
Google forcing Android System SafetyCore on users to scan for nudes
We dive into the mechanics of the controversial nude-scanning app that has mysteriously materialized on a billion phones.
747 articles

We dive into the mechanics of the controversial nude-scanning app that has mysteriously materialized on a billion phones.

Online converters are a tempting but dangerous way to change file formats. We tell you how to convert files and not get trojanized.

Everything you wanted to know about meme cryptocurrencies — such as TRUMP and DOGE — and ways to win or lose big.

Scareware is malware that scares users into doing something risky. Here’s how it works.
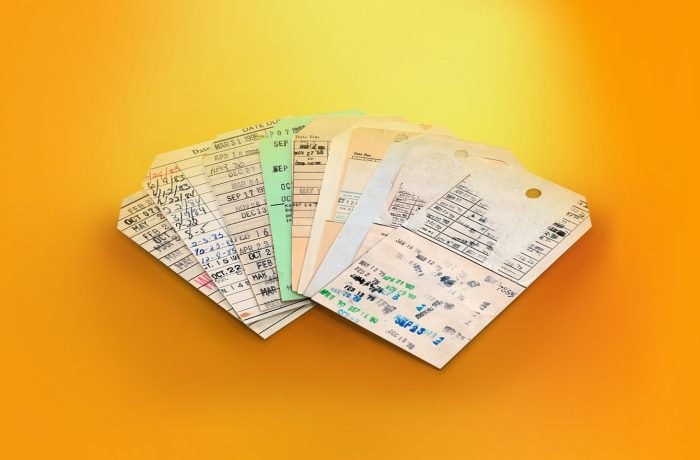
Every file, video, etc. we share contains a lot of hidden additional information — metadata. What’s it for, and is it really necessary?

How to avoid giving away your password to scammers when logging in to third-party sites or viewing “encrypted” or “confidential” documents.

Mistakes to learn from in 2024 – and resolutions for a safer 2025.

The best privacy-focused services that make practical gifts for friends and family.

We explain how to detect if scammers have gained access to your Telegram account, and what to do about it.

Is a taped-over webcam or phonecam a sign of paranoia – or smart thinking?

Scammers posing as buyers snatch one-time codes during online product demos.

Cybercriminals are enticing Telegram users with free subscriptions. Is this an unexpected act of generosity or just another scam?

Black Friday is a great opportunity for scammers to line their pockets — but not with your money if you follow our advice.

A step-by-step guide for those who may be tracked through stalker apps or wireless beacons.

Five dead simple tips to greatly improve your defenses against cybercriminals.

Web pages often disappear, move, or change content. How to keep them the way you want, or easily locate a web archive?

A detailed guide to configuring privacy settings in the ASICS Runkeeper running app.

Many of us have dozens of online subscriptions and recurring payments. How to take control, save money, and stay on top of expenses?

A detailed guide on setting up privacy in the adidas Running app.

Many popular online services these days require a selfie with your ID card or passport to register. We explore whether taking such photos is safe (spoiler: it’s not) and how to minimize the risks.