Perhaps the biggest problem with cybercriminals is that they are extremely difficult to catch. Think of a real-life bank robbery with guns and face-masks — the thieves leave fingerprints; their voices are recorded by security cameras; police can trace their cars using traffic cameras; and so on. All of that helps the investigators find the suspects. But when cybercriminals pull off a robbery, they leave … basically nothing. No clues.
Yet sometimes they get caught. Remember the SpyEye banking trojan? Its creators were caught in 2011. Remember the Carberp group, which was active from 2010 to 2012? Caught as well. How about the infamous Angler exploit kit, which suddenly went off the radar in late June? Lurk malware stopped its attacks around the same time — because the group behind it got caught, with the help of Russian authorities and Kaspersky Lab.
The story began back in 2011, when we first encountered Lurk. What caught our eye was the fact that some nameless Trojan that used remote banking software to steal money was classified by our internal malware naming system as a Trojan that could be used for many things — but not stealing money. So we took a closer look.
The investigation yielded almost no results — the Trojan seemed to do nothing. But the attacks continued, and our analysts were able to get more and more samples to look at.
During that time, we learned a lot about Lurk. For example, it had a modular structure: When the Trojan detected that it had infected a computer with remote banking software installed, it would download the malicious payload, which was responsible for stealing money. That is why our naming system didn’t call Lurk a banking Trojan at first — the payload was missing.
A technical look at #Lurk #banking #Trojan https://t.co/rNsJ0YHimW pic.twitter.com/vT7YLXZOae
— Kaspersky (@kaspersky) June 10, 2016
We also found that Lurk avoided leaving any footprints on the hard drive, working only in the RAM of the computers it had infected. That made it harder to catch. Lurk’s creators were also using encryption here and there as well as obfuscation. Their command-and-control servers were hosted on domains that were registered with false registration data. And the software — both Lurk’s body and the malicious payloads — were constantly changing, being tailored specifically for one bank or another.
Lurk’s creators were careful, and we knew there must be a team of professionals behind such complex malware. But professionals are still just people, and people make mistakes. Those mistakes gave us information we could use to find the people behind the Trojan.
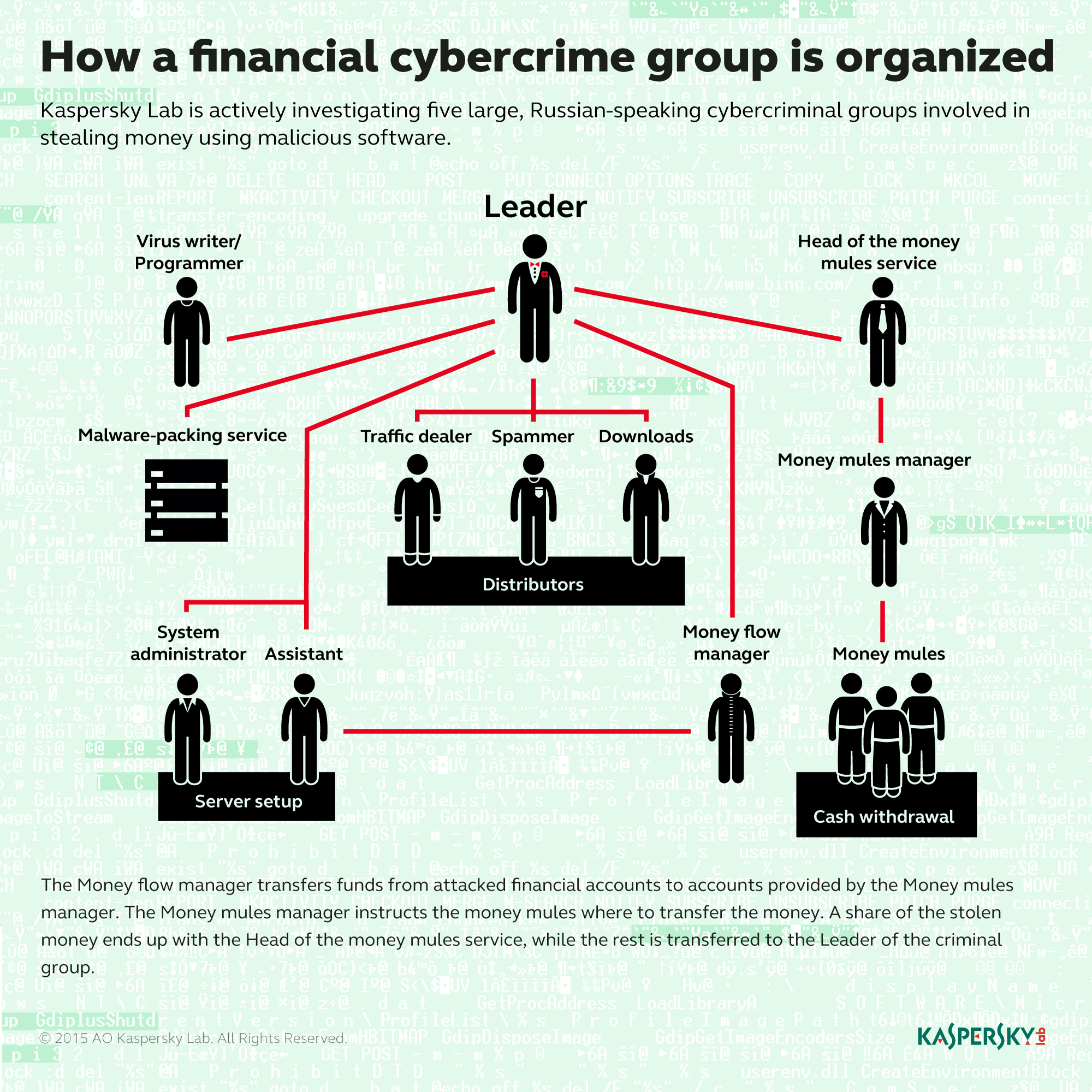
Lurk, it turned out, was created and maintained by a group of about 15 people, although by the time it was shut down, that number had risen to 40. They had two projects: the malware itself and the botnet used for its distribution. Each project had its own team.
A group of programmers developed Lurk, and a group of testers checked how it performed in various environments. On the botnet side, there were administrators, operators, a money flow manager, and other people. Money mules picked up cash at ATMs, and a money mule manager collected that money from the mules.
Most of the people involved were basically wage workers on a salary. To hire them, the people behind Lurk posted job vacancies on head-hunting websites, promising remote work with full employment and an attractive salary. During the job interview, the recruiter would ask the candidates whether they had strong moral principles. Those who didn’t got the job.
Developing Lurk and maintaining the botnet required not only a lot of people, but also some costly infrastructure including servers, VPNs, and other tools. After a few years in business, the Lurk team looked like a medium-size IT company. And like many companies, they decided to diversify their business after a while.
The cybercriminals behind Lurk are also responsible for creating Angler, aka XXX — one of the most sophisticated exploit kits to date. At first it was designed as a tool to deliver Lurk to its victims, but its creators decided to sell Angler to third parties as well. Its success and apparent invincibility boosted the group behind Lurk to almost legendary status among Russian cybercriminals, and that in turn gave a good boost to Angler sales on underground markets.
Angler became quite popular among cybercriminals. For example, it was used to distribute CryptXXX and Teslacrypt ransomware.
#Nuclear, #Angler exploit kit activity has disappeared via @threatpost https://t.co/XHxKsObx03 pic.twitter.com/GPjzpJDVvS
— Kaspersky (@kaspersky) June 23, 2016
But by the time they started to sell Angler, the group’s days were already numbered. The Russian police, with Kaspersky Lab’s help, had collected enough evidence to arrest the suspected group members. In June 2016 Lurk activity stopped, and soon Angler followed suit. The cybercriminals thought to the end that they would never get caught because of the precautions they took.
Their precautions shielded them for a while, but even clever cybercriminals are still human. Sooner or later they’ll stumble and make some mistakes, and then a good team of investigators will find them. It usually takes a long time and a lot of effort, but that’s how we bring justice to the cyberworld.
 Angler
Angler

 Tips
Tips