Beta Bot is a Trojan that infects computers and attempts to prevent users from accessing security websites while also disabling their antivirus and malware scan software.
How Beta Bots Work?
This Trojan infects computers and attempts to prevent users from accessing security websites while also disabling their antivirus and malware scan software. To accomplish this, the bot:
- Creates a fake Microsoft Windows message box with the heading "User Account Control."
- It asks users to allow the "Windows Command Processor" to make administrator-level changes, and claims it is verified by Microsoft.
- If changes are approved, Beta Bot modifies a user's computer to steal log-in credentials and financial data while also disabling security software access.
Common Beta Bot Locations and Risk Factors
Here’s how beta Bot are transmitted to a computer:
- False links from services such as Skype or in emails that ask users to download a ""video player"" or similarly benign-sounding software.
- USB drives are also used to carry the program.
In addition to the User Account Control (UAC) pop-up described above, this Trojan attempts to frighten users into accepting its request by creating a false ""Critical Disk Error"" warning. As a result, even cautious users may approve the false UAC request.
How to Remove Beta Bot
Removing Beta Bot can be difficult, since local malware scans will be disabled and security website access blocked.
According to the FBI, here’s how to disable and remove a Beta Bot:
- Download a full antivirus suite or antivirus updates onto a clean computer.
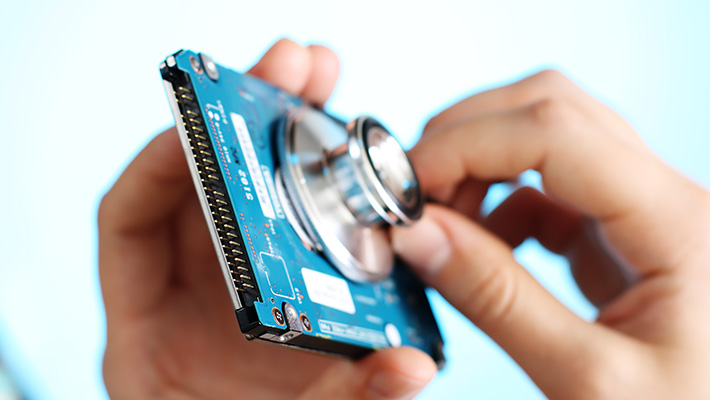
- Transfer the needed files to a USB drive.
- Run the antivirus program on their infected computer.
- After, users should also reformat the USB drive to prevent accidental infection.
To avoid this bot, users should never click on unknown links or open any software downloads without first performing a virus scan. In addition, users should deny any UAC request unless they are making modifications to their own system.
Other articles and links related to Definitions
Recommended products:

