not shut down two of their hookup sites.
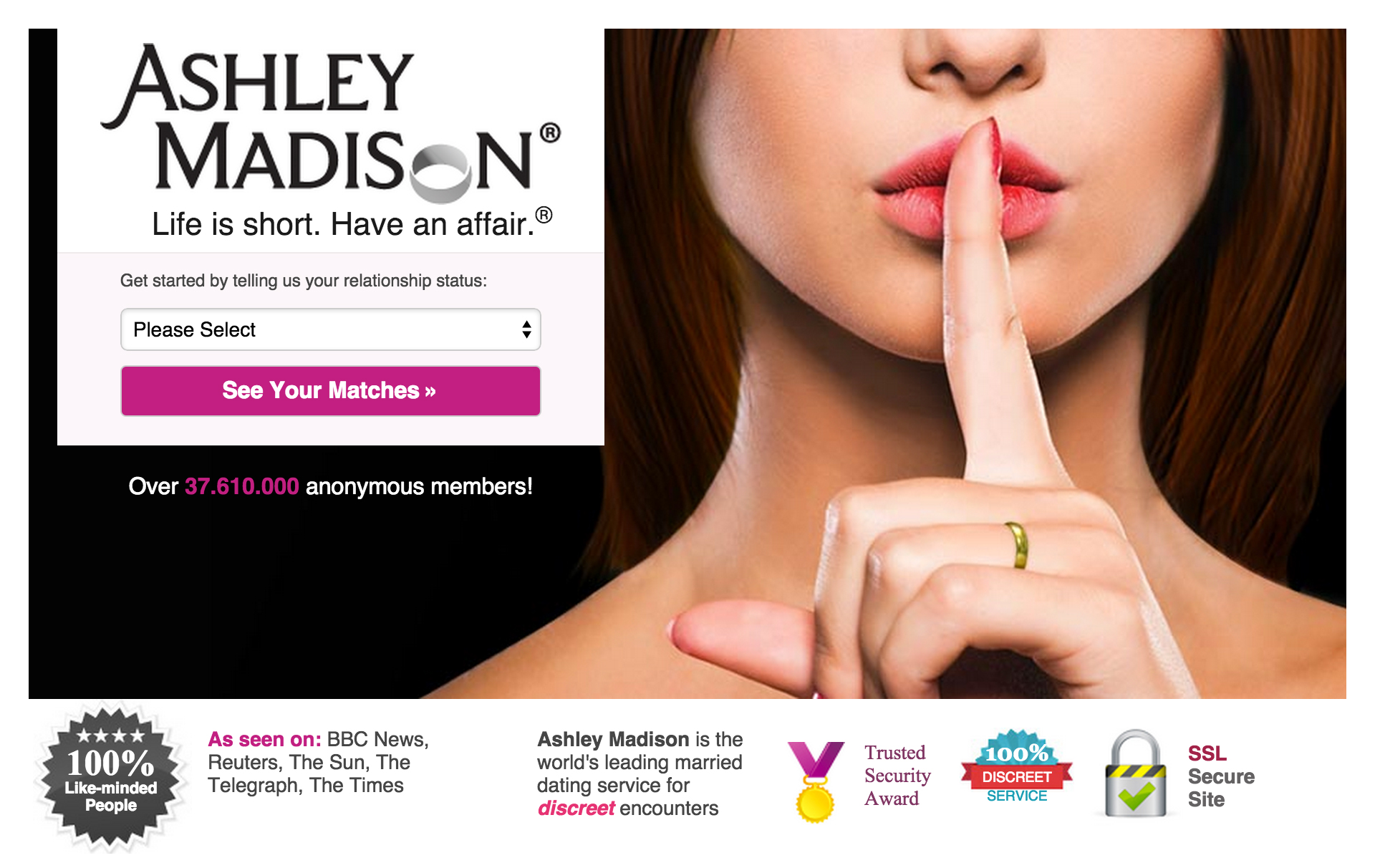
The popular dating site ‘Ashley Madison’ with the provocative slogan “Life is short. Have an affair” and the ‘Established Men’ website that sets up rich men with women — both belong to the Avid Life Media company. Hackers claim to punish ALM’s unfair practices: the company reportedly asks its customers to pay a $19 fee for completely erasing their profiles but actually does not wipe clients’ data as promised.
The attackers said: “Users almost always pay with credit card; their purchase details are not removed as promised, and include real name and address, which is of course the most important information the users want removed.”
The #cheating website in an involuntary affair with #hackers. #security #privacy
Tweet
Advocating justice, hackers demand ALM to permanently take both websites offline in all forms. Otherwise real customers names and addresses together with information about their secret sexual fantasies will be published online.
Hackers graciously permit the company to keep the other sites online (the only other site that belongs to ALM is the Cougar Life that connects older women with younger men). The company responds by charging attackers for committing a criminal act.
#TDSBreakingNews Cheating website Ashley Madison hacked. Back to cheating the old-fashioned way: with wife's sister.
— The Daily Show (@TheDailyShow) July 20, 2015
KrebsOnSecurity reports that samples of stolen data had been already published on the web to prove the hack, but ALM managed to remove published data shortly after the incident. The company confirmed the breach and stated that it engaged ‘leading forensics experts and other security professionals to determine the origin, nature, and scope of this incident’.
It’s quite possible that an individual with the inside access to the company’s network is involved — a former employee or a contractor. An indirect proof for this theory lies in the apology note that the attacker addresses to the ALM director of security: “Our one apology is to Mark Steele. You did everything you could, but nothing you could have done could have stopped this”.
Dating site, Match are putting user data at risk with non-HTTPS login. Via @arstechnica – http://t.co/8ojiCWsxbL pic.twitter.com/3gmkxE7w83
— Kaspersky (@kaspersky) April 21, 2015
For ALM huge revenue is at stake: according to the hackers, the profile removal service alone brought the company about $1.7 million in 2014. The whole Ashley Madison project is rated about $1 billion.
Currently ALM doesn’t seem to be ready to follow hackers’ demands and close their business. On the other hand, the privacy of 37 million of cheaters is thrown into the mix. If you put morality issues and possible family problems aside, the data can be used by other cybercriminals for phishing attempts or banking fraud.
It’s not clear who is the first to blame: ALM that promised security to its users or the users themselves. A recent Electronic Frontier Foundation report shows that dating sites are very dangerous from security/privacy point of view. Just a couple of months earlier another dating site was hacked and more than 3.5 million people’s sexual preferences, fetishes and secrets have been exposed.
6 heartbreaking #privacy and #security flops on major online dating sites – and what you can do about it. https://t.co/jrY3xXw8
— EFF (@EFF) February 10, 2012
When you’re paying with a credit card for intimate goods and services, you share your sensitive information with the seller — and with every hacker who will be bold enough to hack the seller’s system. Once the data is released online there is no way to take it down.
That’s why it’s vital to think about basic security:
– use encrypted communication channels;
– pay in cash if you don’t want your data to be recorded and used by unfair sellers;
– use a different email account and a nickname for dating websites.
Dating in the digital age & staying safe online. http://t.co/FVE0ylNElM #onlinedating #onlinesecurity pic.twitter.com/PdNZZMIzuS
— Kaspersky (@kaspersky) February 21, 2015
ALM claims that it’s close to identifying the hackers responsible. Unfortunately, it’s unclear if they finish the investigation in time to save privacy of millions of their users.
 dating sites
dating sites