Smartphones became an integral part of our lives so quickly that many people still haven’t realized which threats came along with these smart pocketable helpers. The list is long: malicious programs for smartphone are able to steal money. If your device is stolen, thousands of photos, private messages and social network credentials fall into the wrong hands. It’s easy to constantly monitor a person using his/her smartphone as a beacon, and corporations face a huge risk of data leakage. Luckily for all of us, these risks are obvious beyond those individuals in the security industry. For example, Google developers take these risks very seriously and the upcoming release of the Android codenamed L will greatly improve the security landscape for this OS, which leads today in terms of mobile threats presence.
Steal it if you can
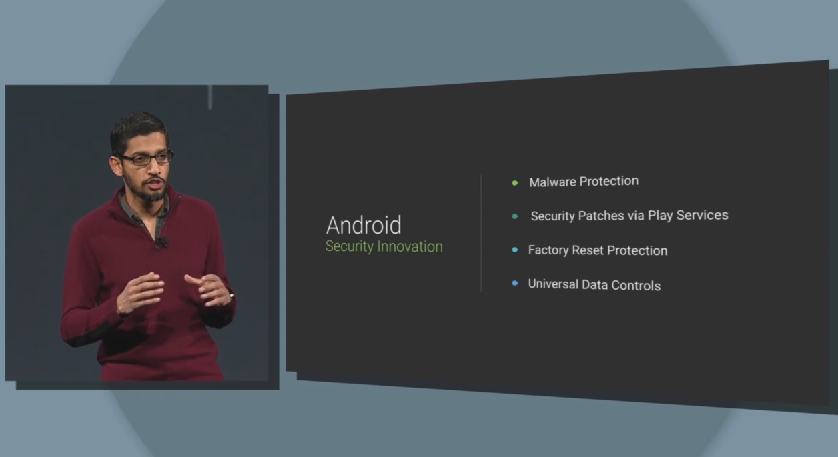
Thieves love smartphones, because it’s easy to steal one and then sell it for a relatively substantial sum of money. To quickly get rid of dangerous evidence, thieves perform a factory reset after a smartphone theft. This trick will be harder to perform with the new Android L-based devices, as the factory reset will require a legitimate owner’s password, otherwise the smartphone will remain a useless brick.
Pichai says that with Android L Google is strengthening security. If your phone is stolen, you can now factory reset it remotely. #io14
— The Times Of India (@timesofindia) June 25, 2014
Patch it quickly
As soon as Android became popular, it was criticized for its very slow and unreliable security patching. Any discovered security issue should be fixed in thousands of firmware variations from multiple vendors and carriers for each specific smartphone model, a large undertaking. No wonder that many critical issues were left unfixed for years (!). Google will try to remediate this problem by delivering most security updates directly to end users via its own Google Play services and applying those updates without a complete firmware update. However, this feature will not be applicable to every Android smartphone and some issues can’t be resolved this way. But it’s better than nothing.
Keep the work-life balance
Many companies don’t allow Android smartphones for business purposes because of data leakage fears. These fears are legitimate, as Android malware is able to steal company information from a smartphone. The new Android for Work solution (which incorporates Samsung KNOX features) will address these issues by creating an encrypted storage and a virtual environment, basically, a smartphone inside a smartphone. After launching Android for Work, a user will see a “business home screen” with company-approved apps and can perform his/her duties using encrypted data and an encrypted Internet connection. One click ― and his/her personal home screen and apps are back. Private and work-related apps and data are fully isolated, e.g. the company email app cannot read users’ personal address book or photo library, and vice versa.
Android for Work helps to isolate personal and corporate data on the same smartphone.
Tweet
In addition to security improvements, this approach could potentially improve an employee’s work-life balance. Launching Android for Work requires extra actions, including password entry, thus making it less tempting to read emails on Sunday.
A convenient protection
In general, passwords are boring and obtrusive, but smartphones make it even more evident, as you have to unlock a smartphone every 5 minutes or so. Google aims to reduce this routine, identifying a legitimate owner by other means, if it’s possible. For example, a lock screen could be disabled, if an owner’s smart watch is nearby, indicating that owner himself is close as well. Also, a user may define a “zone of trust”, e.g. home. Lockscreen is also disabled in such zones. Of course, every convenient workaround somewhat reduces the level of security, so every user must find his personal tradeoff between convenience and security.
More privacy
Google developers briefly mentioned something called Universal Data Controls, a centralized tool helping a user identify items like which apps, what kind of his/her personal data and what should be blocked for an individual’s smartphone. Unfortunately, there are few details on the subject. We will have to wait until September to take a closer look at this function.
 Android
Android

 Tips
Tips